Introduction
You can connect to your Azure DevOps data in Microsoft Fabric using the high-performance Azure DevOps ODBC Driver (powered by Azure DevOps Connector). We'll walk you through the entire setup.
Let's not waste time and get started!
Create data source using Azure DevOps ODBC Driver
Video instructions
Watch this quick walkthrough to see how to configure your Azure DevOps ODBC data source, or scroll down for the step-by-step written guide.
Step-by-step instructions
To get data from Azure DevOps using Microsoft Fabric, we first need to create an ODBC data source. We will later read this data in Microsoft Fabric. Perform these steps:
-
Download and install ODBC PowerPack (if you haven't already).
-
Search for
odbcand open the ODBC Data Sources (64-bit):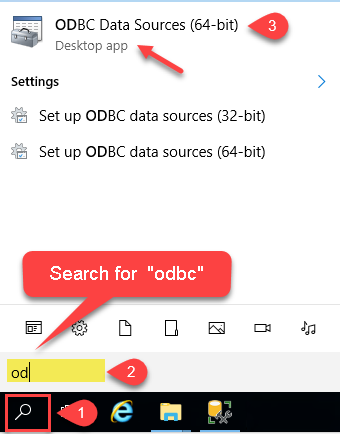
-
Create a User data source (User DSN) based on the ZappySys API Driver driver:
ZappySys API Driver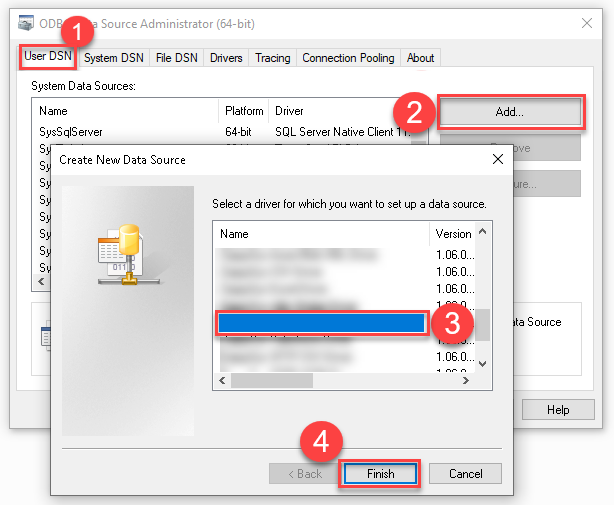
- Create and use a User DSN if the client application runs under a User Account. This is the ideal option at design time (e.g., when developing in Visual Studio). Use it for both types of applications (64-bit and 32-bit).
- Create and use a System DSN if the client application runs under a System Account (e.g., as a Windows Service). This is usually the required option in a production environment. If your Windows Service is a 32-bit application, you must use the 32-bit ODBC Data Source Administrator to configure this
-
When the Configuration window appears give your data source a name if you haven't done that already, then select "Azure DevOps" from the list of Popular Connectors. If "Azure DevOps" is not present in the list, then click "Search Online" and download it. Then set the path to the location where you downloaded it. Finally, click Continue >> to proceed with configuring the DSN:
AzureDevopsDSNAzure DevOps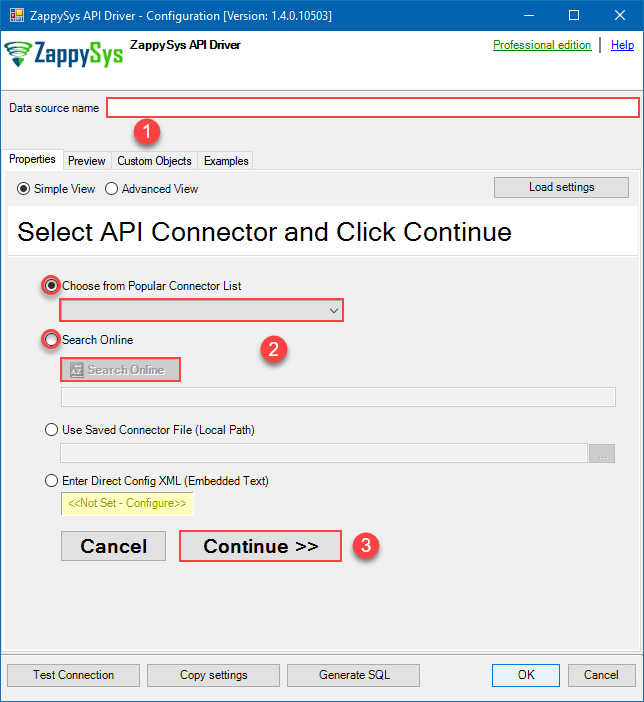
-
Select your authentication scenario below to expand connection configuration steps to:
- Configure the authentication in Azure DevOps.
- Enter those details into the ZappySys API Driver data source configuration.
User Credentials
Azure DevOps authentication
Delegated access using OAuth authorization code flow. Users sign in with their Azure AD account. [API reference]
Follow these simple steps below to create Microsoft Entra ID application with delegated access:
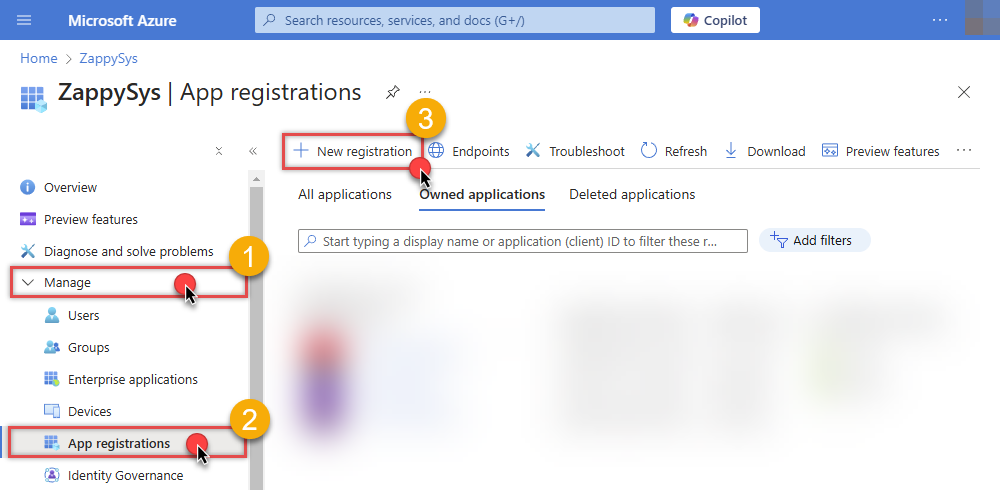
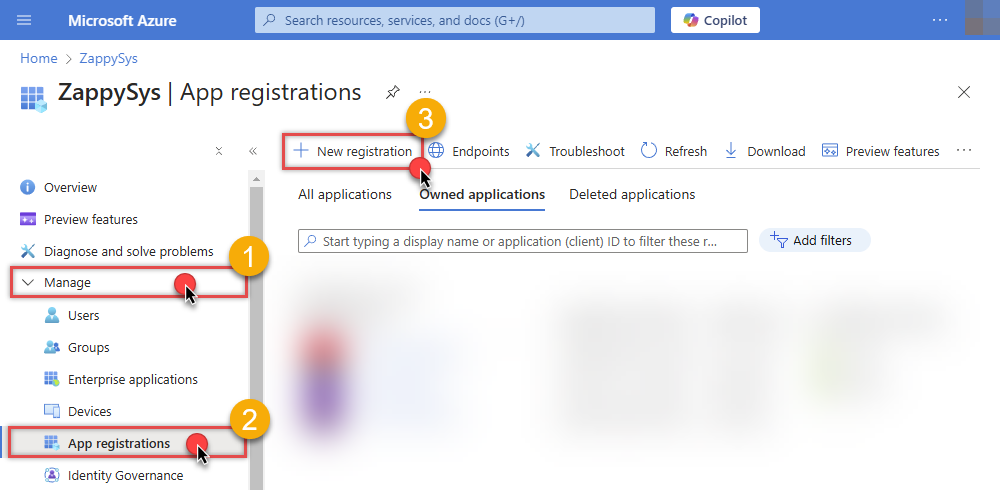
WARNING: To automate your company's processes, make sure you use a system/generic account (e.g.automation@my-company.com). When you use a personal account which is tied to a specific employee profile and that employee leaves the company, the token may become invalid and any automated processes using that token will start to fail.- Navigate to the Azure Portal and log in using your credentials.
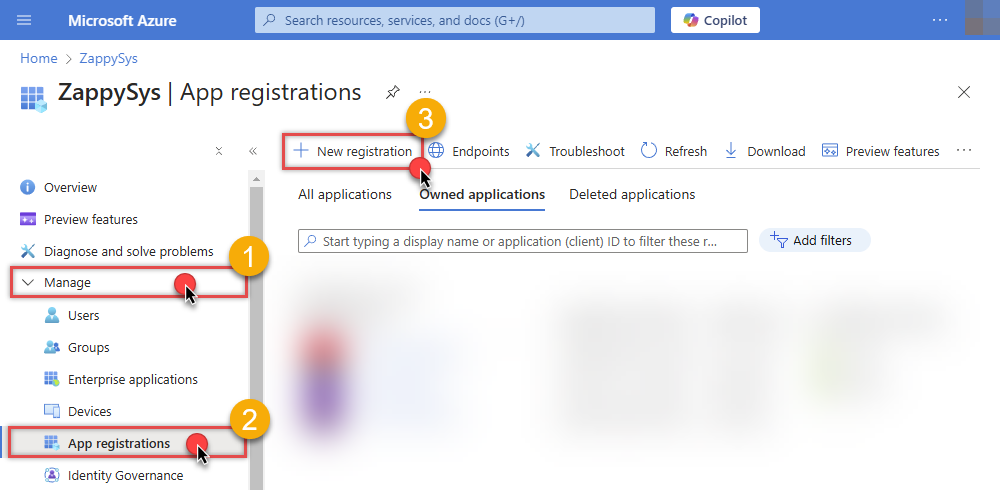
- Access Microsoft Entra ID.
-
Register a new application by going to
App registrations
and clicking on New registration button:
 INFO: Find more information on how to register an application in Graph API reference.
INFO: Find more information on how to register an application in Graph API reference. -
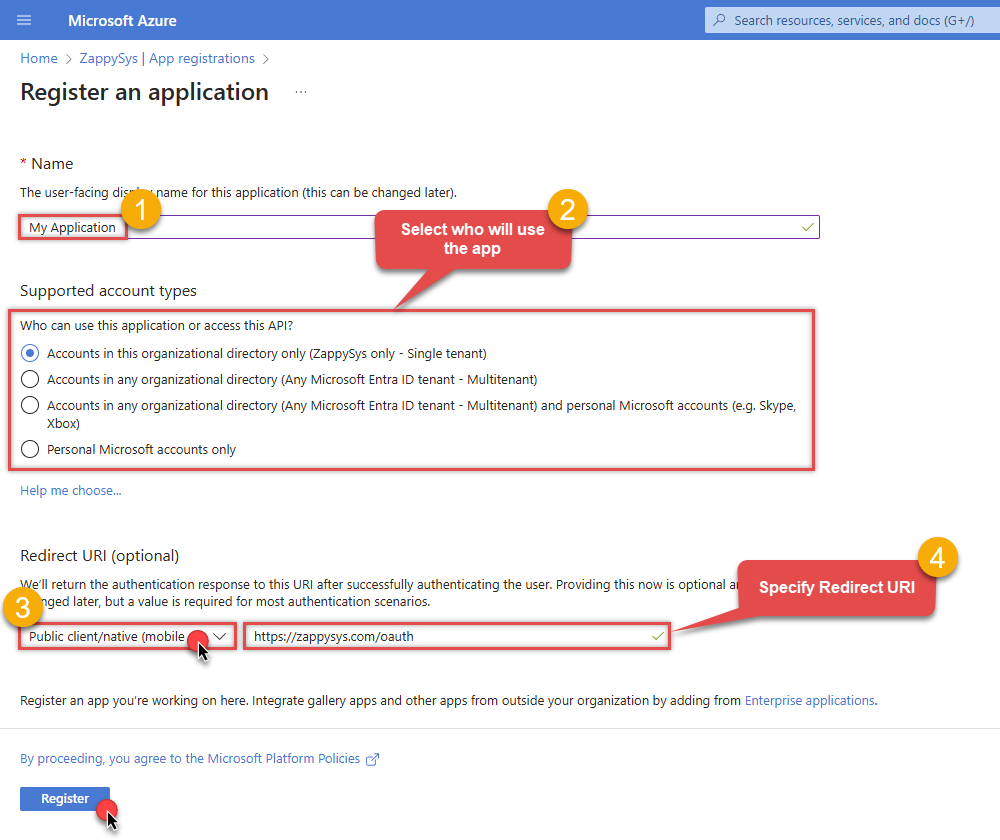
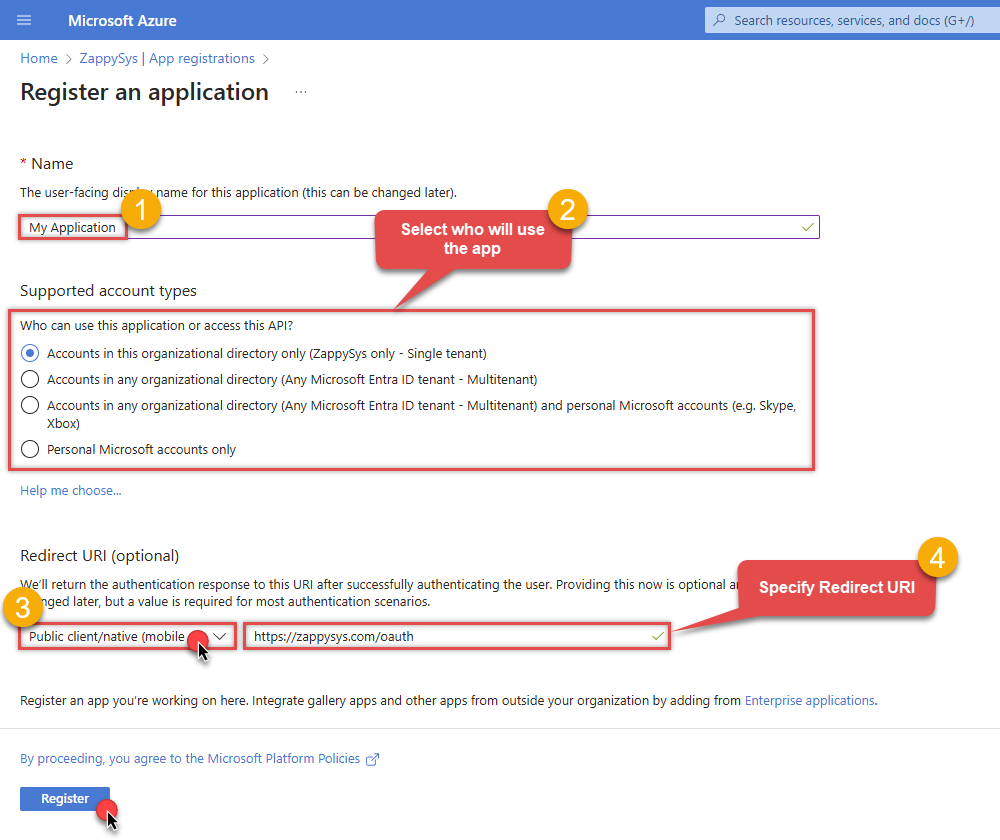
When configuration window opens, configure these fields:
-
Supported account type
- Use
Accounts in this organizational directory only, if you need access to data in your organization only.
- Use
-
Supported account type
-
Redirect URI:
- Set the type to
Public client/native (mobile & desktop). - Use
https://zappysys.com/oauthas the URL.
- Set the type to
-
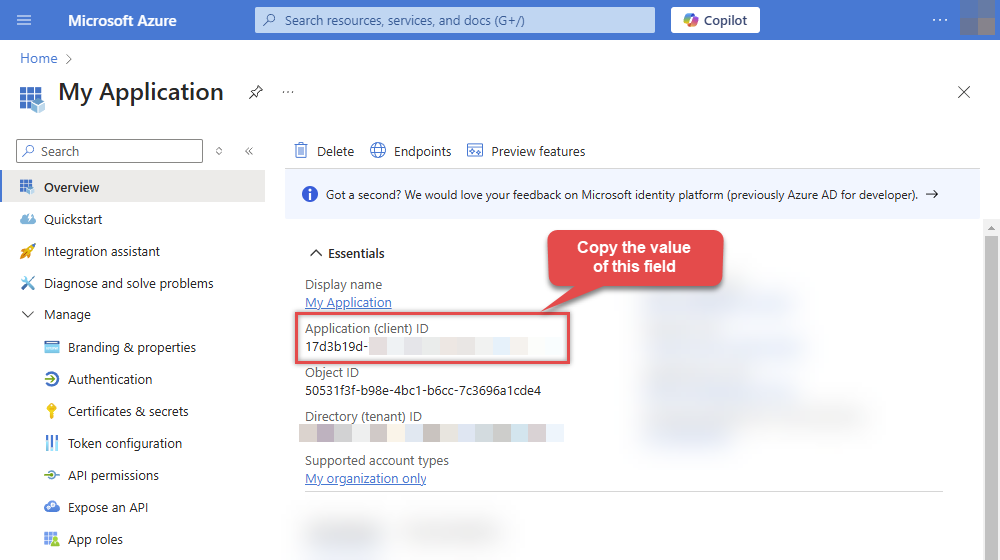
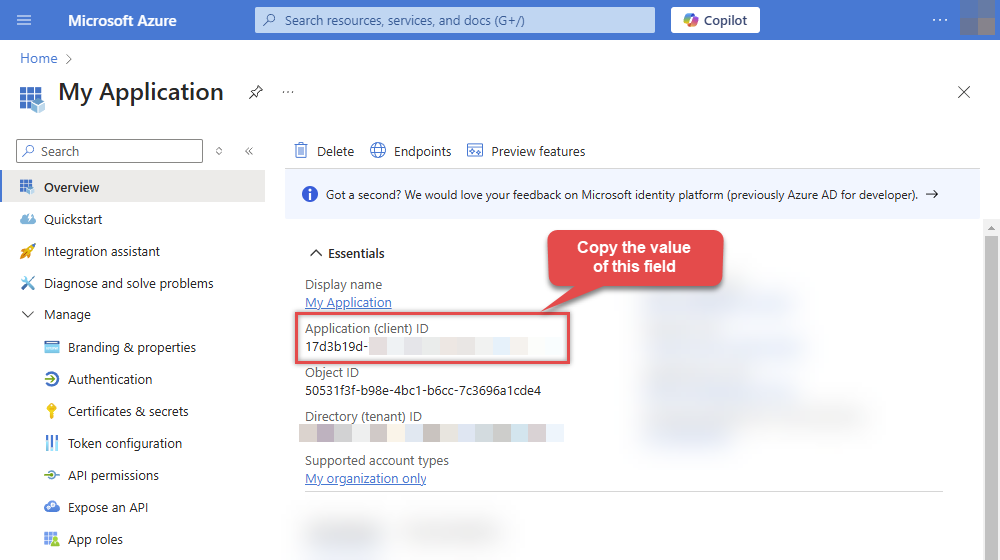
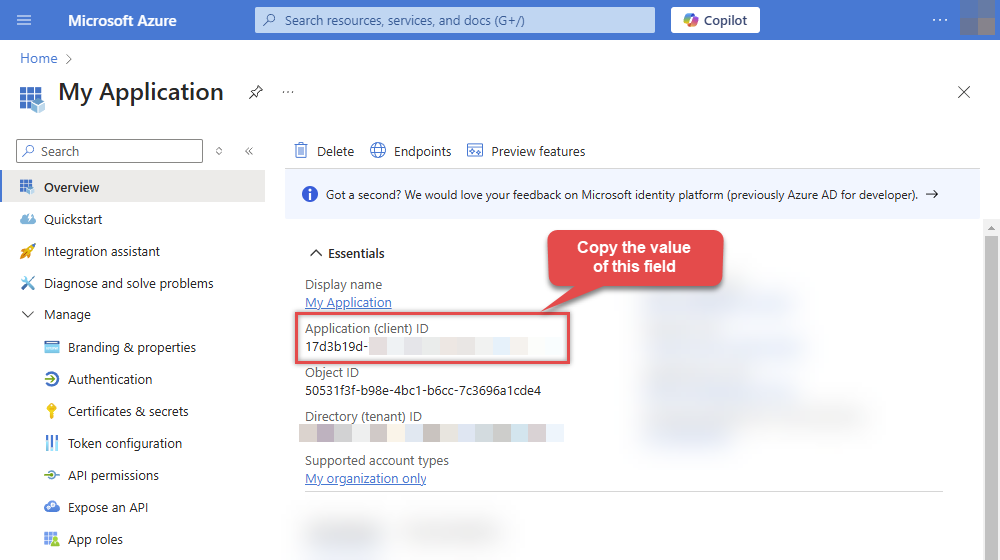
After registering the app, copy the Application (client) ID for later:
-
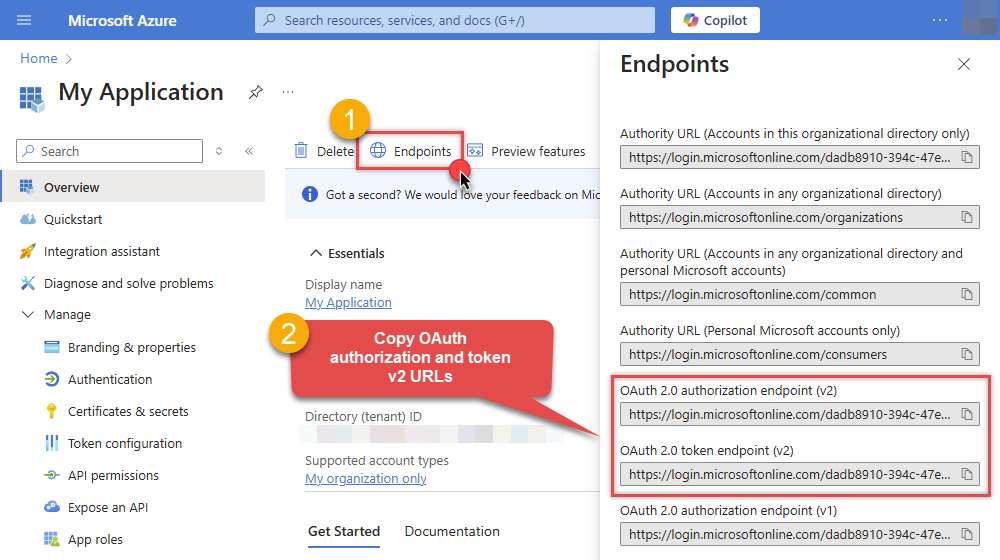
Then copy OAuth authorization endpoint (v2) & OAuth token endpoint (v2) URLs to use later in the configuration:
-
Now go to SSIS package or ODBC data source and use the copied values in User Credentials authentication configuration:
- In the Authorization URL field paste the OAuth authorization endpoint (v2) URL value you copied in the previous step.
