Reading data in SSIS
In this section we will learn how to configure and use Azure DevOps Connector in API Source to extract data from Azure DevOps.
Video tutorial
This video covers following and more so watch carefully. After watching this video follow the steps described in this article.
- How to download SSIS PowerPack for Azure DevOps integration in SSIS
- How to configure connection for Azure DevOps
- How to read data from Azure DevOps
- Features about SSIS API Source
- Using Azure DevOps Connector in SSIS
Step-by-step instructions
-
Open Visual Studio and click Create a new project.
-
Select Integration Services Project. Enter a name and location for your project, then click OK.
-
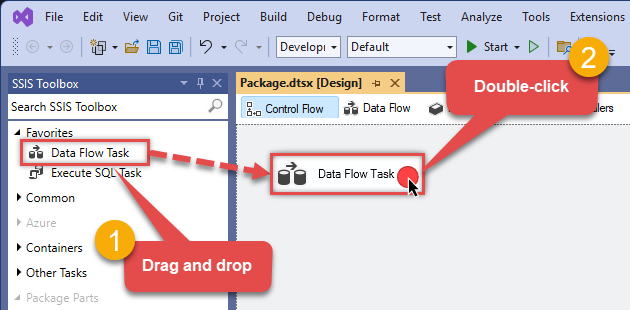
From the SSIS Toolbox, drag and drop a Data Flow Task onto the Control Flow surface, and double-click it:
-
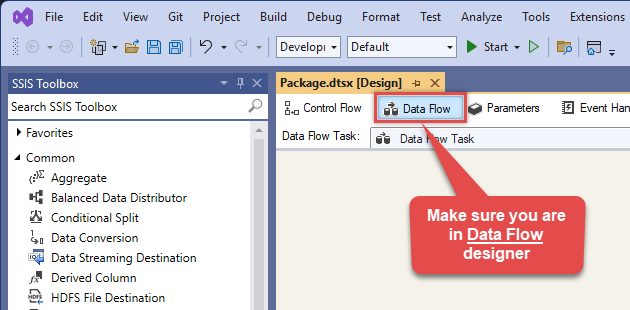
Make sure you are in the Data Flow Task designer:
-
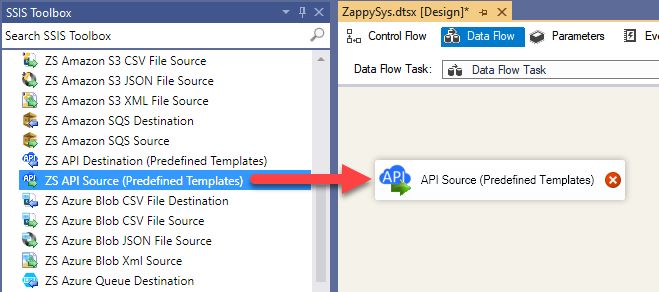
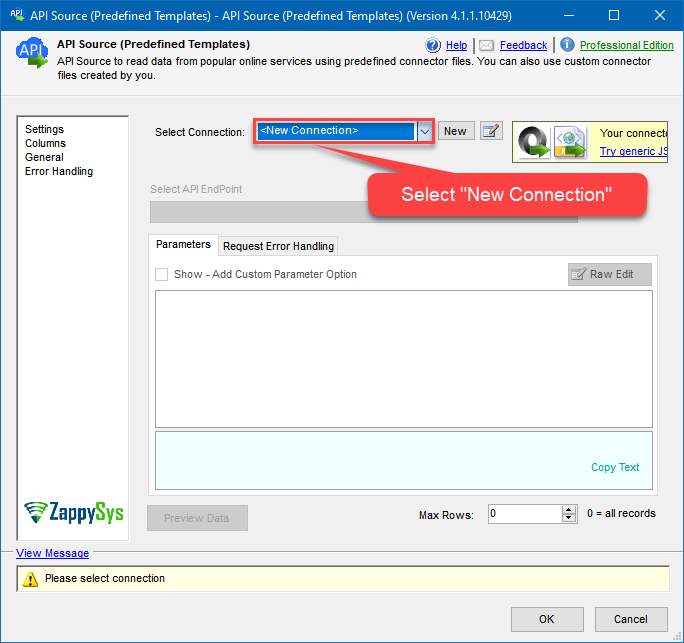
From the SSIS toolbox drag and API Source (Predefined Templates) on the data flow designer surface, and double click on it to edit it:
-
Select New Connection to create a new connection:
-
Use a preinstalled Azure DevOps Connector from Popular Connector List or press Search Online radio button to download Azure DevOps Connector. Once downloaded simply use it in the configuration:
Azure DevOps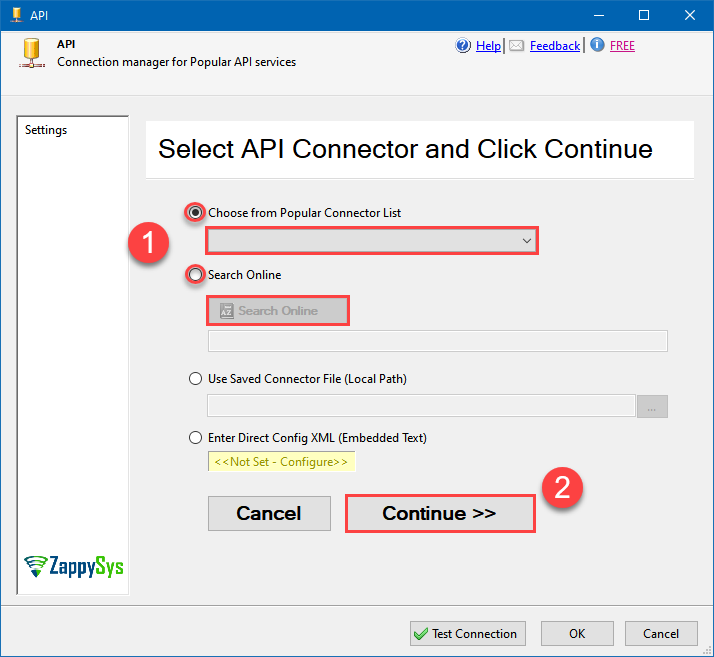
-
Select your authentication scenario below to expand connection configuration steps to:
- Configure the authentication in Azure DevOps.
- Enter those details into the API Connection Manager configuration.