- In the Token URL field paste the OAuth token endpoint (v2) URL value you copied in the previous step.
- In the Client ID field paste the Application (client) ID value you copied in the previous step.
-
In the Scope field use the default value or select individual scopes, e.g.:
-
vso.project -
vso.work_full
-
- Press Generate Token button to generate Access and Refresh Tokens.
- Optional step. Choose Default Drive Id from the drop down menu.
- Click Test Connection to confirm the connection is working.
- Done! Now you are ready to use the API Connector!
API Connection Manager configuration
Just perform these simple steps to finish authentication configuration:
-
Set Authentication Type to
User Credentials [OAuth] - Optional step. Modify API Base URL if needed (in most cases default will work).
- Fill in all the required parameters and set optional parameters if needed.
- Press Generate Token button to generate the tokens.
- Finally, hit OK button:
AzureDevopsDSNAzure DevOpsUser Credentials [OAuth]https://dev.azure.comRequired Parameters Authorization URL Fill-in the parameter... Token URL Fill-in the parameter... Client ID Fill-in the parameter... Organization name or Id (e.g. mycompany) Fill-in the parameter... Return URL Fill-in the parameter... Scopes (Must match with App Registration) Fill-in the parameter... API Version Fill-in the parameter... Optional Parameters Client Secret Refresh Token File Path Default Project Name (Choose after Generating Token) RetryMode RetryWhenStatusCodeMatch RetryStatusCodeList 429 RetryCountMax 5 RetryMultiplyWaitTime True 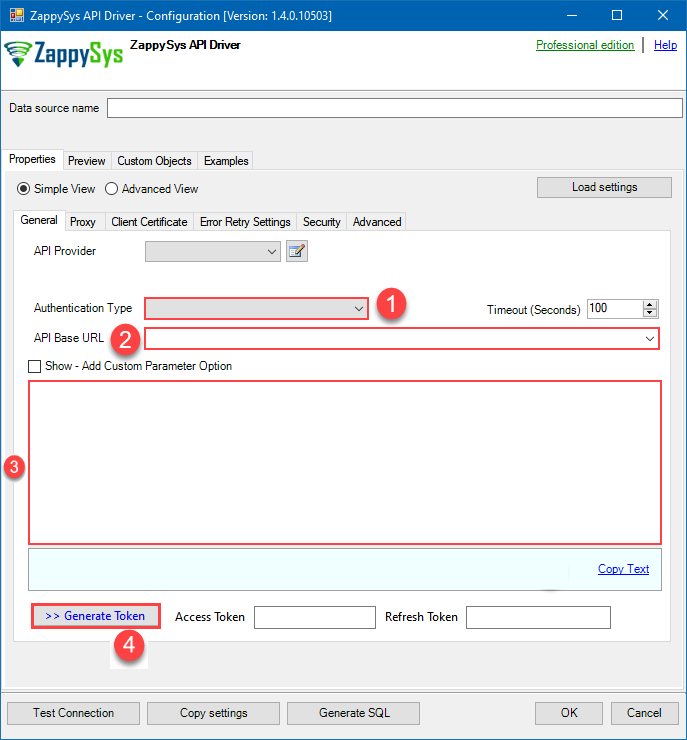 Find full details in the Azure DevOps Connector authentication reference.
Find full details in the Azure DevOps Connector authentication reference.Azure App Credentials
Azure DevOps authentication
Use Azure AD service principal credentials (client id + secret) with the client credentials flow. Recommended for automated server-to-server access instead of PAT or delegated OAuth. [API reference]
Step 1: Register the App in Microsoft Entra ID (AAD)
- Go to the Azure Portal > Microsoft Entra ID > App registrations and click New registration:
- Name it (e.g., ZS-AzureDevOps-AppCred).
- Set Supported account types to "Accounts in this organizational directory only" (Single Tenant):
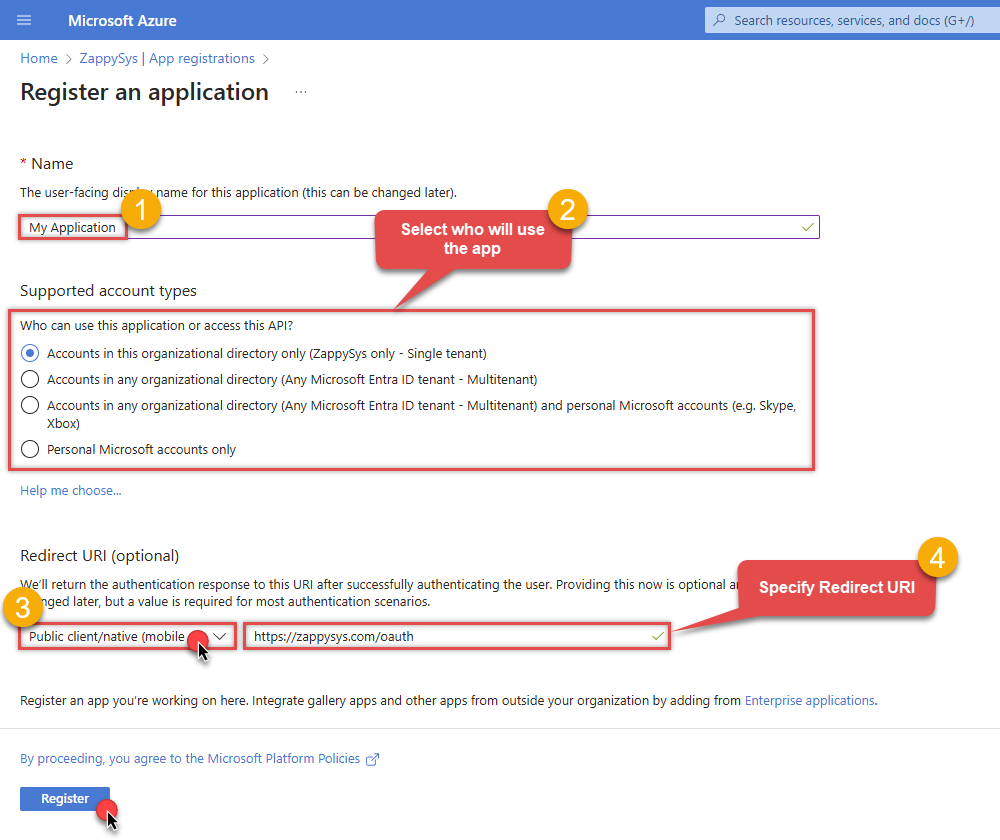
- Leave Redirect URI blank (it's not used for Client Credentials).
- Click Register.
Step 2: Create a Client Secret
- In your new app, go to Certificates & secrets.
- Click New client secret, give it a name, and set an expiration.
- Copy the Secret Value immediately. You will never see it again once you leave the page:
Step 3: Set Permissions and Admin Consent
- Go to API permissions > Add a permission.
- Select Azure DevOps and click Delegated permissions.
- Check the necessary scopes (e.g.,
vso.project,vso.work_full). - Crucial: Click Grant admin consent for [Your Tenant]. Without this, the app cannot authenticate in the background.
Step 4: Map the App to Azure DevOps Organization
- Copy your Application (client) ID from the App Overview page.
- Go to your Azure DevOps Organization Settings > Users.
- Click Add users, paste the Application (client) ID in the search box, and select the App.
- Assign an Access level (usually Basic) and add it to the relevant Projects.
Step 5: Connection Settings
In your SSIS package or ODBC data source, use the following in the App Credentials configuration:
- In the Token URL field, paste the OAuth token endpoint (v2) URL from the Azure Portal 'Endpoints' tab.
- In the Client ID field, paste the Application (client) ID.
- In the Client Secret field, paste the Secret Value copied in Step 2.
- In the Scope field, use:
https://app.vssps.visualstudio.com/.default
Step 6: Finalize Connection
- Press Generate Token button to fetch the token using the Client Secret.
- Click Test Connection to confirm the setup.
- Done! You are ready to use the API Connector!
API Connection Manager configuration
Just perform these simple steps to finish authentication configuration:
-
Set Authentication Type to
Azure App Credentials [OAuth] - Optional step. Modify API Base URL if needed (in most cases default will work).
- Fill in all the required parameters and set optional parameters if needed.
- Finally, hit OK button:
AzureDevopsDSNAzure DevOpsAzure App Credentials [OAuth]https://dev.azure.comRequired Parameters Token URL Fill-in the parameter... Client ID Fill-in the parameter... Client Secret Fill-in the parameter... Scopes (Use .default for App Credentials) Fill-in the parameter... Organization name or Id Fill-in the parameter... API Version Fill-in the parameter... Optional Parameters Default Project Name RetryMode RetryWhenStatusCodeMatch RetryStatusCodeList 429 RetryCountMax 5 RetryMultiplyWaitTime True 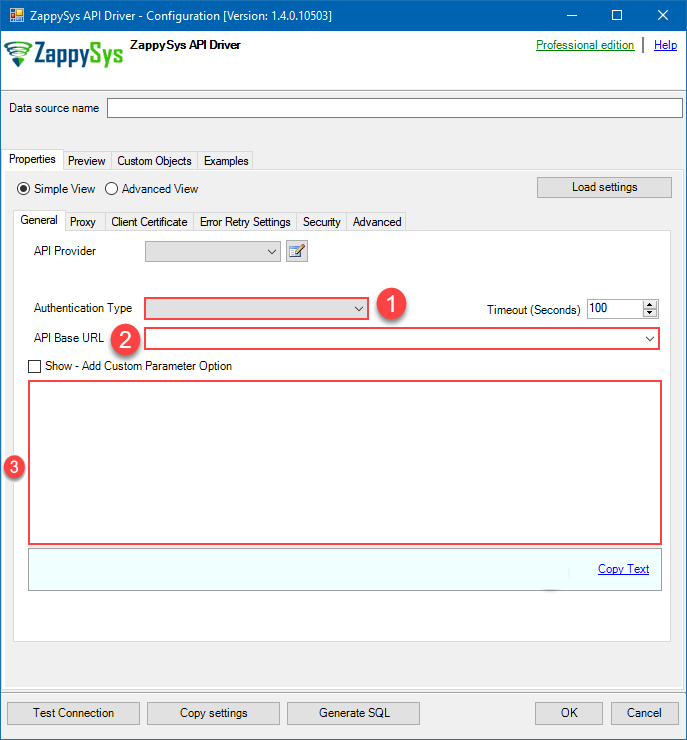 Find full details in the Azure DevOps Connector authentication reference.
Find full details in the Azure DevOps Connector authentication reference.Azure App Credentials with Certificate (Sign JWT with Private Key)
Azure DevOps authentication
Same as Application Credentials but uses a client certificate instead of a secret. [API reference]
Step 1: Register the App in Microsoft Entra ID (AAD)
- Go to the Azure Portal > Microsoft Entra ID > App registrations and click New registration:
- Name it (e.g., ZS-AzureDevOps-CertAuth).
- Set Supported account types to "Accounts in this organizational directory only" (Single Tenant):
- Leave Redirect URI blank (it's not used for Client Credentials flows).
- Click Register.
Step 2: Upload Client Certificate
- In your new app, go to Certificates & secrets.
- Click the Certificates tab, then click Upload certificate.
- Upload your public key certificate (.cer, .pem, or .crt). Keep the private key secure on your system.
- Copy the Thumbprint for your configuration:
Step 3: Set Permissions and Admin Consent
- Go to API permissions > Add a permission.
- Select Azure DevOps and click Delegated permissions.
- Select the required scopes (e.g.,
vso.project,vso.work_full). - Crucial: Click Grant admin consent for [Your Tenant]. Without this, the background service cannot acquire a token.
Step 4: Map the App to Azure DevOps Organization
- Copy your Application (client) ID from the App Overview page.
- Go to your Azure DevOps Organization Settings > Users.
- Click Add users and paste the Application (client) ID in the search box to find the App.
- Assign an Access level (usually Basic) and add it to the relevant Projects.
Step 5: Connection Settings
In your SSIS package or ODBC data source, use the following in the Client Certificate configuration:
- In the Token URL field, paste the OAuth token endpoint (v2) URL from the Azure Portal 'Endpoints' tab.
- In the Client ID field, paste the Application (client) ID.
- Configure your Certificate Path or Thumbprint in the Client Certificate tab of the connector.
- In the Scope field, use:
https://app.vssps.visualstudio.com/.default
Step 6: Finalize Connection
- Press Generate Token. The connector will sign the request using your certificate to fetch a token.
- Click Test Connection to confirm the setup.
- Done! Your certificate-based connection is ready!
API Connection Manager configuration
Just perform these simple steps to finish authentication configuration:
-
Set Authentication Type to
Azure App Credentials with Certificate (Sign JWT with Private Key) [OAuth] - Optional step. Modify API Base URL if needed (in most cases default will work).
- Fill in all the required parameters and set optional parameters if needed.
- Finally, hit OK button:
AzureDevopsDSNAzure DevOpsAzure App Credentials with Certificate (Sign JWT with Private Key) [OAuth]https://dev.azure.comRequired Parameters Token URL Fill-in the parameter... Client ID Fill-in the parameter... Certificate: *** Configure [Client Certificate] Tab *** Fill-in the parameter... Scopes (Must match with App Registration) Fill-in the parameter... Organization name or Id Fill-in the parameter... API Version Fill-in the parameter... Optional Parameters Default Project Name RetryMode RetryWhenStatusCodeMatch RetryStatusCodeList 429 RetryCountMax 5 RetryMultiplyWaitTime True 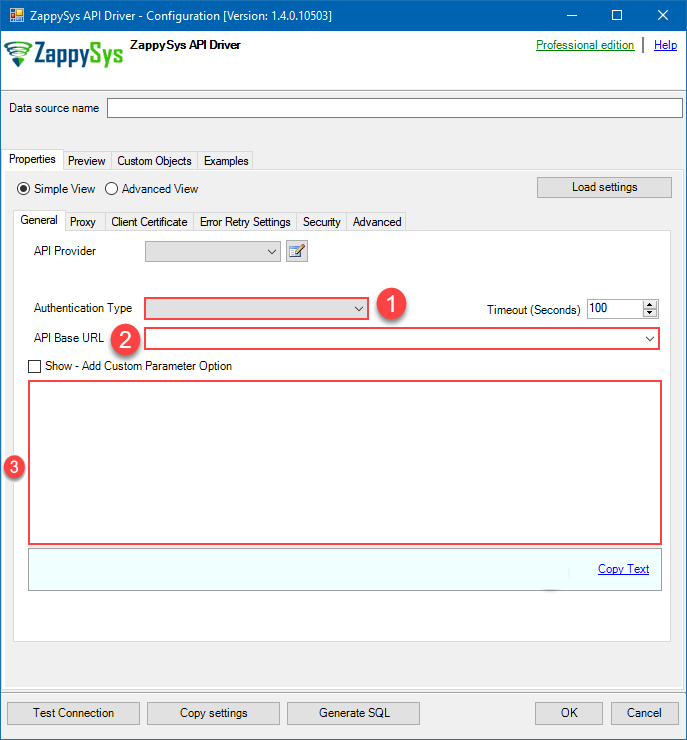 Find full details in the Azure DevOps Connector authentication reference.
Find full details in the Azure DevOps Connector authentication reference.(Cloud) OAuth App - User Credentials (DEPRECATED)
Azure DevOps authentication
**DEPRECATED:** this OAuth-based user credential flow is legacy; for new integrations prefer the Azure App Credentials options below. Connecting to your Azure DevOps data requires you to authenticate your REST API access. Follow the instructions below:- Go to https://app.vsaex.visualstudio.com/app/register to register your app.
-
Fill in your application and company's information as required, and then select the scopes that your application needs.
This should typically be Project and team (read and write) and Work items (read and write).
Your selected scopes when registering your app must match the scopes you enter here on the connector screen. If they don't match, the connector will not be able to work with your Azure DevOps account!If you need further information about the scopes used in Azure DevOps, or need to see what to enter into the connector screen to match up with your selected scopes, visit https://learn.microsoft.com/en-us/azure/devops/integrate/get-started/authentication/oauth?view=azure-devops.
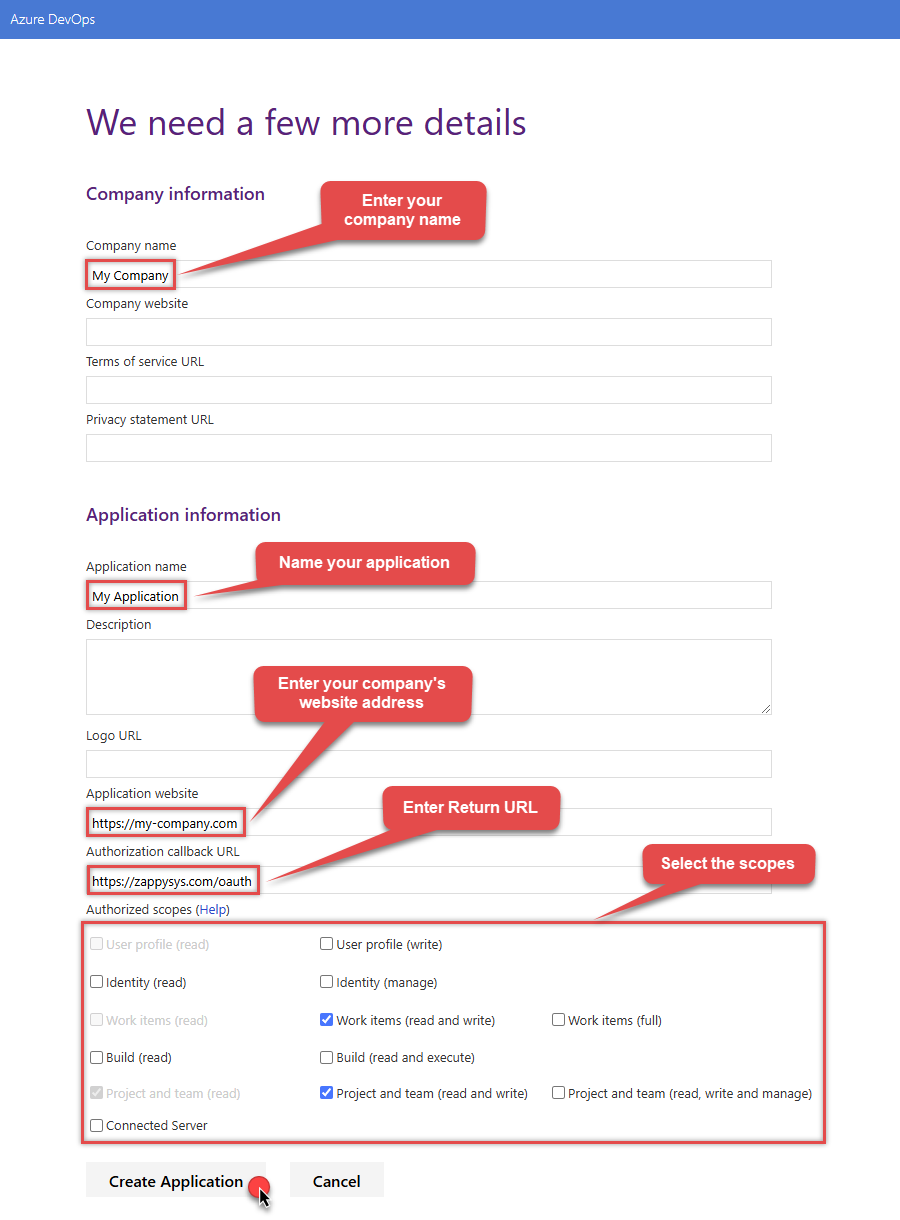
NOTE: For Authorization callback URL use your company's OAuth Redirect URL (if IT administrator provides you one) or you can use
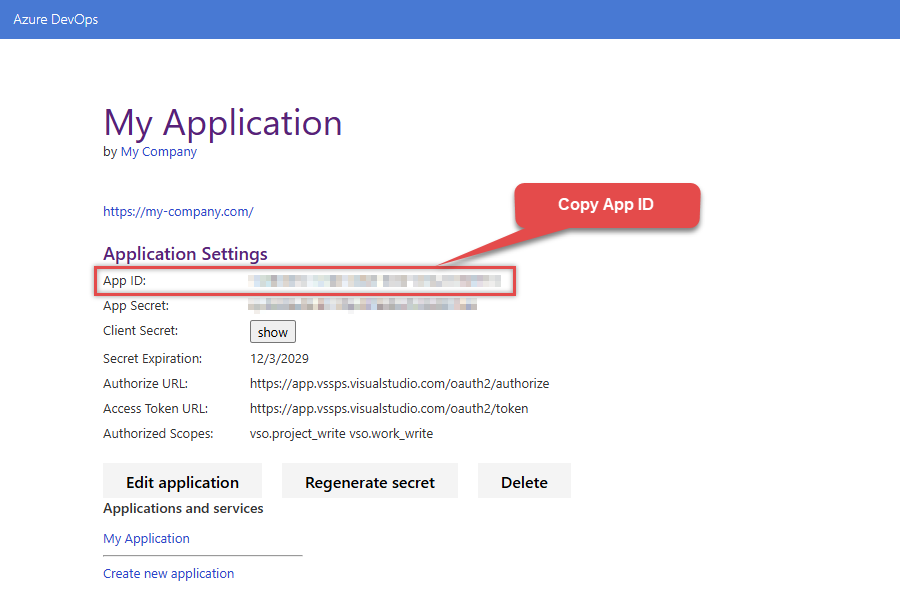
https://zappysys.com/oauth(it's safe). - Select Create Application and then the Application Settings page will be displayed.
-
Record the App ID for us to use later:
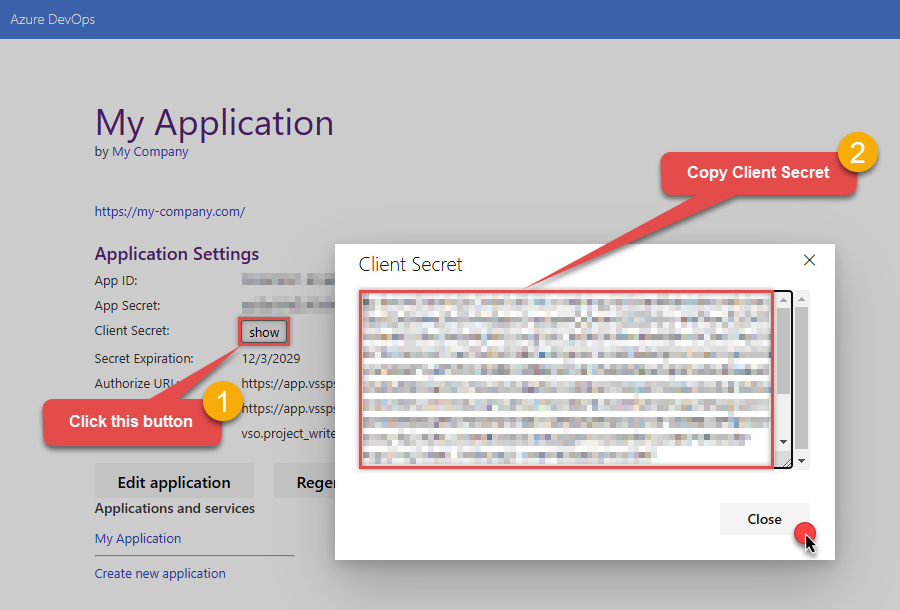
-
And do the same with Client Secret:
- Then go to https://aex.dev.azure.com and select relevant organization on the left.
-
Then copy Organization's host name part (e.g.
acmeinc, if full host name isacmeinc.visualstudio.com), save it to a file, and click it: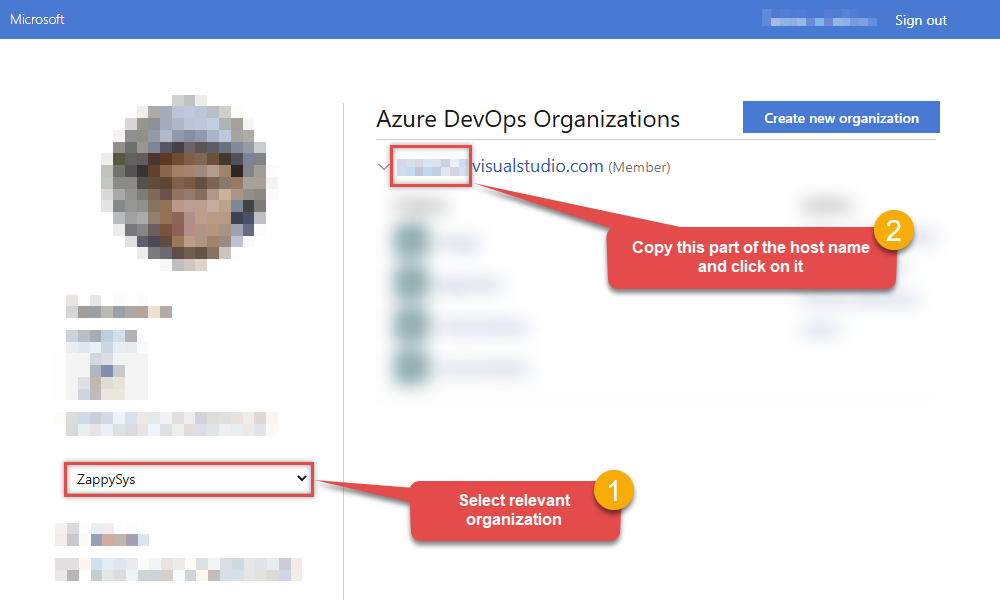
- Back at the connector screen, enter the App ID into the Client Id (App ID) field that was recorded in the previous step.
- Enter the Client Secret that was recorded in the previous step into the Client Secret field. In order to edit the text in this field, select the ellipses (...) button that appears when the textbox is clicked, and edit the Client Secret with the dialog box that appears.
- Enter the organization that was recorded in step 5 into the Organization name or Id for url field.
- Click Generate Token. If proper authentication occurs, you will see a notice saying so. You can click Yes to save a backup file of your generated tokens.
- Select the project you want to connect to by default from the Default Project (Choose after Generating Token) field.
- Select the Security tab.
-
Enter
https://auditservice.dev.azure.com,https://almsearch.dev.azure.cominto the Additional Trusted Domains field. - Select the Test Connection button at the bottom of the window to verify proper connectivity with your Azure DevOps account.
- If the connection test succeeds, select OK.
-
To edit previously created app you can visit
https://app.vsaex.visualstudio.com/meand see Applications and services section. Click on your desired app name.
API Connection Manager configuration
Just perform these simple steps to finish authentication configuration:
-
Set Authentication Type to
(Cloud) OAuth App - User Credentials (DEPRECATED) [OAuth] - Optional step. Modify API Base URL if needed (in most cases default will work).
- Fill in all the required parameters and set optional parameters if needed.
- Press Generate Token button to generate the tokens.
- Finally, hit OK button:
AzureDevopsDSNAzure DevOps(Cloud) OAuth App - User Credentials (DEPRECATED) [OAuth]https://dev.azure.comRequired Parameters Client Id (App ID) Fill-in the parameter... Client Secret Fill-in the parameter... Organization name or Id (e.g. mycompany) Fill-in the parameter... Return URL Fill-in the parameter... Scopes (Use .default for App Credentials) Fill-in the parameter... API Version Fill-in the parameter... Optional Parameters Default Project Name (Choose after Generating Token) RetryMode RetryWhenStatusCodeMatch RetryStatusCodeList 429 RetryCountMax 5 RetryMultiplyWaitTime True 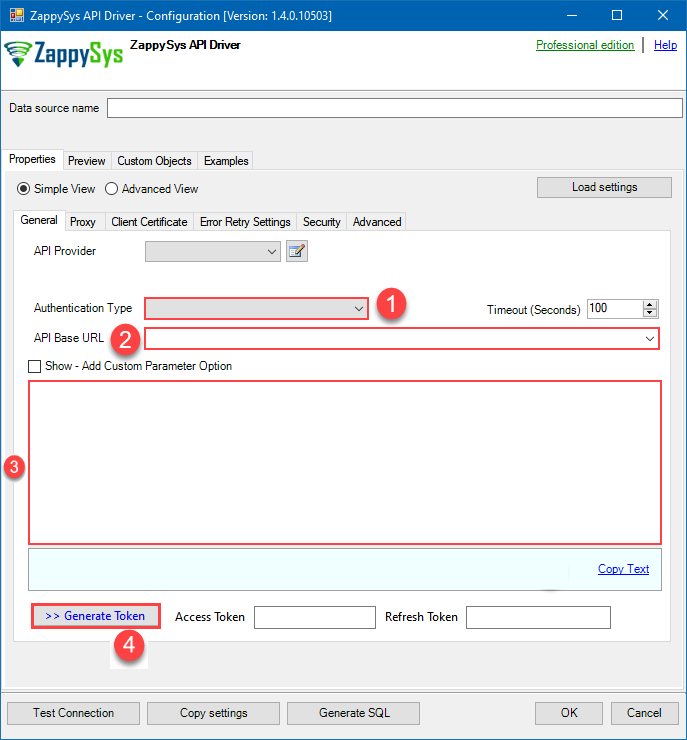 Find full details in the Azure DevOps Connector authentication reference.
Find full details in the Azure DevOps Connector authentication reference.(Cloud) Personal Access Token (PAT) (DEPRECATED)
Azure DevOps authentication
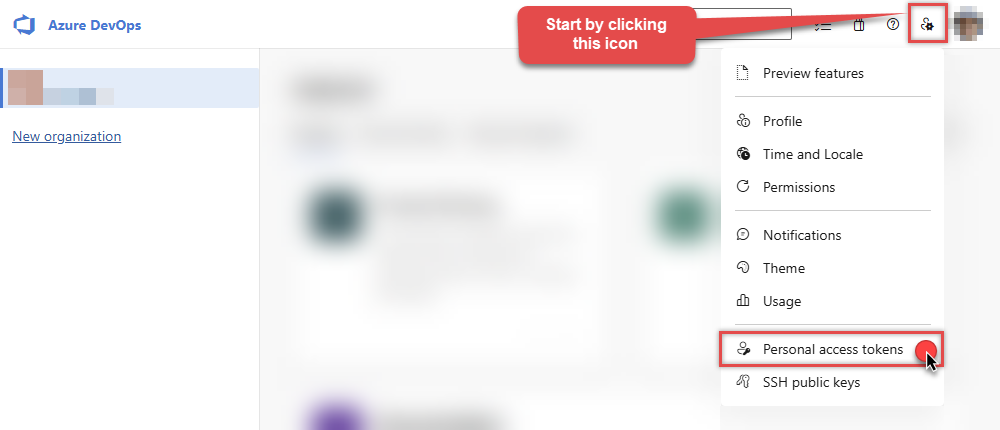
**DEPRECATED:** Personal Access Tokens are still supported but the new Azure App Credentials auth is recommended for security and automation. To connect to Azure DevOps using a Personal Access Token (PAT), you must first create a valid PAT:- Start by going to https://aex.dev.azure.com and selecting relevant organization on the left.
-
Then copy Organization's host name part (e.g.
acmeinc, if full host name isacmeinc.visualstudio.com), save it to a file, and click it: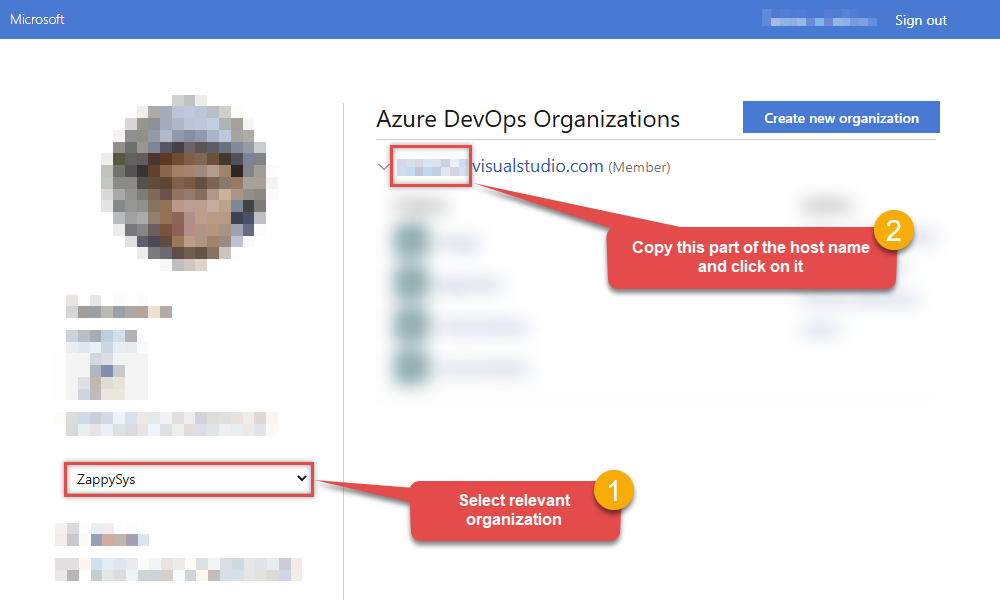
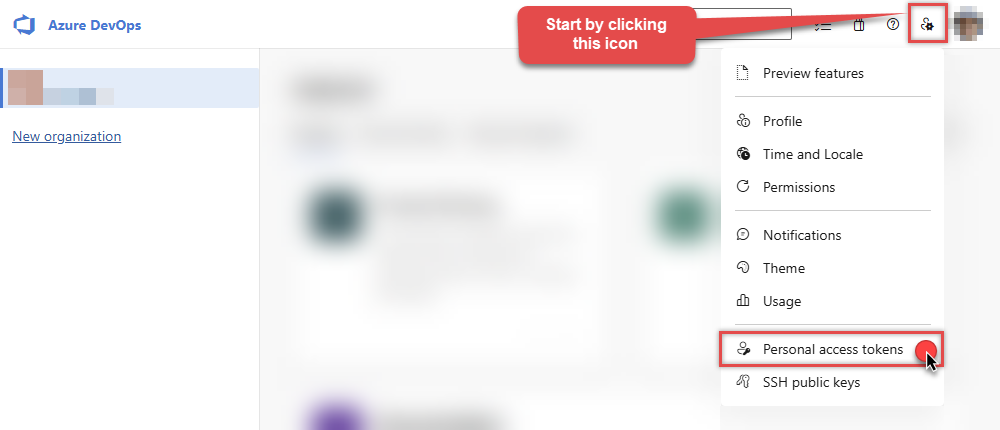
-
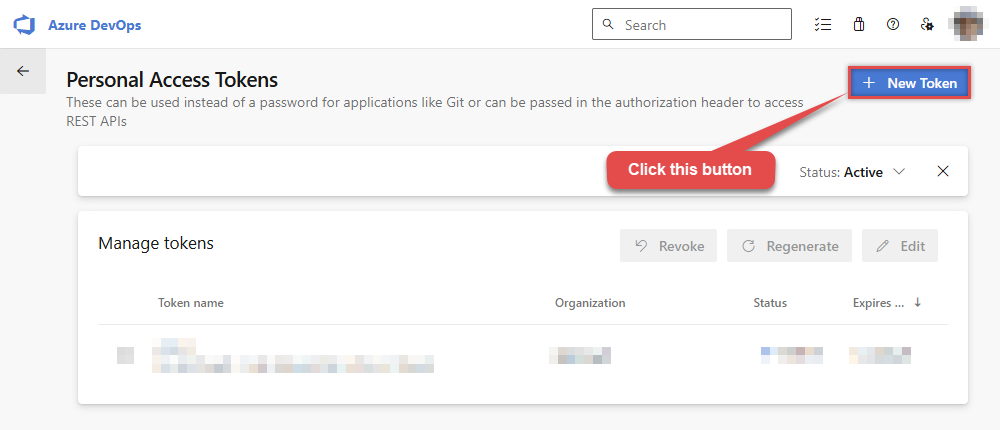
Next, click User settings icon and then click Personal access tokens:
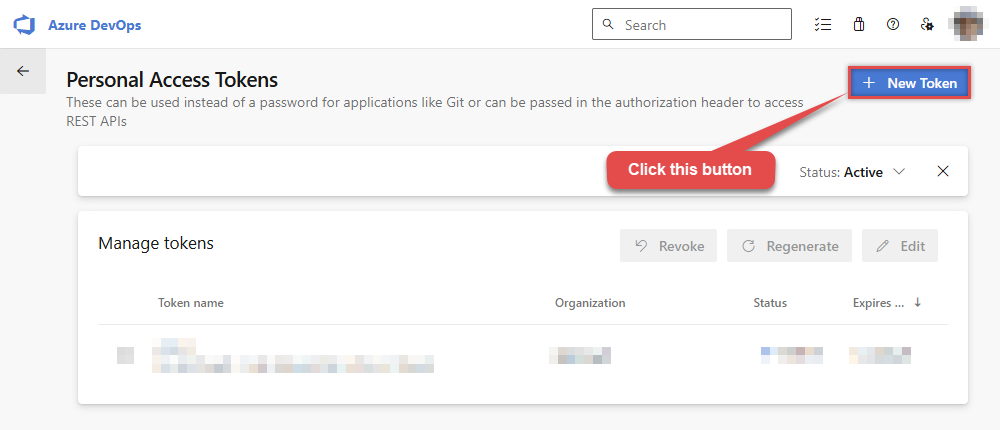
-
Then click New Token button to create a new personal access token:
-
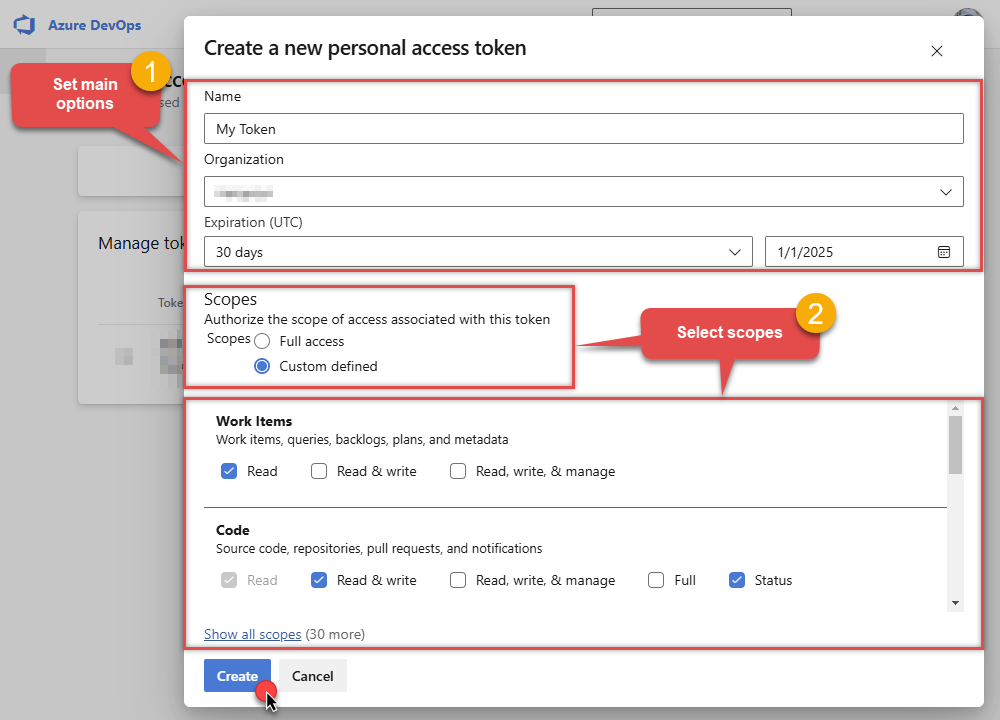
Continue by...