User Credentials
Azure DevOps authentication
Delegated access using OAuth authorization code flow. Users sign in with their Azure AD account. [API reference]
Follow these simple steps below to create Microsoft Entra ID application with delegated access:
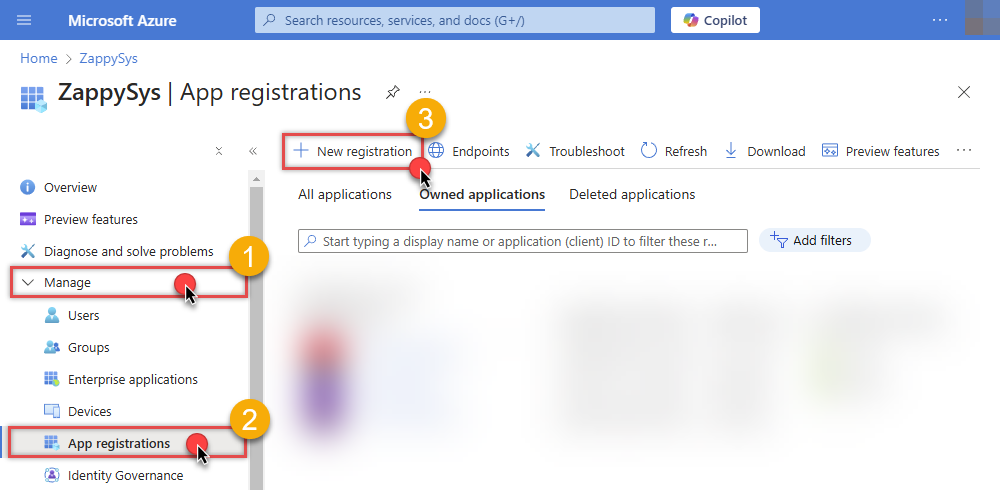
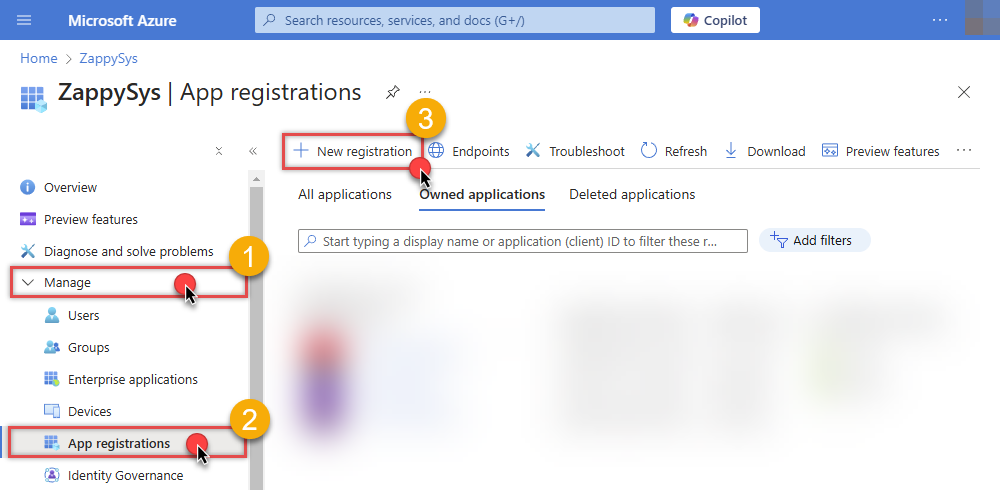
WARNING: To automate your company's processes, make sure you use a system/generic account (e.g.automation@my-company.com). When you use a personal account which is tied to a specific employee profile and that employee leaves the company, the token may become invalid and any automated processes using that token will start to fail.- Navigate to the Azure Portal and log in using your credentials.
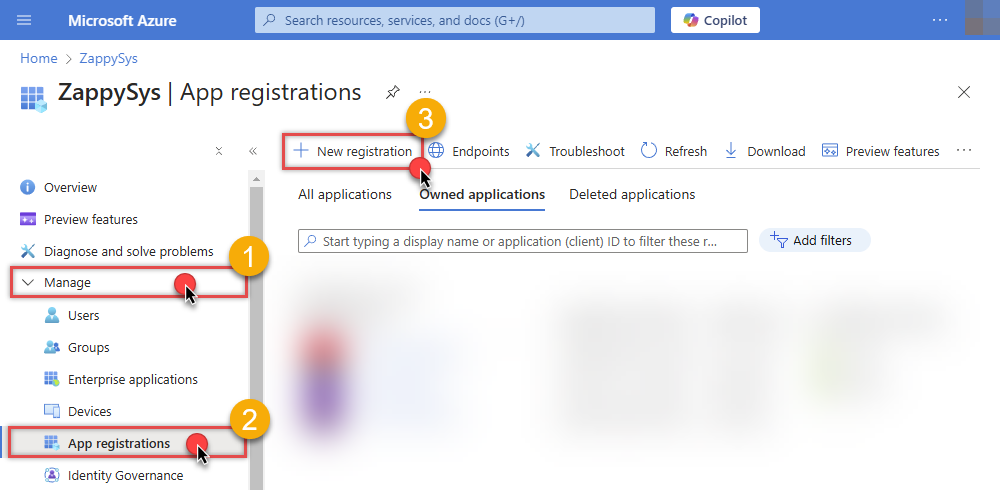
- Access Microsoft Entra ID.