- naming your token
- selecting the right Organization
- setting token's Expiration date (it's recommended to use
Custom definedoption and make it expire after one year or later) - and setting the Scopes:
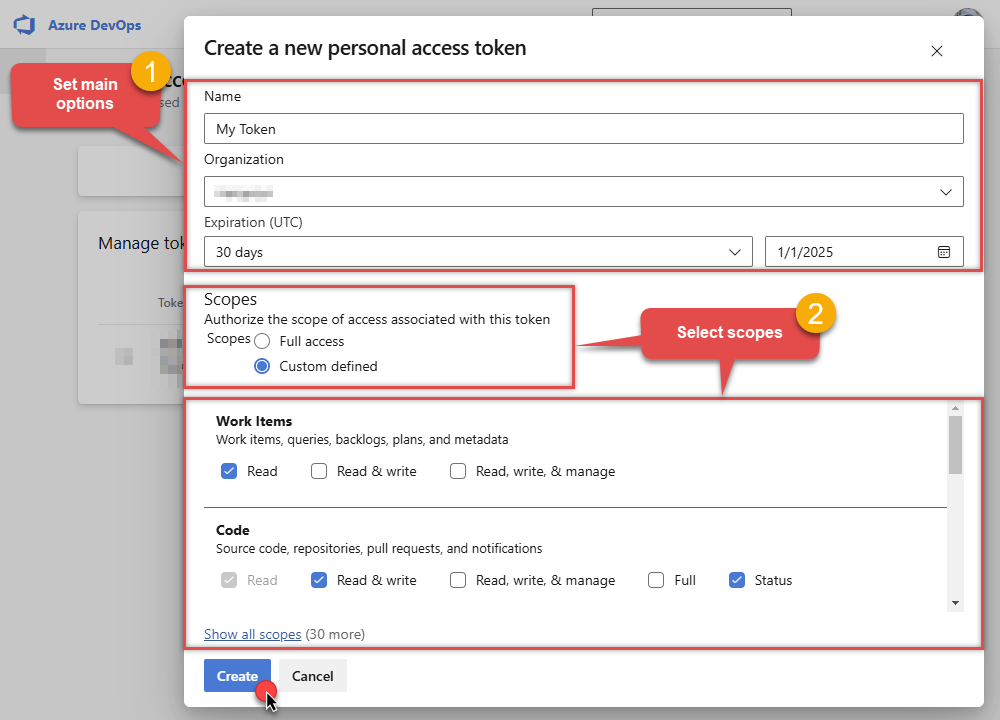
NOTE: You may be restricted from creating full-scoped PATs. If so, your Azure DevOps administrator in Azure AD has enabled a policy which limits you to a specific custom defined set of scopes.
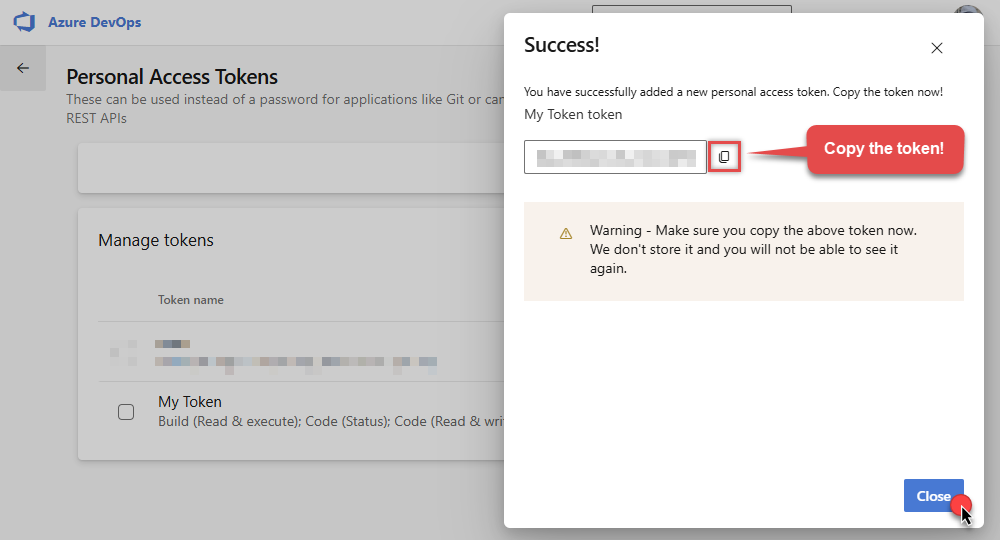
-
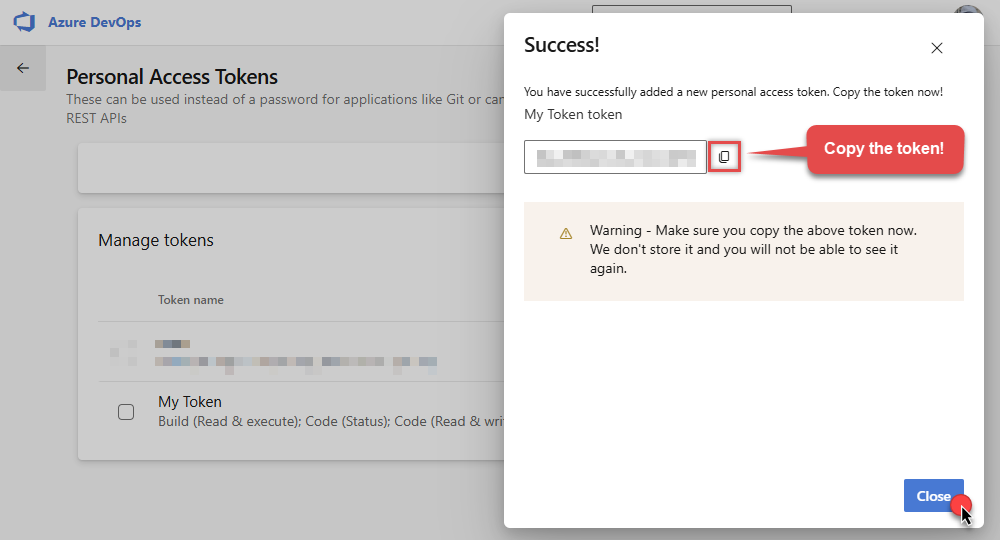
Now click Copy button and save the newly created token into a file for quick access later:
- Go back to the connector screen, input the token you saved in a previous step into the Personal Access Token (PAT) field.
- Then enter the Organization host name part that you noted recorded in previous step into Organization name or Id for url field.
- Enter the name or Id of the project you want to connect to by default in the Default Project (Choose after above fields) field.
- Select the Security tab.
- Enter
https://auditservice.dev.azure.com,https://almsearch.dev.azure.com,https://analytics.dev.azure.cominto the Additional Trusted Domains field. - Select the Test Connection button at the bottom of the window to verify proper connectivity with your Azure DevOps account.
- Done!
API Connection Manager configuration
Just perform these simple steps to finish authentication configuration:
-
Set Authentication Type to
(Cloud) Personal Access Token (PAT) (DEPRECATED) [Http] - Optional step. Modify API Base URL if needed (in most cases default will work).
- Fill in all the required parameters and set optional parameters if needed.
- Finally, hit OK button:
AzureDevopsDSNAzure DevOps(Cloud) Personal Access Token (PAT) (DEPRECATED) [Http]https://dev.azure.comRequired Parameters Personal Access Token (PAT) Fill-in the parameter... Organization name or Id for url Fill-in the parameter... API Version Fill-in the parameter... Optional Parameters AuthScheme Bearer AuthHeader Authorization Default Project Name RetryMode RetryWhenStatusCodeMatch RetryStatusCodeList 429 RetryCountMax 5 RetryMultiplyWaitTime True 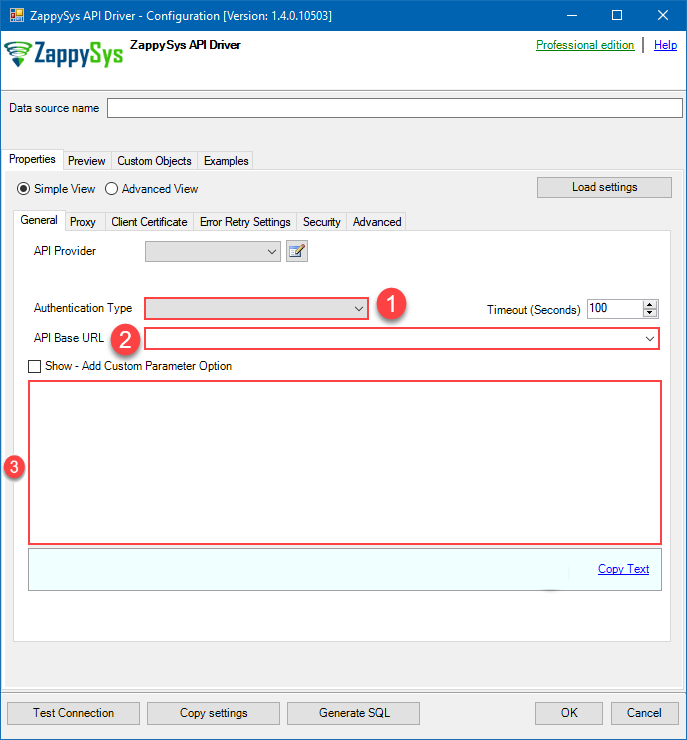 Find full details in the Azure DevOps Connector authentication reference.
Find full details in the Azure DevOps Connector authentication reference.(On-Premises) Personal Access Token (PAT) (DEPRECATED)
Azure DevOps authentication
**DEPRECATED:** On-premises PAT method is legacy; consider Azure App Credentials if your server supports Azure AD apps. To connect to Azure DevOps On-Premises Server using a Personal Access Token (PAT), you must first create a valid PAT:-
Start by navigating to your on-premises Azure DevOps Server URL.
NOTE: The screenshots shown below are from the cloud version, so your interface may look slightly different depending on which on-premises Azure DevOps Server version you’re using — however, the overall concepts and steps are very similar between the cloud and on-premises editions. -
Now open any project and capture Collection Name from the URL. For example if your URL is
https://tfs.mycompany.local/tfs/MyCollection/MyProject/
then your collection name is MyCollection usually after /tfs/. Copy this collection name and later we will enter on Connection UI. -
Next, click User settings icon and then click Personal access tokens:
-
Then click New Token button to create a new personal access token:
-
Continue by...
- naming your token
- selecting the right Organization
- setting token's Expiration date (it's recommended to use
Custom definedoption and make it expire after one year or later) - and setting the Scopes:
NOTE: You may be restricted from creating full-scoped PATs. If so, your Azure DevOps administrator in Azure AD has enabled a policy which limits you to a specific custom defined set of scopes.
-
Now click Copy button and save the newly created token into a file for quick access later:
- Go back to the connector screen, input the token you saved in a previous step into the Personal Access Token (PAT) field.
- Then enter the Organization host name part that you noted recorded in previous step into Organization name or Id for url field.
- Enter the name or Id of the project you want to connect to by default in the Default Project (Choose after above fields) field.
- Select the Security tab.
- Enter
https://auditservice.dev.azure.com,https://almsearch.dev.azure.com,https://analytics.dev.azure.cominto the Additional Trusted Domains field. - Select the Test Connection button at the bottom of the window to verify proper connectivity with your Azure DevOps account.
- Done!
API Connection Manager configuration
Just perform these simple steps to finish authentication configuration:
-
Set Authentication Type to
(On-Premises) Personal Access Token (PAT) (DEPRECATED) [Http] - Optional step. Modify API Base URL if needed (in most cases default will work).
- Fill in all the required parameters and set optional parameters if needed.
- Finally, hit OK button:
AzureDevopsDSNAzure DevOps(On-Premises) Personal Access Token (PAT) (DEPRECATED) [Http]https://dev.azure.comRequired Parameters Personal Access Token (PAT) Fill-in the parameter... Collection name (e.g. MyCollection) Fill-in the parameter... API Version Fill-in the parameter... Optional Parameters AuthScheme Bearer AuthHeader Authorization Default Project Name RetryMode RetryWhenStatusCodeMatch RetryStatusCodeList 429 RetryCountMax 5 RetryMultiplyWaitTime True 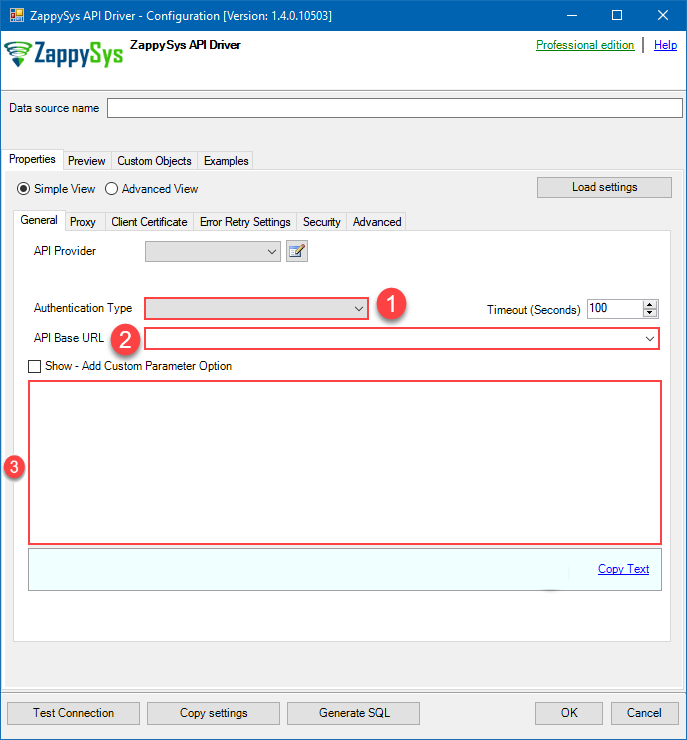 Find full details in the Azure DevOps Connector authentication reference.
Find full details in the Azure DevOps Connector authentication reference. -
Once the data source connection has been configured, it's time to configure the SQL query. Select the Preview tab and then click Query Builder button to configure the SQL query:
 ZappySys API Driver - Azure DevOpsRead and write Azure DevOps (Cloud or On-Premises) data effortlessly. Integrate, manage, and automate work items, projects, and teams — almost no coding required.AzureDevopsDSN
ZappySys API Driver - Azure DevOpsRead and write Azure DevOps (Cloud or On-Premises) data effortlessly. Integrate, manage, and automate work items, projects, and teams — almost no coding required.AzureDevopsDSN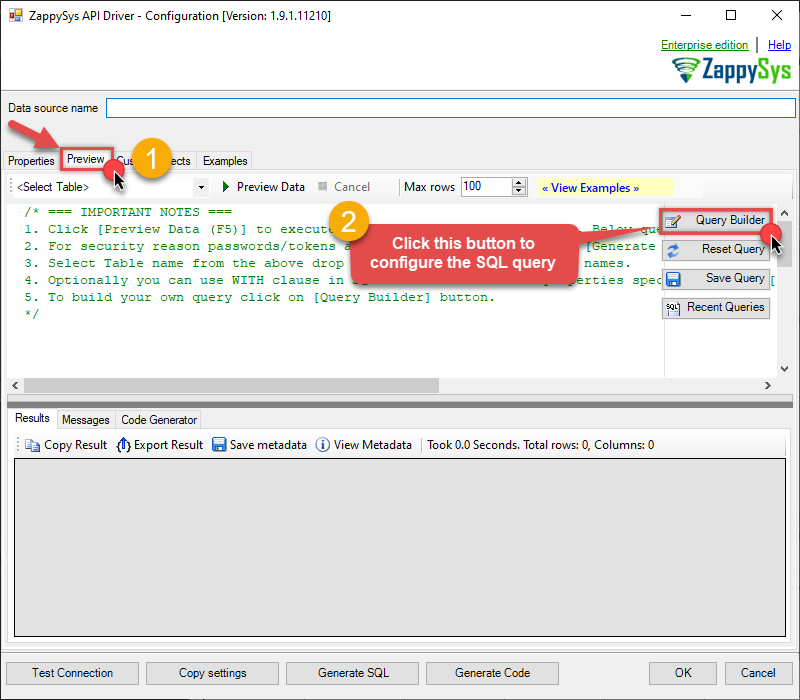
-
Start by selecting the Table or Endpoint you are interested in and then configure the parameters. This will generate a query that we will use in Microsoft Fabric to retrieve data from Azure DevOps. Hit OK button to use this query in the next step.
SELECT * FROM WorkItems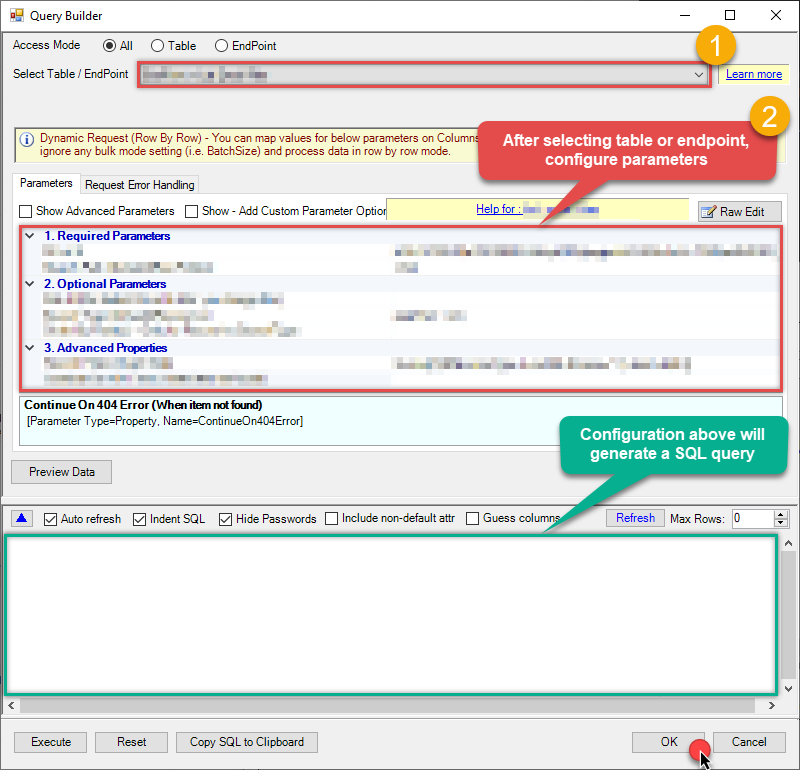 Some parameters configured in this window will be passed to the Azure DevOps API, e.g. filtering parameters. It means that filtering will be done on the server side (instead of the client side), enabling you to get only the meaningful data
Some parameters configured in this window will be passed to the Azure DevOps API, e.g. filtering parameters. It means that filtering will be done on the server side (instead of the client side), enabling you to get only the meaningful datamuch faster . -
Now hit Preview Data button to preview the data using the generated SQL query. If you are satisfied with the result, use this query in Microsoft Fabric:
 ZappySys API Driver - Azure DevOpsRead and write Azure DevOps (Cloud or On-Premises) data effortlessly. Integrate, manage, and automate work items, projects, and teams — almost no coding required.AzureDevopsDSN
ZappySys API Driver - Azure DevOpsRead and write Azure DevOps (Cloud or On-Premises) data effortlessly. Integrate, manage, and automate work items, projects, and teams — almost no coding required.AzureDevopsDSNSELECT * FROM WorkItems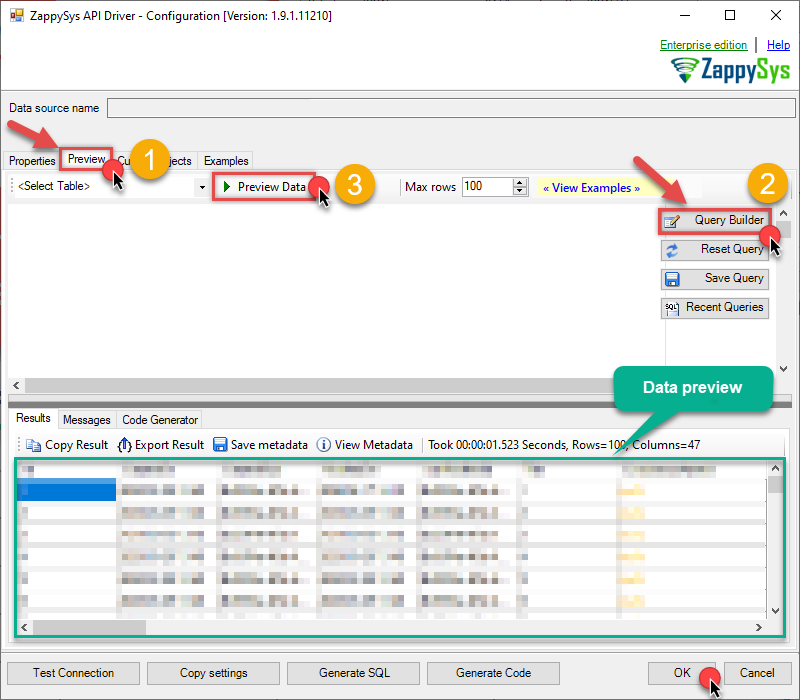 You can also access data quickly from the tables dropdown by selecting <Select table>.A
You can also access data quickly from the tables dropdown by selecting <Select table>.AWHEREclause,LIMITkeyword will be performed on the client side, meaning that thewhole result set will be retrieved from the Azure DevOps API first, and only then the filtering will be applied to the data. If possible, it is recommended to use parameters in Query Builder to filter the data on the server side (in Azure DevOps servers). -
Click OK to finish creating the data source.
Install Microsoft On-premises data gateway (Standard mode)
To access and read Azure DevOps data in Microsoft Fabric, you must download and install the Microsoft On-premises data gateway (Standard mode). It acts as a secure bridge between Microsoft Fabric cloud services and your local Azure DevOps ODBC data source:

There are two types of On-premises data gateways:
- Supports Power BI and other Microsoft Cloud services
- Installs as a Windows service
- Starts automatically
- Supports centralized user access control
- Supports the
Direct Queryfeature - Ideal for enterprise solutions
- Supports Power BI services only
- Cannot run as a Windows service
- Stops when you sign out of Windows
- Does not support access control
- Does not support the
Direct Queryfeature - Best for individual use and POC solutions
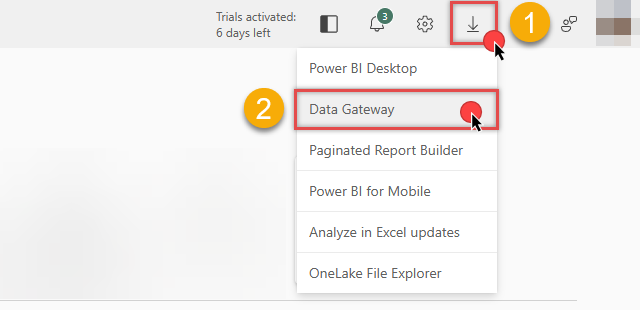
You can download the On-premises data gateway directly from the Microsoft Fabric or Power BI portals:
Link ODBC data source via the gateway
Follow these steps to download, install, and configure the gateway in Standard mode:
-
Download On-premises data gateway (standard mode) and run the installer.
-
Once the configuration window opens, sign in:
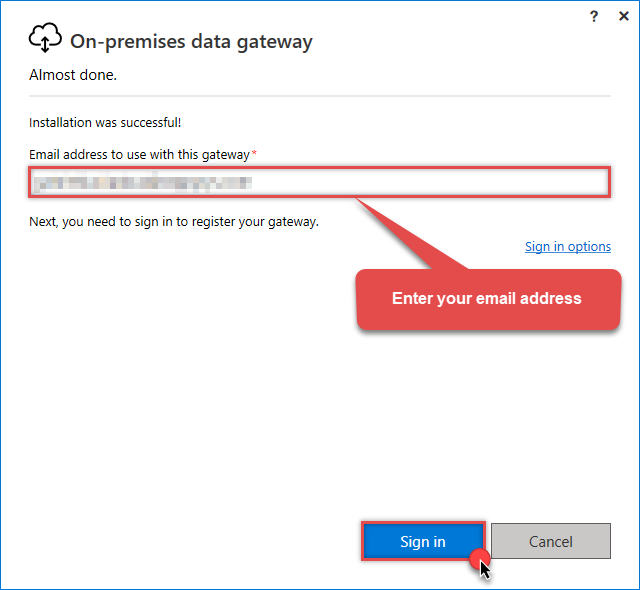 Sign in with the same email address you use for Microsoft Fabric.
Sign in with the same email address you use for Microsoft Fabric. -
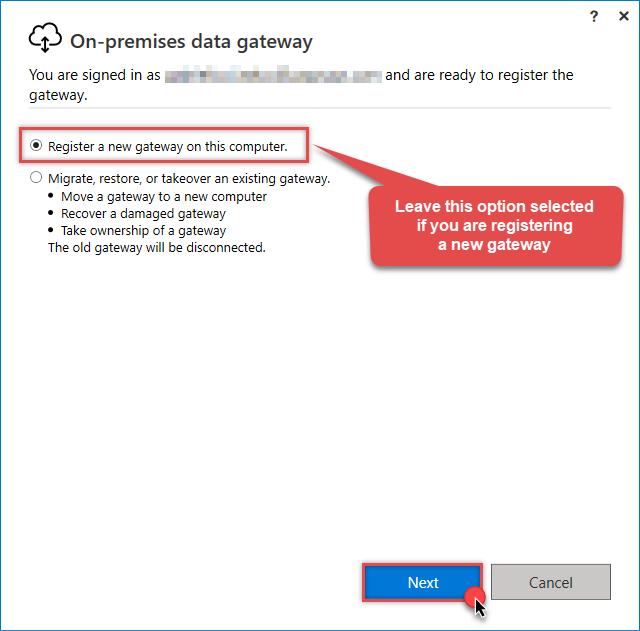
Select Register a new gateway on this computer (or migrate an existing one):
-
Name your gateway, enter a Recovery key, and click the Configure button:
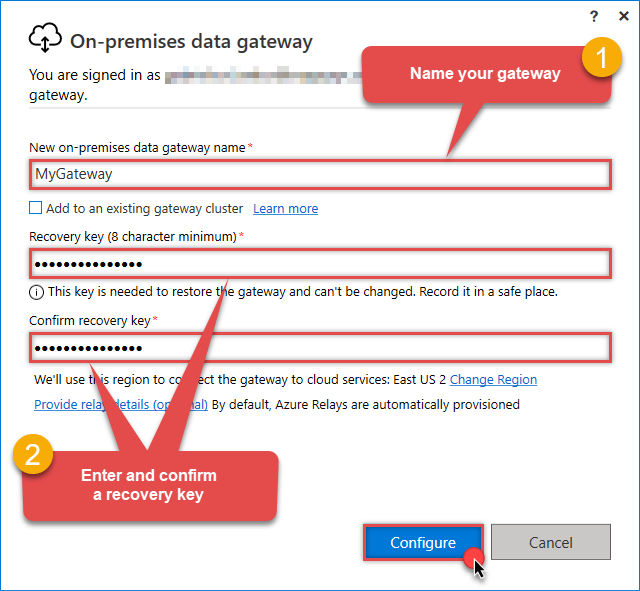 Save your Recovery Key in a safe place (like a password manager). If you lose it, you cannot restore or migrate this gateway later.
Save your Recovery Key in a safe place (like a password manager). If you lose it, you cannot restore or migrate this gateway later. -
Once Microsoft gateway is installed, check if it registered correctly:
-
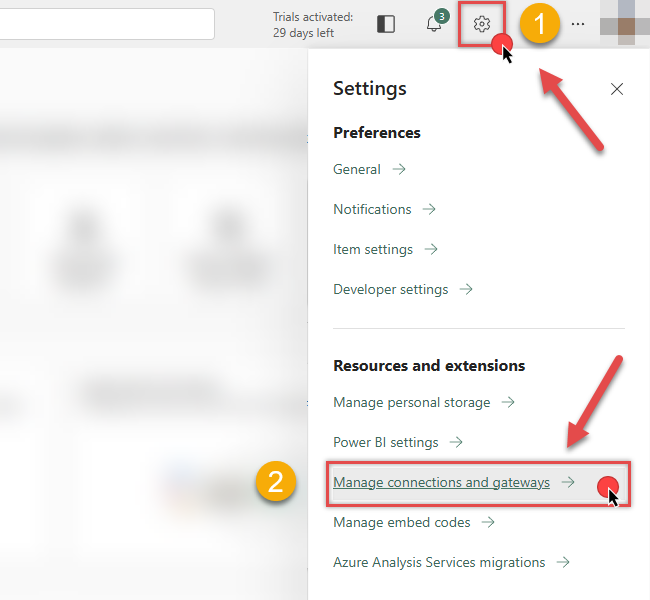
Go back to Microsoft Fabric portal
-
Click Gear icon on top-right
-
And then hit Manage connections and gateways menu item
-
-
Continue by clicking the On-premises data gateway tab and selecting Standard mode gateways from the dropdown menu:
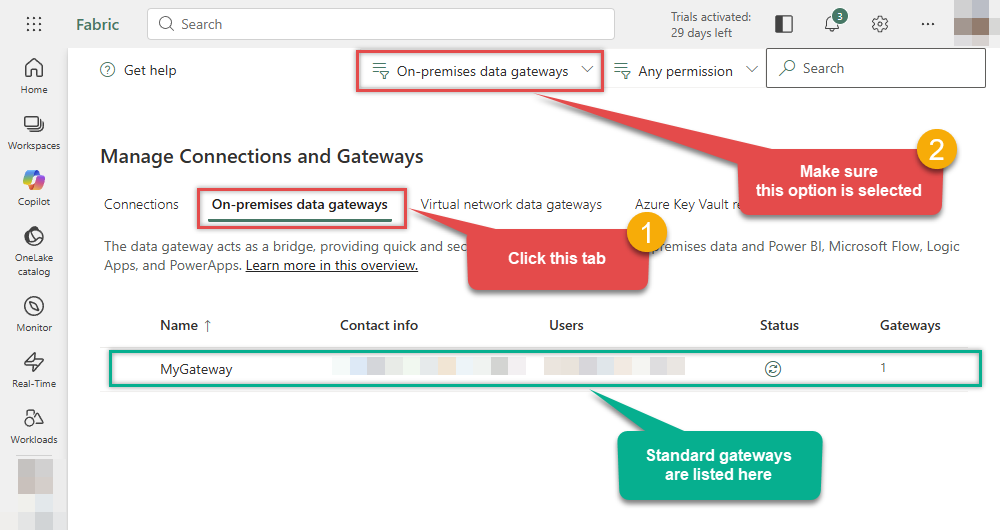
If your gateway is not listed, the registration may have failed. To resolve this:
- Wait a couple of minutes and refresh Microsoft Fabric portal page
- Restart the machine where On-premises data gateway is installed
- Check firewall settings
-
Success! The gateway is now Online and ready to handle requests.
- Done!
You are now ready to load data into Microsoft Fabric.
Load Azure DevOps data into Microsoft Fabric
Now that we have configured the ODBC data source and installed the On-premises data gateway, we can proceed with loading data. You can accomplish this in two ways:
-
Copy job
Best for simple, high-speed data copying without modification.
-
Dataflow Gen2
Best if you need to transform, clean, or reshape data before loading.
Let's dive into the steps for both methods.
Use Copy job for high-speed loading
-
Go to the Microsoft Fabric Portal.
-
Select an existing Workspace or create a new one by clicking New workspace (ensure you are in the Home section):
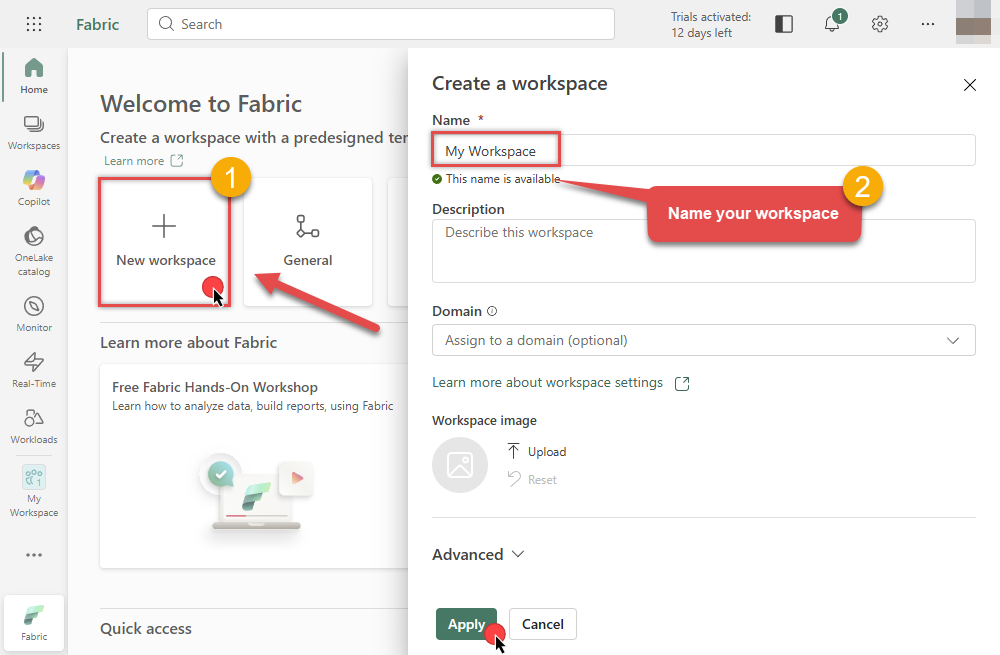
-
Inside your workspace, click the New item button in the toolbar to start creating your data pipeline:

-
In the item selection window, choose Copy job to open the data ingestion wizard:

-
In the Choose data source screen, search for
odbcand select the Odbc source: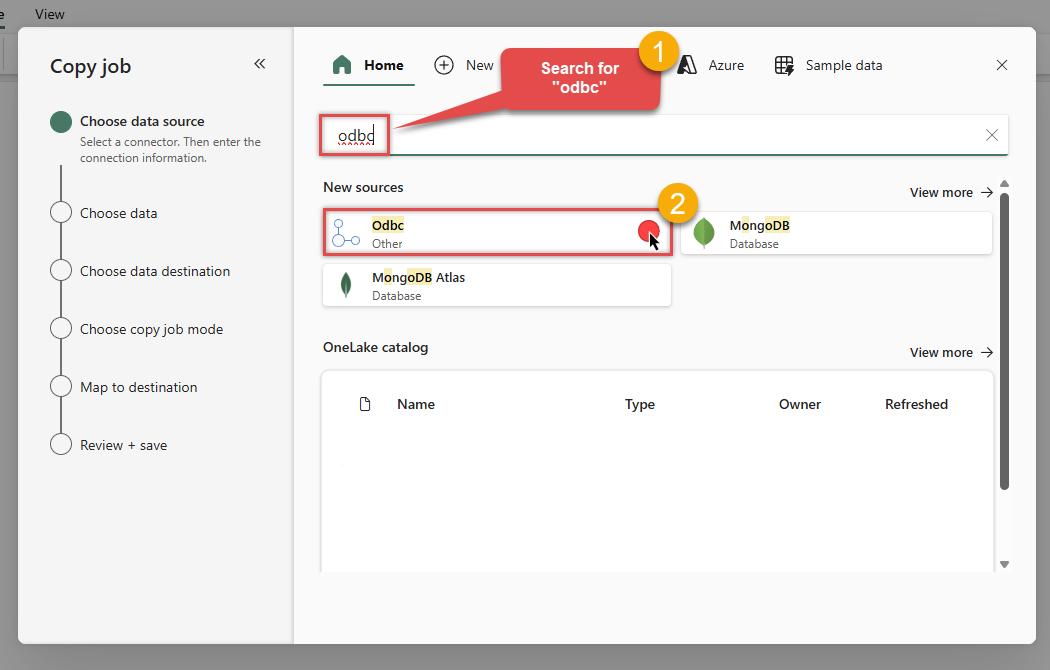
-
Then enter your ODBC connection string (
DSN=AzureDevopsDSN) and selectMyGatewayfrom the Data gateway dropdown we configured in the previous step:DSN=AzureDevopsDSNDSN=AzureDevopsDSN
-
Select the table(s) and preview the data you wish to copy from Azure DevOps. Once done, click Next:
DSN=AzureDevopsDSN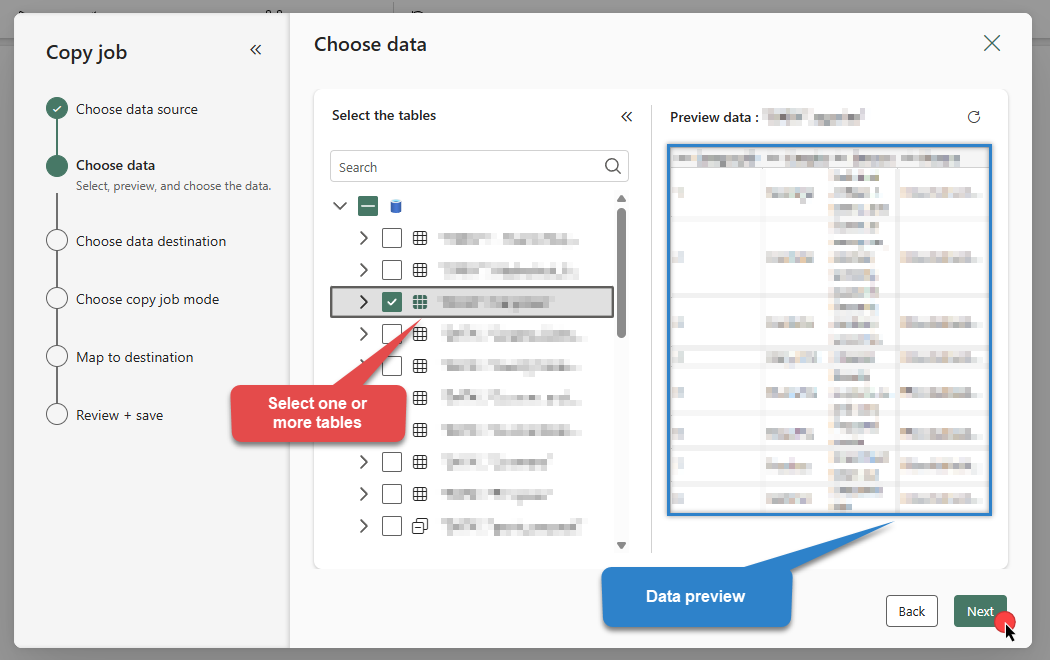
-
Choose your Data Destination. You can create a New Fabric item (like a Lakehouse or Warehouse) or select an existing one:
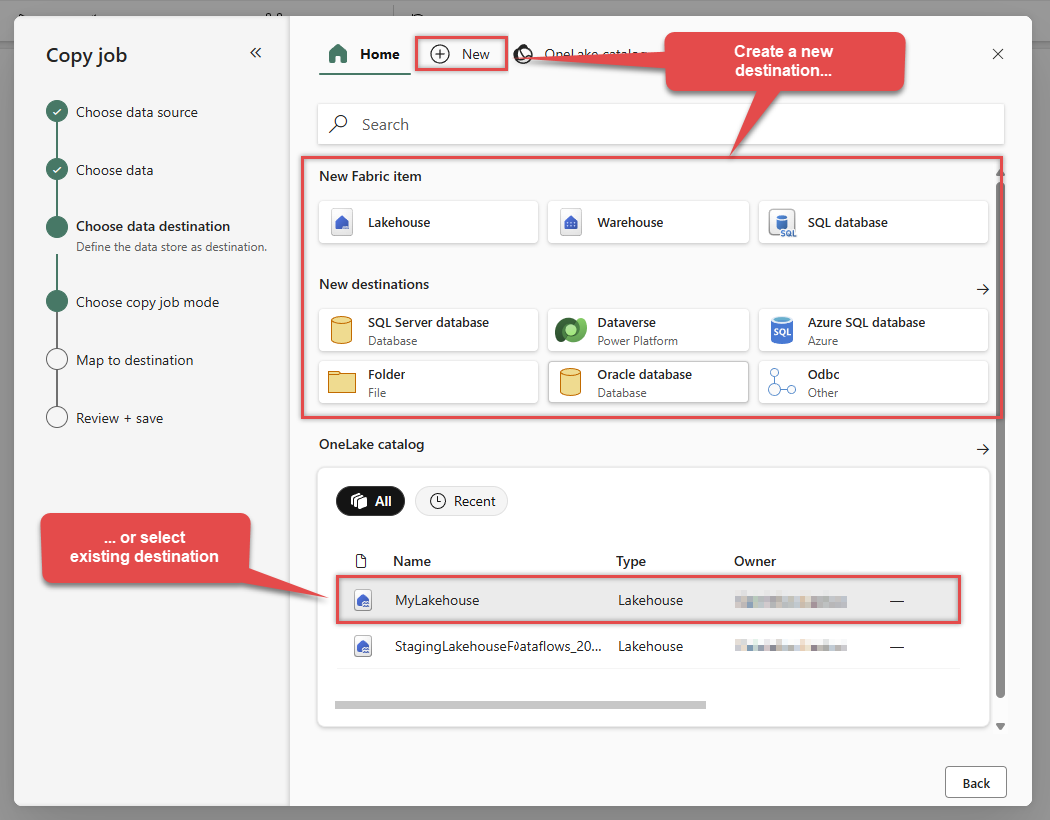 In this example, we will use a Lakehouse as the destination.
In this example, we will use a Lakehouse as the destination. -
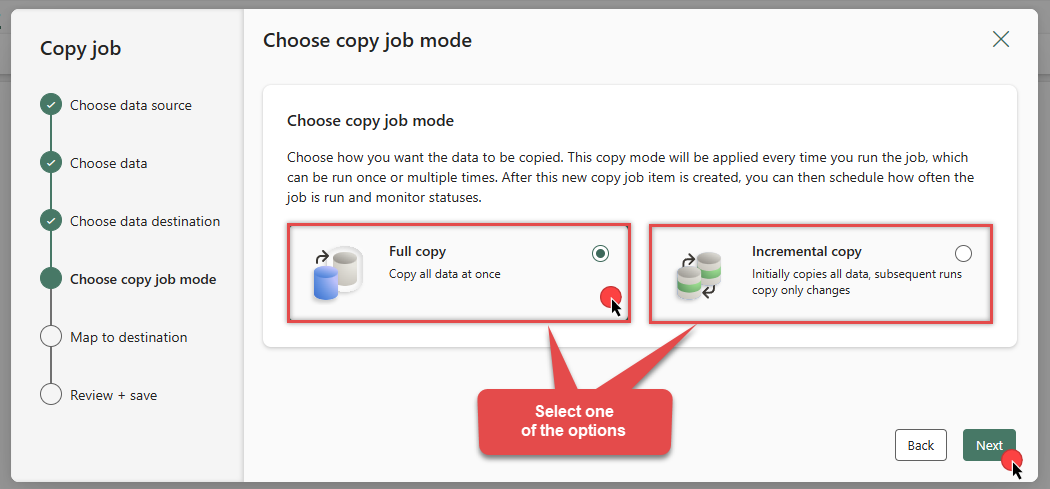
Choose Full copy to load all data, or Incremental copy to load only changed data in subsequent runs:
-
Review the Column and Table mappings section:
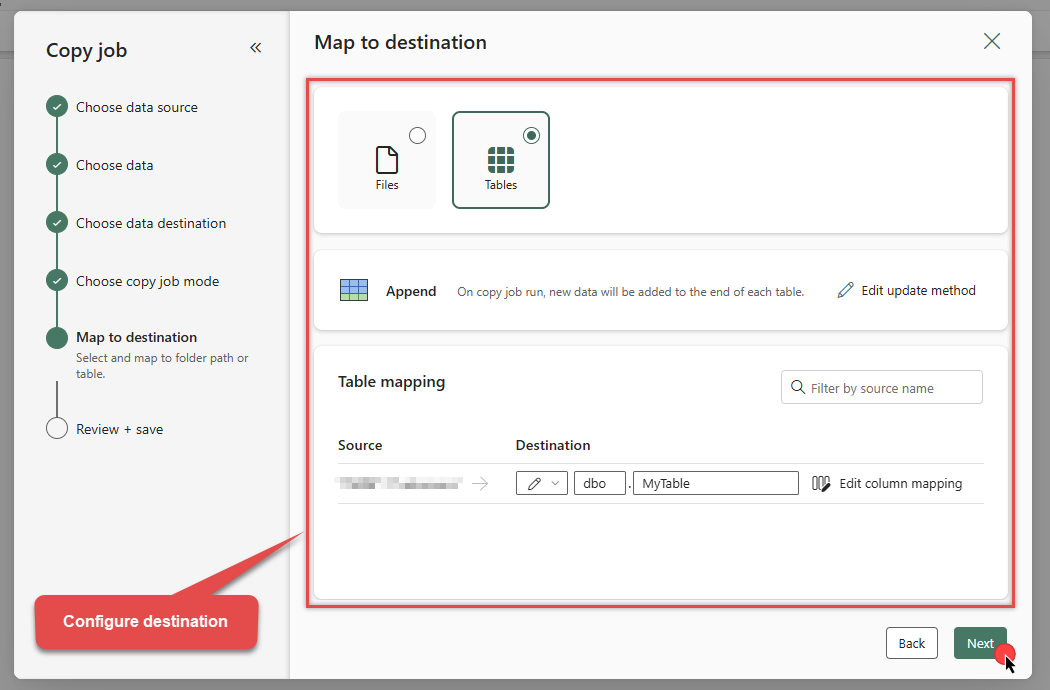
-
On the summary screen, review your settings. You can optionally enable Run on schedule. Click Save + Run to execute the job:
DSN=AzureDevopsDSNDSN=AzureDevopsDSN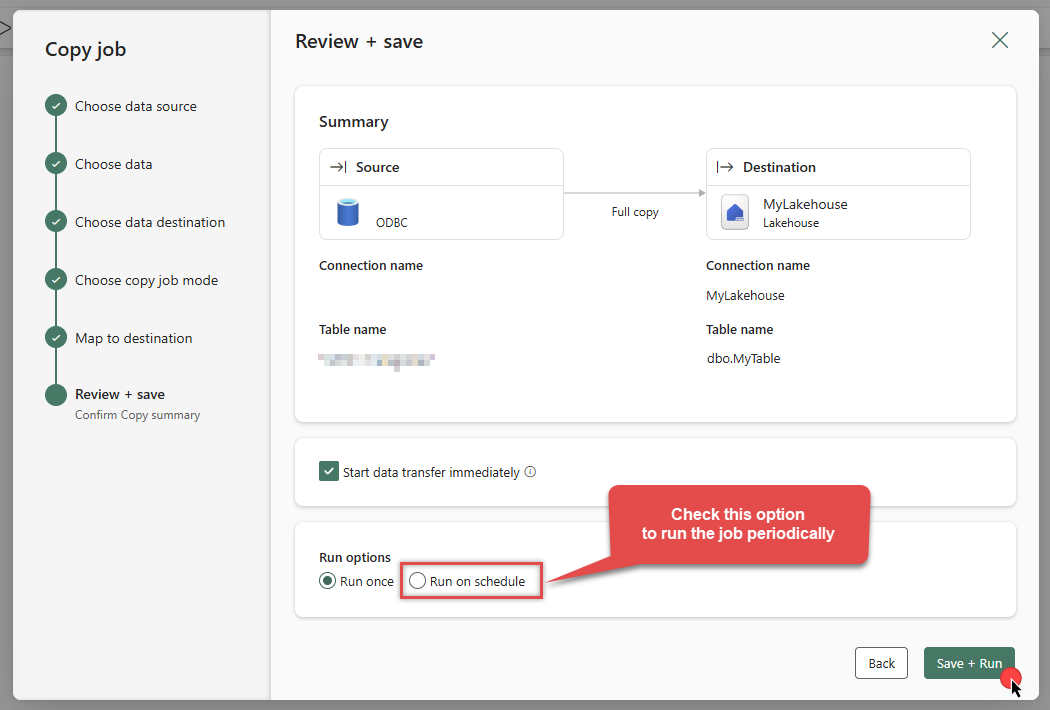
-
The job will enter the queue. Monitor the Status column to see the progress:
DSN=AzureDevopsDSN
-
Wait for the status to change to Succeeded. Your Azure DevOps data is now successfully integrated into Microsoft Fabric!

-
Let's go to our Lakehouse (
MyLakehouse) and verify the data: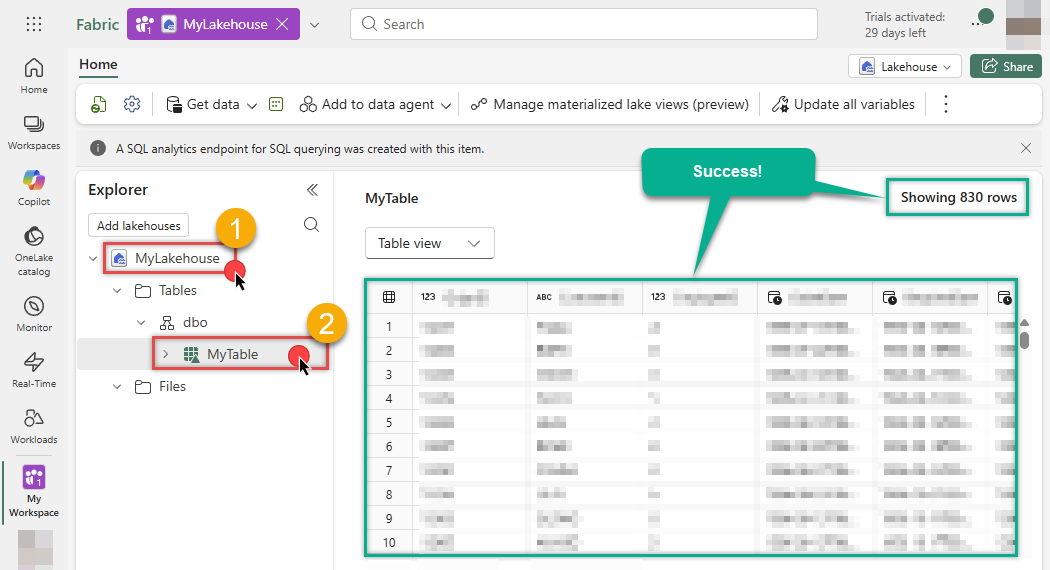
-
Success! The data has been loaded.
Use Dataflow for advanced transformation
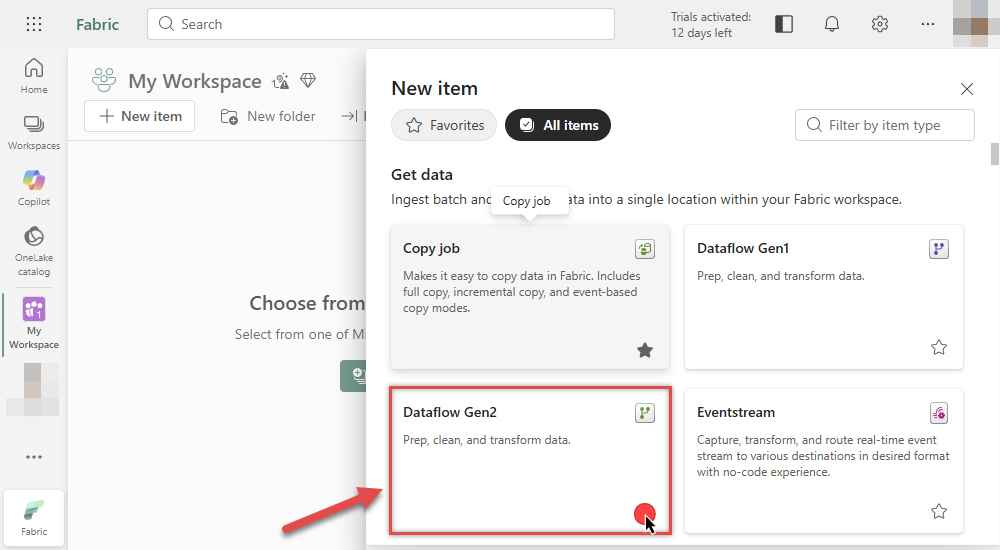
Another way to load data is by creating a Dataflow Gen2. This approach allows you to perform complex data transformations (ETL) before loading the data into its destination.
Configure Dataflow activity
-
Go to the Microsoft Fabric Portal.
-
Inside your workspace, click New item and select Dataflow Gen2:
-
In the Power Query editor, click Get data from another source:
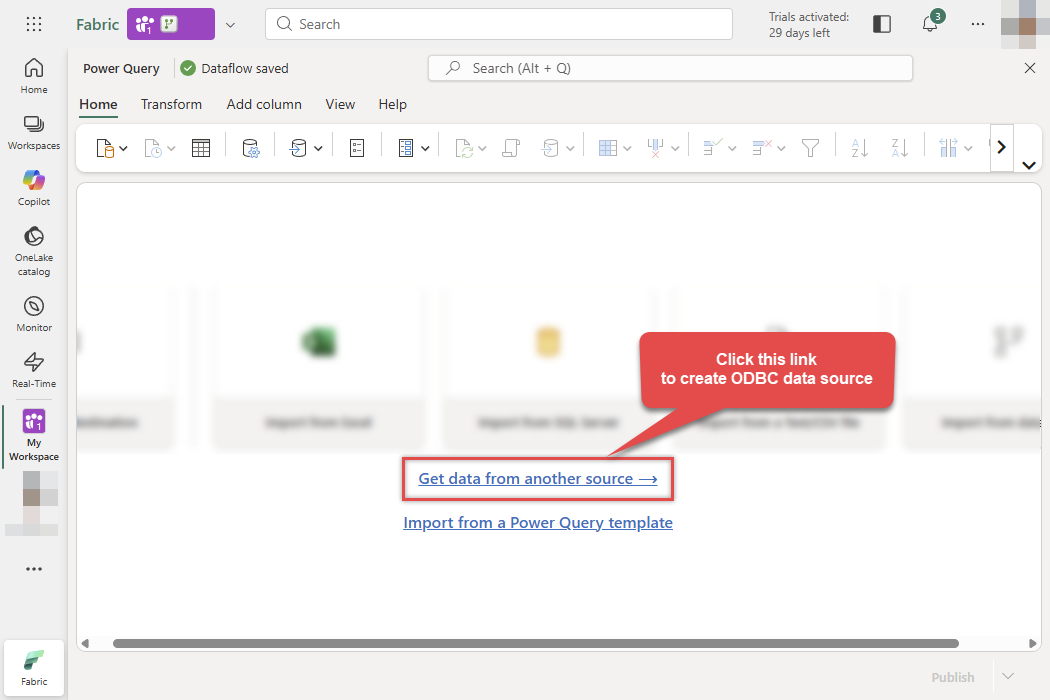
-
Search for ODBC in the search bar and select the ODBC connector:
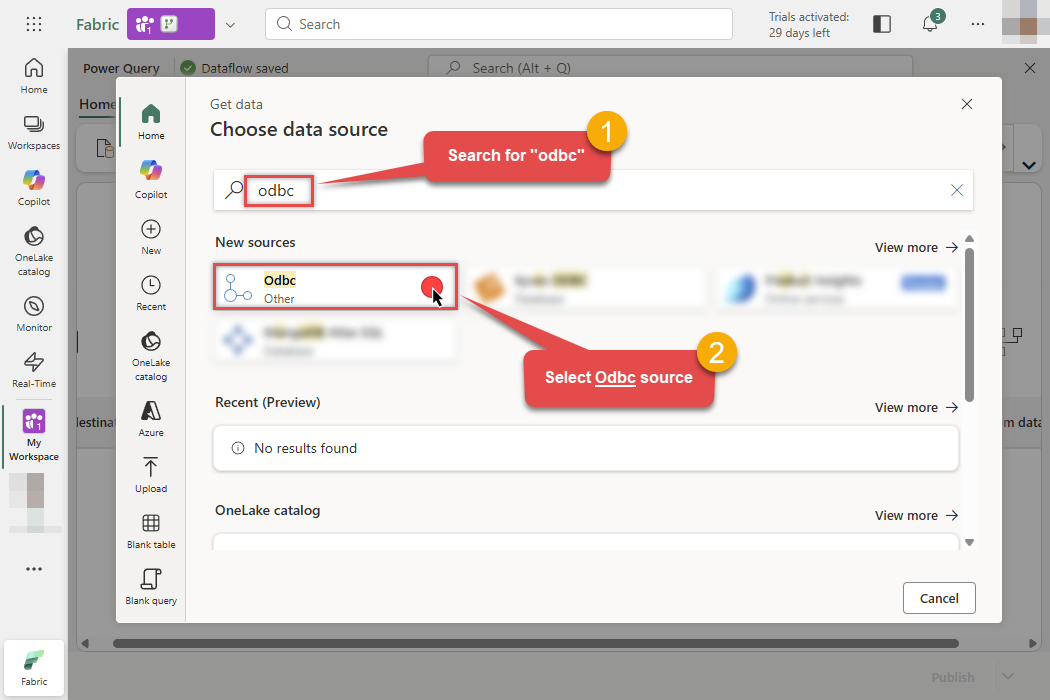
-
Then in the next step follow these instructions:
-
Enter your ODBC connection string (e.g.,
DSN=AzureDevopsDSN) - Expand Advanced options
- Enter your SQL statement
- Select your On-premises data gateway
- Finally, click Next:
DSN=AzureDevopsDSNDSN=AzureDevopsDSNSELECT * FROM WorkItems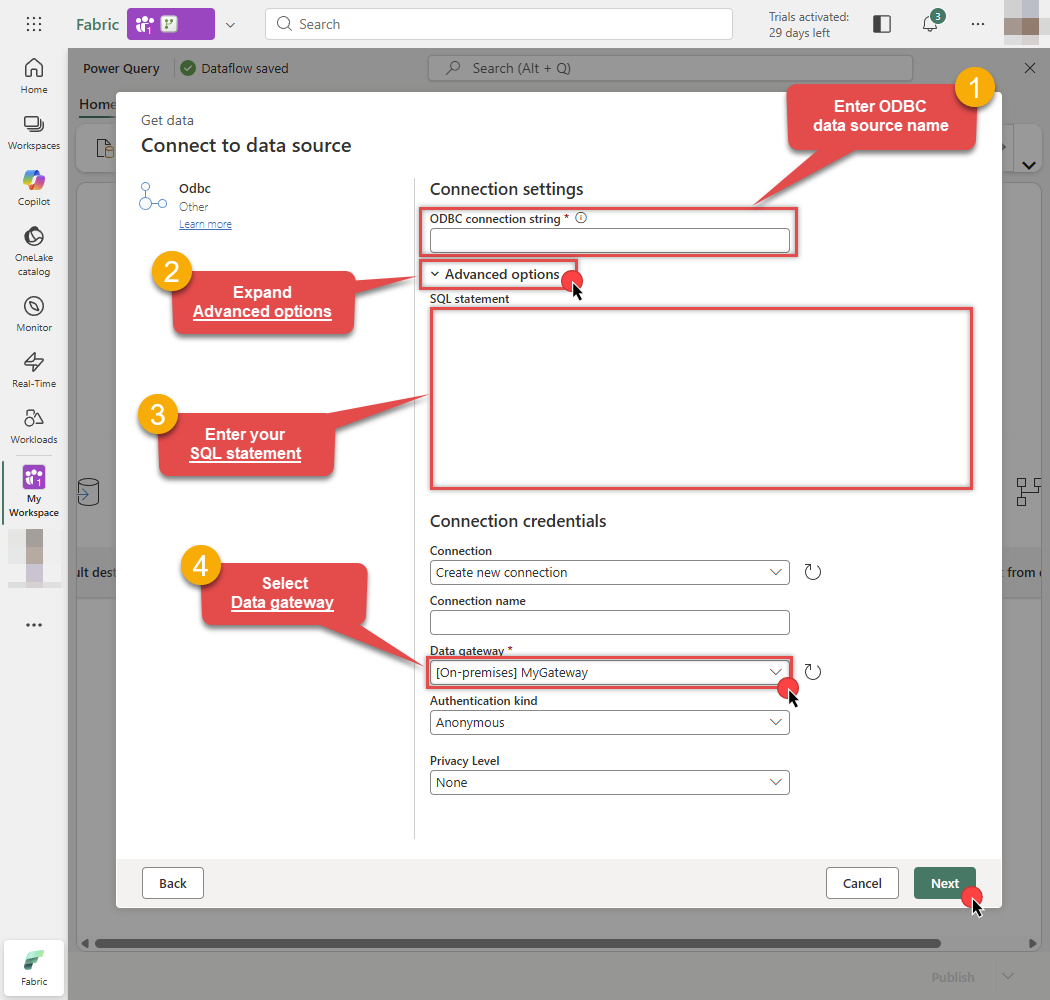
-
Enter your ODBC connection string (e.g.,
-
You will see a preview of your Azure DevOps data. You can now transform the data if needed (filter rows, rename columns, change types, etc.):
Odbc.Query("DSN=AzureDevopsDSN", "SELECT * FROM WorkItems")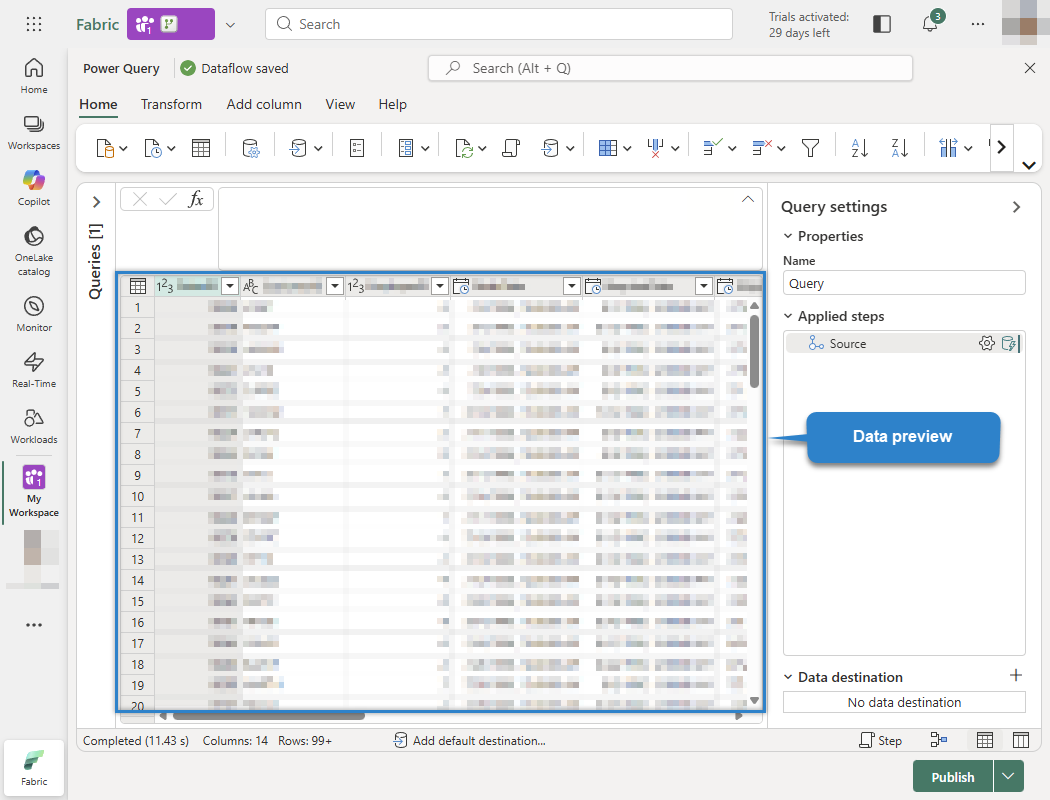
-
Now, let's send this data to the Lakehouse. Click the + button (Add data destination) at the bottom right and select Lakehouse:
Odbc.Query("DSN=AzureDevopsDSN", "SELECT * FROM WorkItems")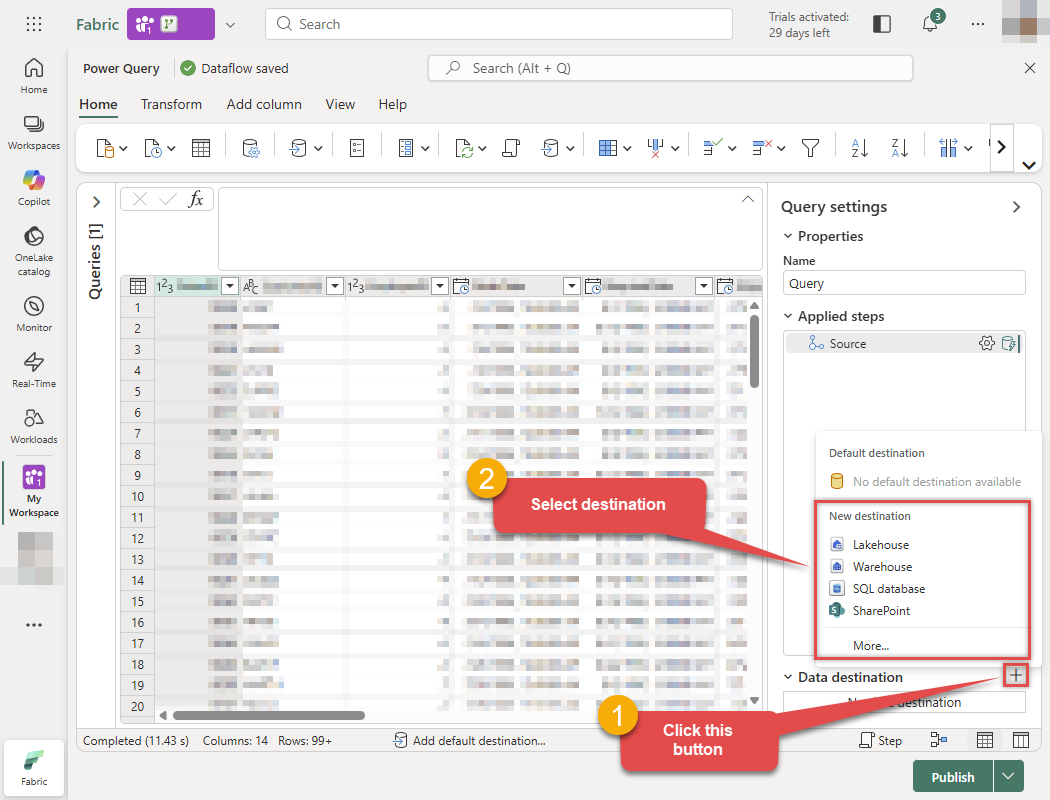
-
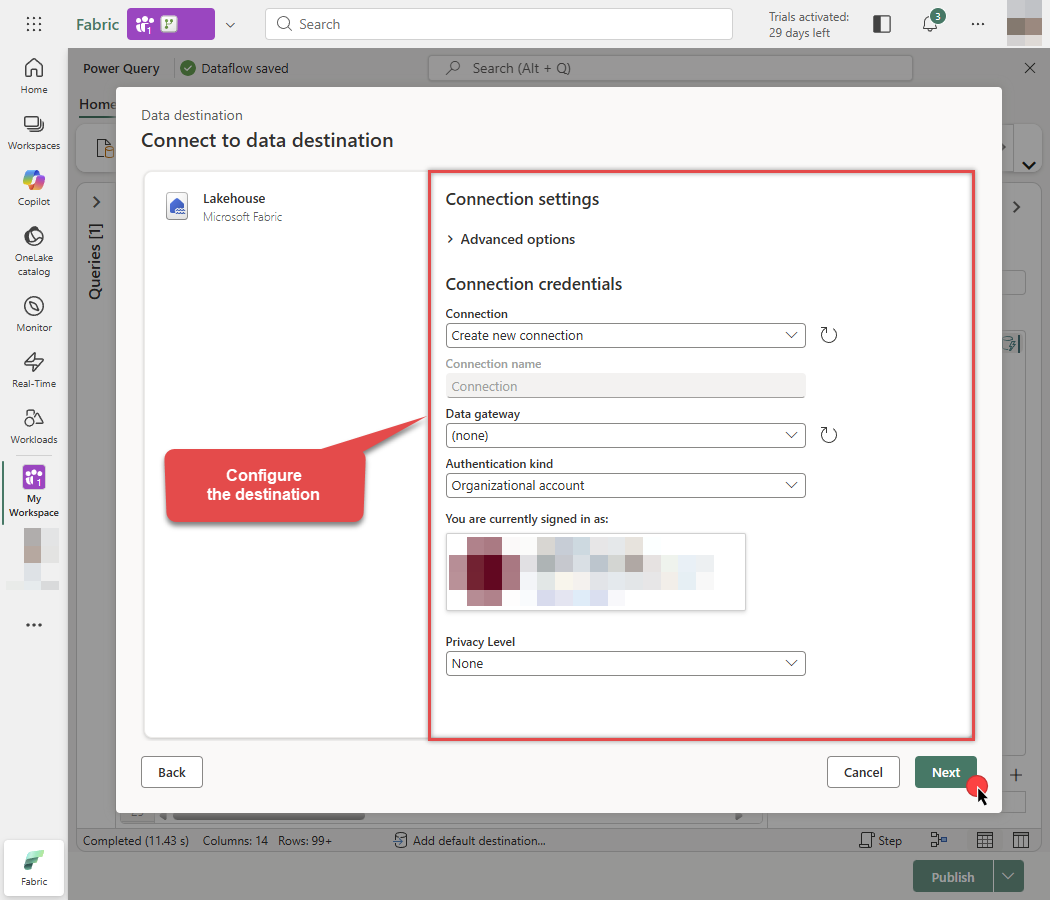
Configure the destination connection settings and click Next:
-
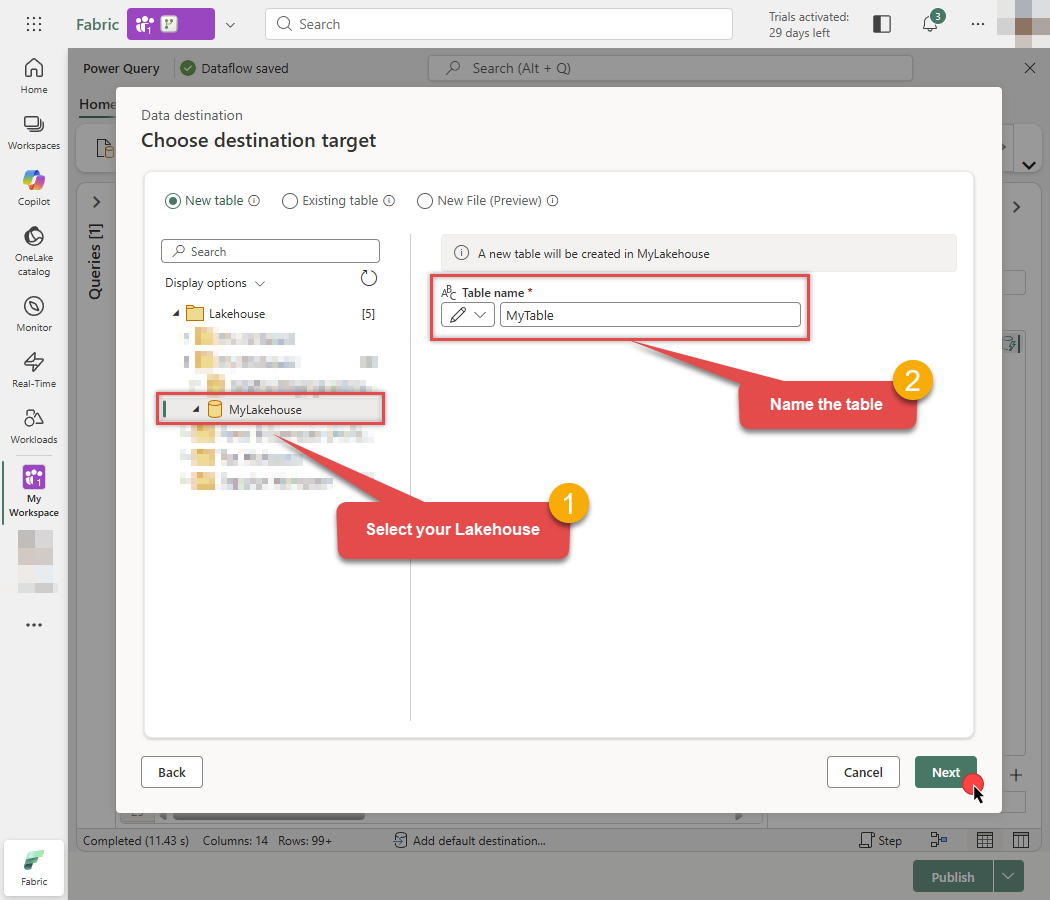
Select your specific Lakehouse, enter the Table name you want to create, and click Next:
-
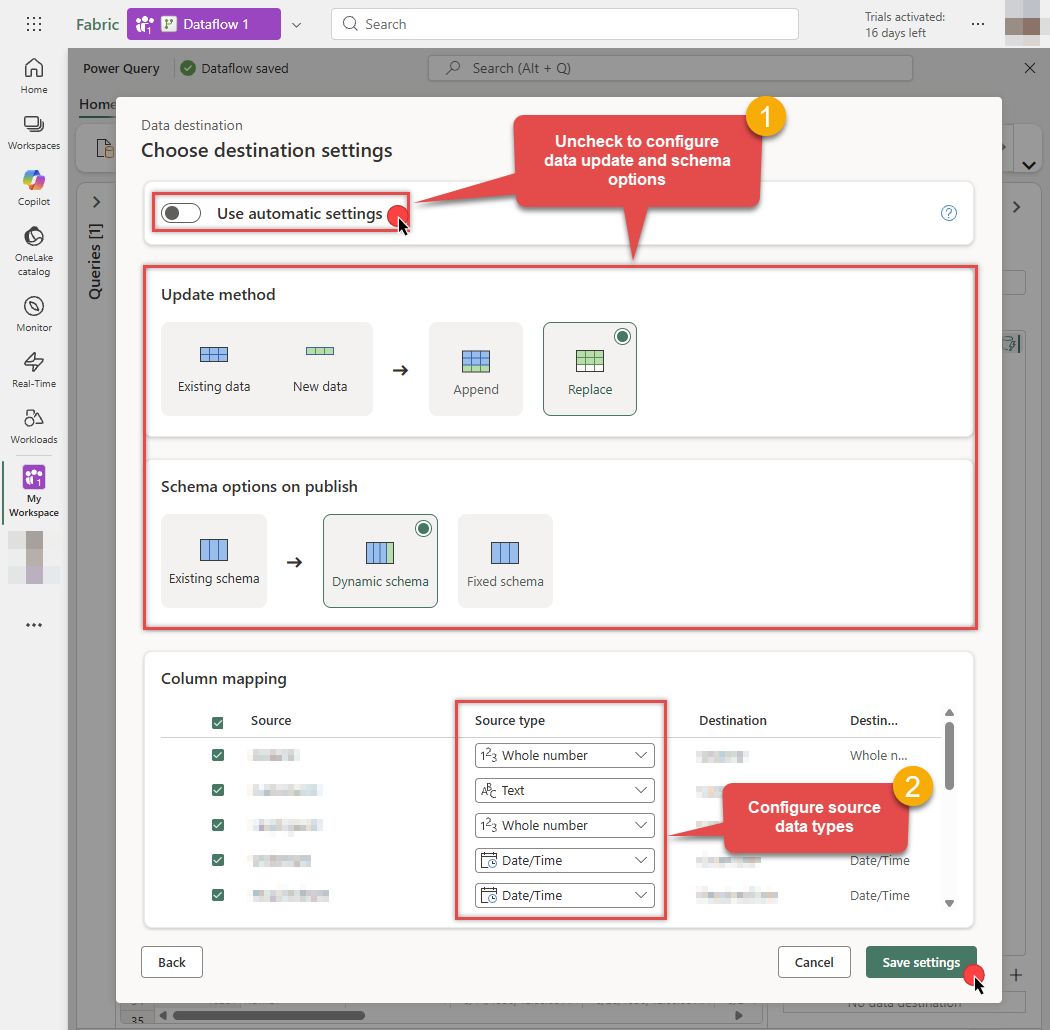
Uncheck Use automatic settings to set data update or schema options manually. Map the columns with proper data types and click Save settings when done:
-
The destination is now set. Click the Publish button to save the Dataflow:
Odbc.Query("DSN=AzureDevopsDSN", "SELECT * FROM WorkItems")
-
Done! You can now start building reports using your new semantic model.
Configure and run Pipeline
Once you have created and published your Dataflow, you can use a Pipeline to orchestrate and run it.
-
Go to the Microsoft Fabric Portal.
-
Inside your workspace, click New item and select Data Pipeline to create a new pipeline.
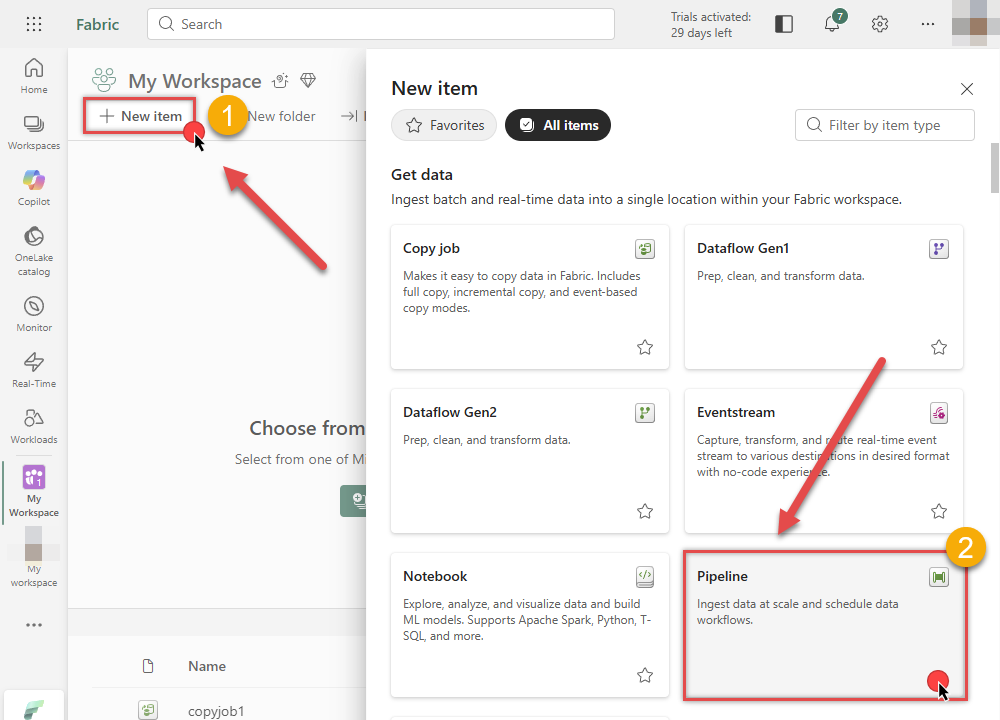
-
In the pipeline editor, select the Dataflow activity from the toolbar to add it to your canvas:
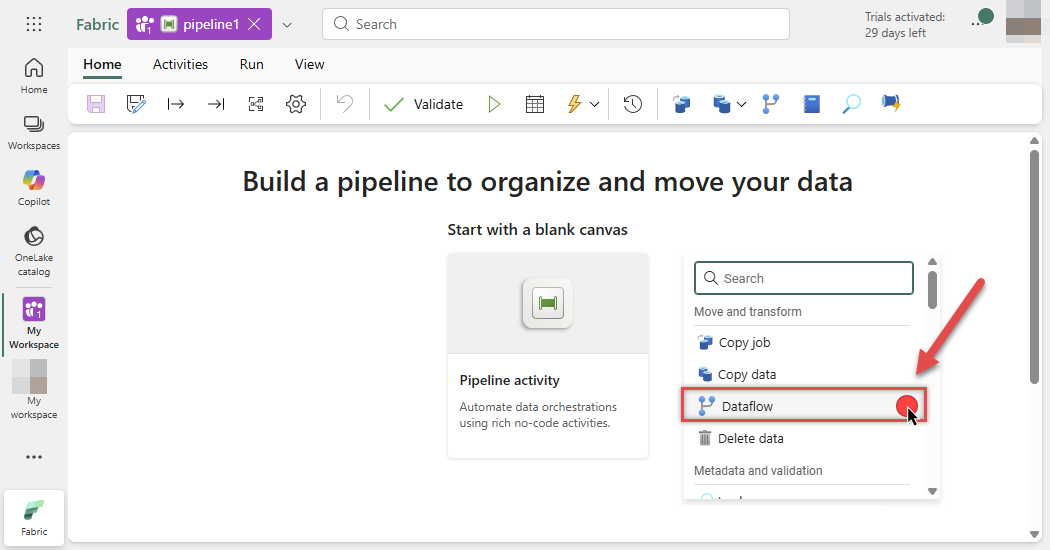
-
Select the Dataflow activity on the canvas and click the Settings tab. Choose your Workspace and the Dataflow you created in the previous steps:

-
You are now ready to link the Dataflow with other Pipeline activities.
-
Once the Pipeline flow is configured, click the Run button at the top, then click Save and run to execute the pipeline:

-
Monitor the Output tab below. The Pipeline status will initially show as In progress:
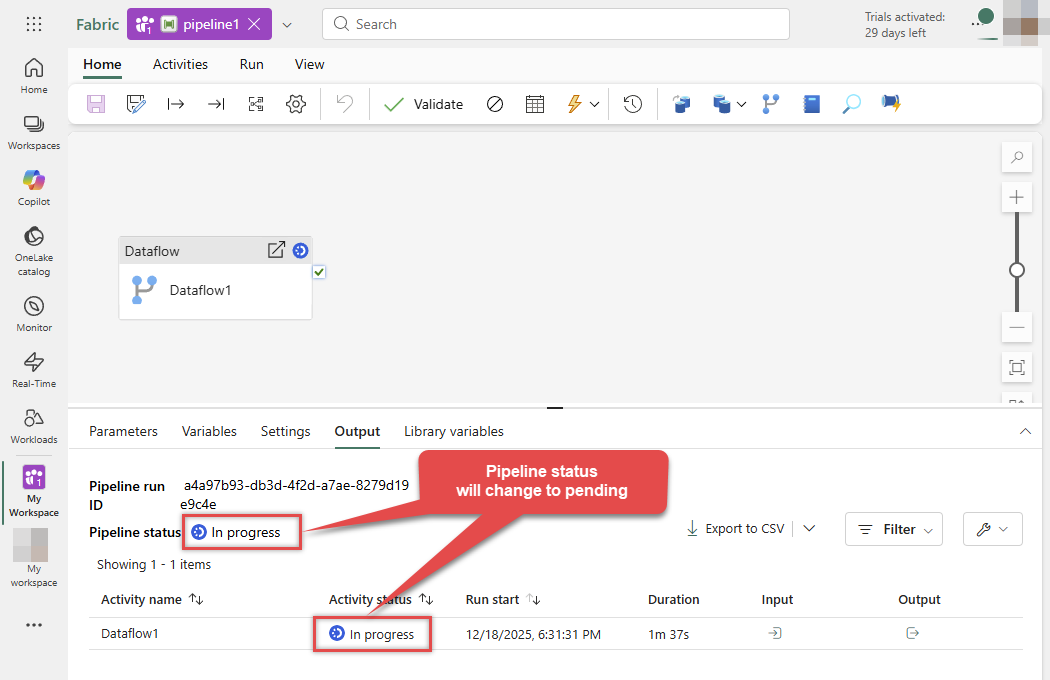
-
Wait for the process to complete. The status will update to Succeeded, indicating your data has been successfully loaded via the Dataflow:

-
Done! You can now start building reports on your new semantic model.
Azure DevOps Connector actions
Got a specific use case in mind? We've mapped out exactly how to perform a variety of essential Azure DevOps operations directly in Microsoft Fabric, so you don't have to figure out the setup from scratch. Check out the step-by-step guides below:
- Get Query Fileds
- Get Work Items for Specified Query Id
- Query Work Items
- Query Work Item Comments
- Get Work Item Comments (by WorkItem Id)
- Get Work Item Comment by Comment Id and Work Item Id
- Create Work Item Comment
- Update Work Item Comment
- Delete Work Item Comment
- Get Work Item Column Fields
- Get Work Items by Ids
- Get Work Item Types
- Create Work Item
- Update Work Item
- Delete Work Item
- Get List of Queries
- Get List of Projects
- Get Project Details
- Create Project
- Update Project
- Delete Project
- Get List of Teams
- Get Team Details
- Create Team
- Update Team
- Delete Team
- Search for Work Items by Text
- Get Team Members
- Get Team Iterations
- Get Team Iteration Capacities
- Make Generic REST API Request
- Make Generic REST API Request (Bulk Write)
Optional: Centralized data access via ZappySys Data Gateway
In some situations, you may need to provide Azure DevOps data access to multiple users or services. Configuring the data source on a Data Gateway creates a single, centralized connection point for this purpose.
This configuration provides two primary advantages:
-
Centralized data access
The data source is configured once on the gateway, eliminating the need to set it up individually on each user's machine or application. This significantly simplifies the management process.
-
Centralized access control
Since all connections route through the gateway, access can be governed or revoked from a single location for all users.
| Data Gateway |
Local ODBC
data source
|
|
|---|---|---|
| Simple configuration | ||
| Installation | Single machine | Per machine |
| Connectivity | Local and remote | Local only |
| Connections limit | Limited by License | Unlimited |
| Central data access | ||
| Central access control | ||
| More flexible cost |
To achieve this, you must first create a data source in the Data Gateway (server-side) and then create an ODBC data source in Microsoft Fabric (client-side) to connect to it.
Let's not wait and get going!
Create Azure DevOps data source in the gateway
In this section we will create a data source for Azure DevOps in the Data Gateway. Let's follow these steps to accomplish that:
-
Search for
gatewayin the Windows Start Menu and open ZappySys Data Gateway Configuration: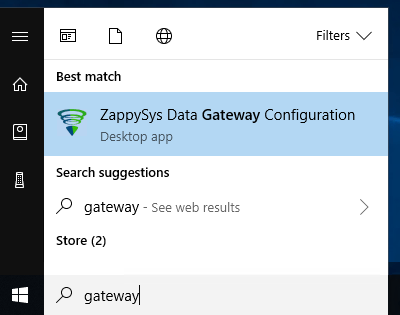
-
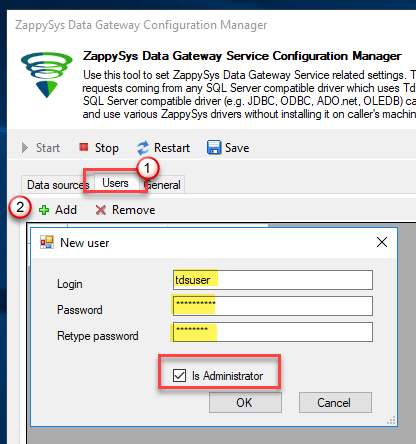
Go to the Users tab and follow these steps to add a Data Gateway user:
- Click the Add button
-
In the Login field enter a username, e.g.,
john - Then enter a Password
- Check the Is Administrator checkbox
- Click OK to save
-
Now we are ready to add a data source:
- Click the Add button
- Give the Data source a name (have it handy for later)
- Then select Native - ZappySys API Driver
- Finally, click OK
AzureDevopsDSNZappySys API Driver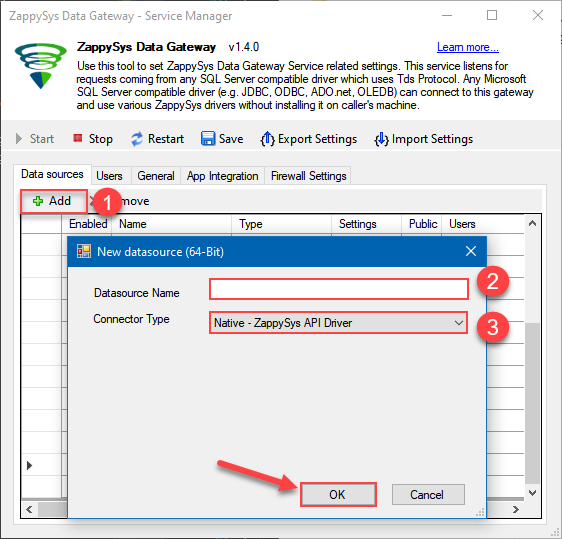
-
When the ZappySys API Driver configuration window opens, go back to ODBC Data Source Administrator where you already have the Azure DevOps ODBC data source created and configured, and follow these steps on how to Import data source configuration into the Gateway:
-
Open ODBC data source configuration and click Copy settings:
ZappySys API Driver - Azure DevOpsRead and write Azure DevOps (Cloud or On-Premises) data effortlessly. Integrate, manage, and automate work items, projects, and teams — almost no coding required.AzureDevopsDSN
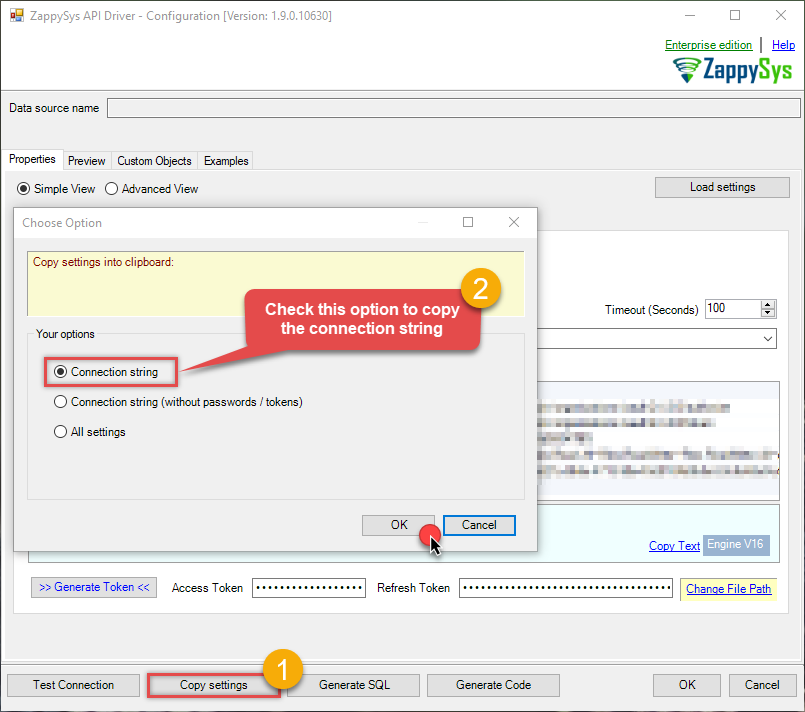
-
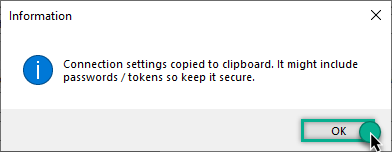
The window opens, telling us the connection string was successfully copied to the clipboard:
-
Then go to Data Gateway configuration and in data source configuration window click Load settings:
AzureDevopsDSNZappySys API Driver - Configuration [Version: 2.0.1.10418]ZappySys API Driver - Azure DevOpsRead and write Azure DevOps (Cloud or On-Premises) data effortlessly. Integrate, manage, and automate work items, projects, and teams — almost no coding required.AzureDevopsDSN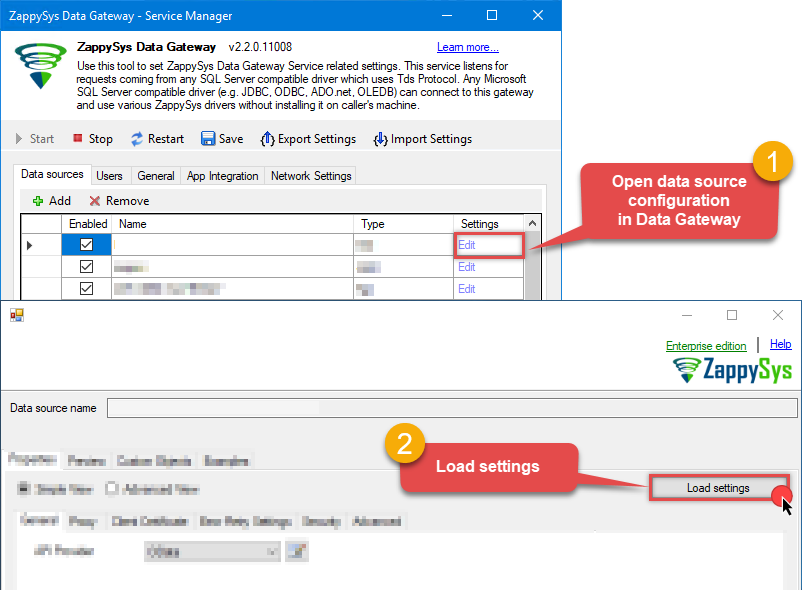
-
Once a window opens, just paste the settings by pressing
CTRL+Vor by clicking right mouse button and then Paste option.
-
Open ODBC data source configuration and click Copy settings:
-
Once done, go to the Network Settings tab and Add a firewall rule for inbound traffic:
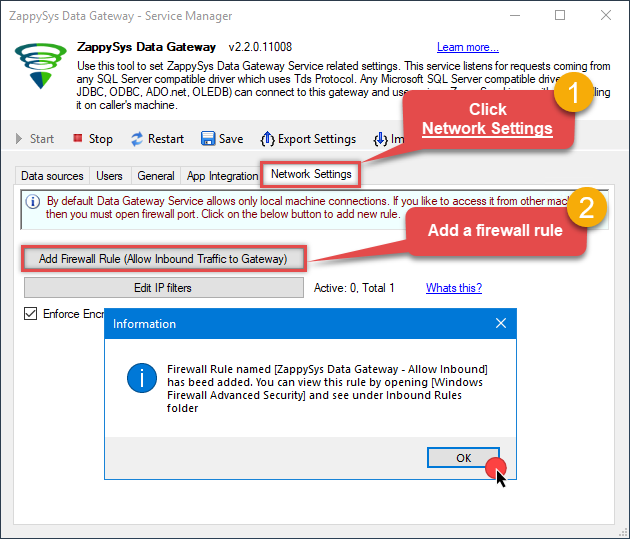
- This will initially allow all inbound traffic.
- Click Edit IP filters to restrict access to specific IP addresses or ranges.
-
Crucial Step: After creating or modifying the data source, you must:
- Click the Save button to persist your changes.
- Hit Yes when prompted to restart the Data Gateway service.
This ensures all changes are properly applied:
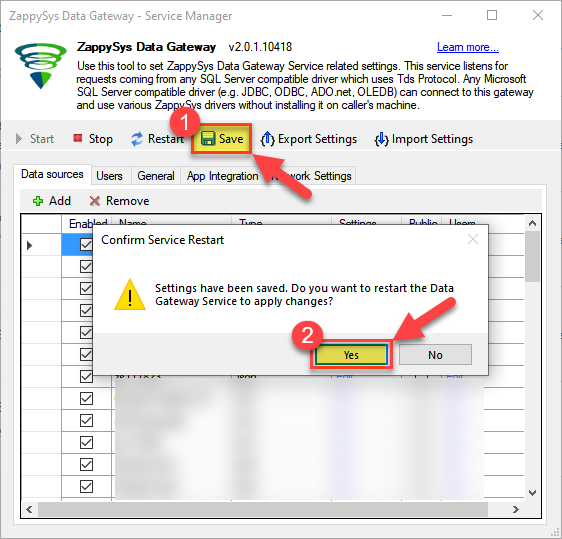 Skipping this step may cause the new settings to fail, preventing you from connecting to the data source.
Skipping this step may cause the new settings to fail, preventing you from connecting to the data source.
Create ODBC data source to connect to the gateway
In this part we will create an ODBC data source to connect to the ZappySys Data Gateway from Microsoft Fabric. To achieve that, let's perform these steps:
-
Search for
odbcand open the ODBC Data Sources (64-bit):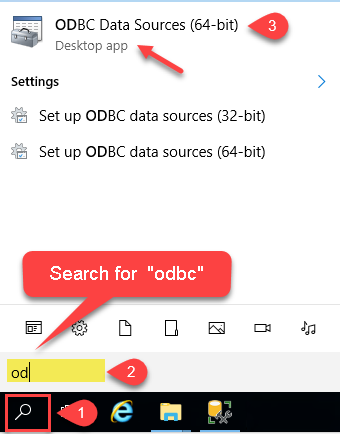
-
Create a User data source (User DSN) based on the ODBC Driver 17 for SQL Server driver:
ODBC Driver 17 for SQL Server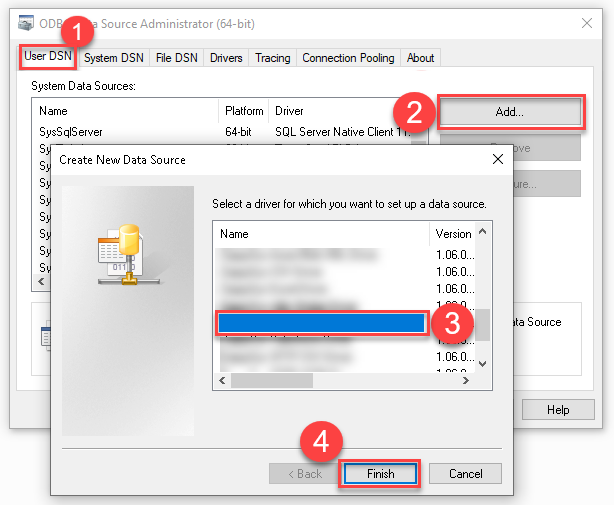 If you don't see the ODBC Driver 17 for SQL Server driver in the list, choose a similar version.
If you don't see the ODBC Driver 17 for SQL Server driver in the list, choose a similar version. -
Then set a Name for the data source (e.g.
Gateway) and the address of the Data Gateway:ZappySysGatewayDSNlocalhost,5000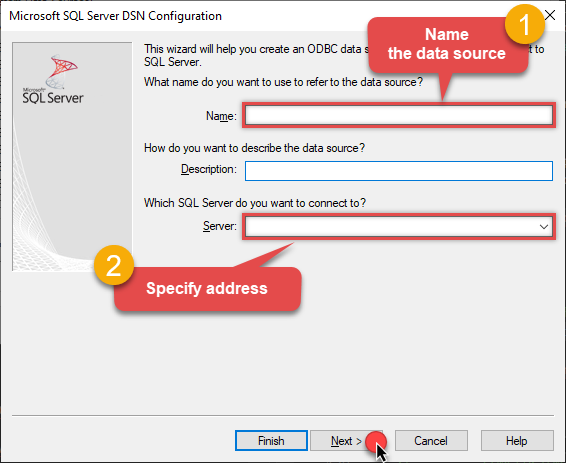 Make sure you separate the hostname and port with a comma, e.g.
Make sure you separate the hostname and port with a comma, e.g.localhost,5000. -
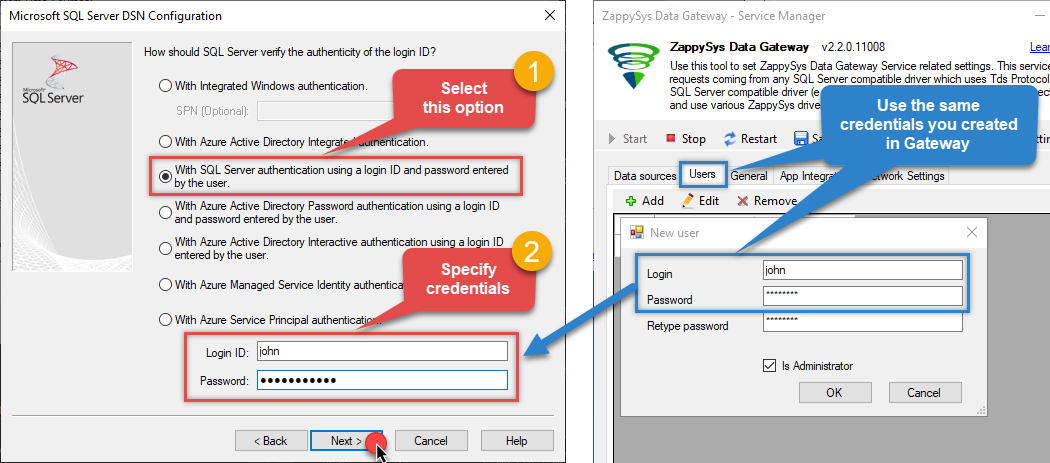
Proceed with the authentication part:
- Select SQL Server authentication
-
In the Login ID field enter the user name you created in the Data Gateway, e.g.,
john - Set Password to the one you configured in the Data Gateway
-
Then set the default database property to
AzureDevopsDSN(the one we used in the Data Gateway):AzureDevopsDSNAzureDevopsDSN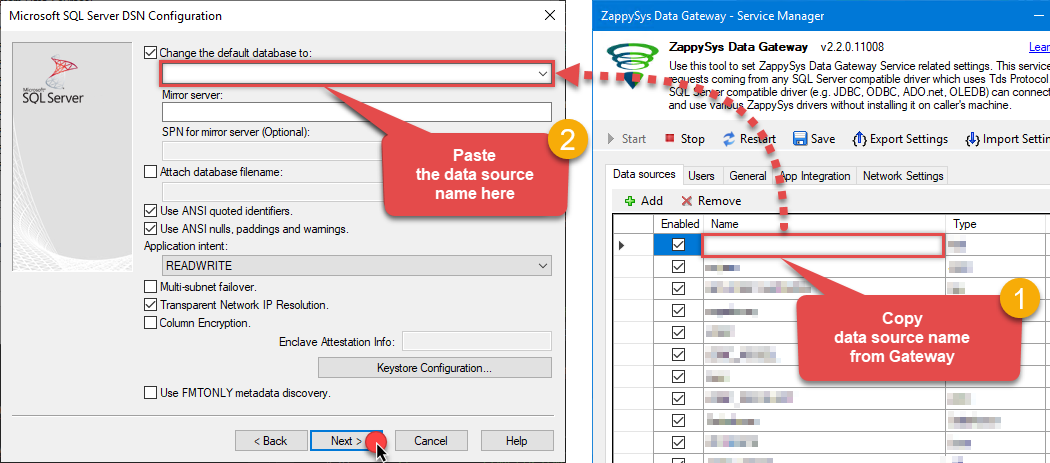 Make sure to type the data source name manually or copy/paste it directly into the field. Using the dropdown might fail because the Trust server certificate option is not enabled yet (next step).
Make sure to type the data source name manually or copy/paste it directly into the field. Using the dropdown might fail because the Trust server certificate option is not enabled yet (next step). -
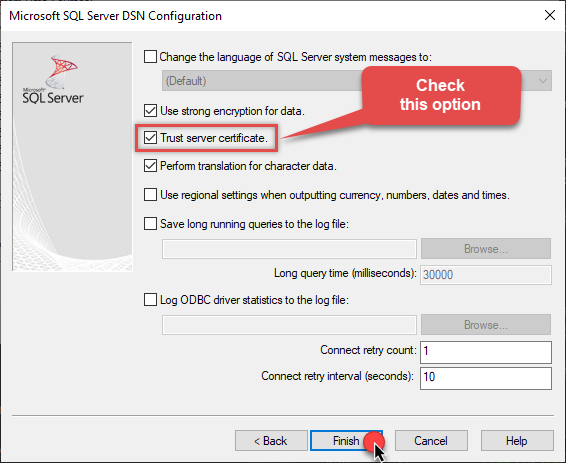
Continue by checking the Trust server certificate option:
-
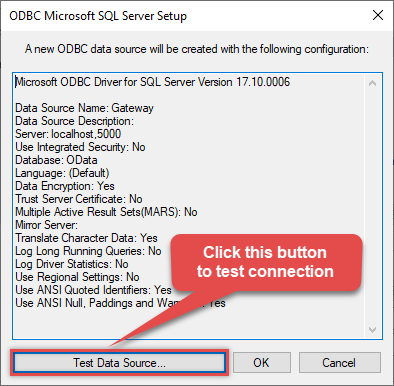
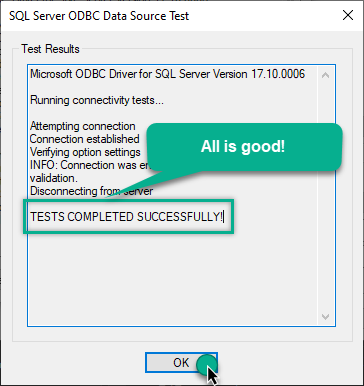
Once you do that, test the connection:
-
If the connection is successful, everything is good:
-
Done!
We are ready to move to the final step. Let's do it!
Access data in Microsoft Fabric via the gateway
Finally, we are ready to read data from Azure DevOps in Microsoft Fabric via the Data Gateway. Follow these final steps:
-
Go back to Microsoft Fabric.
-
Then, go to your Copy job or Dataflow and start configuring your ODBC data source (like you did in the previous step).
-
In the ODBC configuration window, configure these fields:
-
Enter your ODBC connection string (DSN format), for example:
DSN=ZappySysGatewayDSN - Expand Advanced options and set the SQL statement
-
Select
MyGatewayfrom the Data gateway dropdown that you configured in the previous step -
Select
Basicfrom the Authentication kind dropdown -
Enter the Username (e.g.,
john) and Password that you configured in ZappySys Data Gateway
DSN=ZappySysGatewayDSNSELECT * FROM WorkItems
DSN=ZappySysGatewayDSN
-
Enter your ODBC connection string (DSN format), for example:
-
Read the data the same way we discussed at the beginning of this article.
-
That's it!
Now you can connect to Azure DevOps data in Microsoft Fabric via the ZappySys Data Gateway.
Conclusion
In this guide, we demonstrated how to connect to Azure DevOps in Microsoft Fabric and integrate your data — all without writing complex code.
Ready to get started? Download ODBC PowerPack now or ping us via chat if you still need help: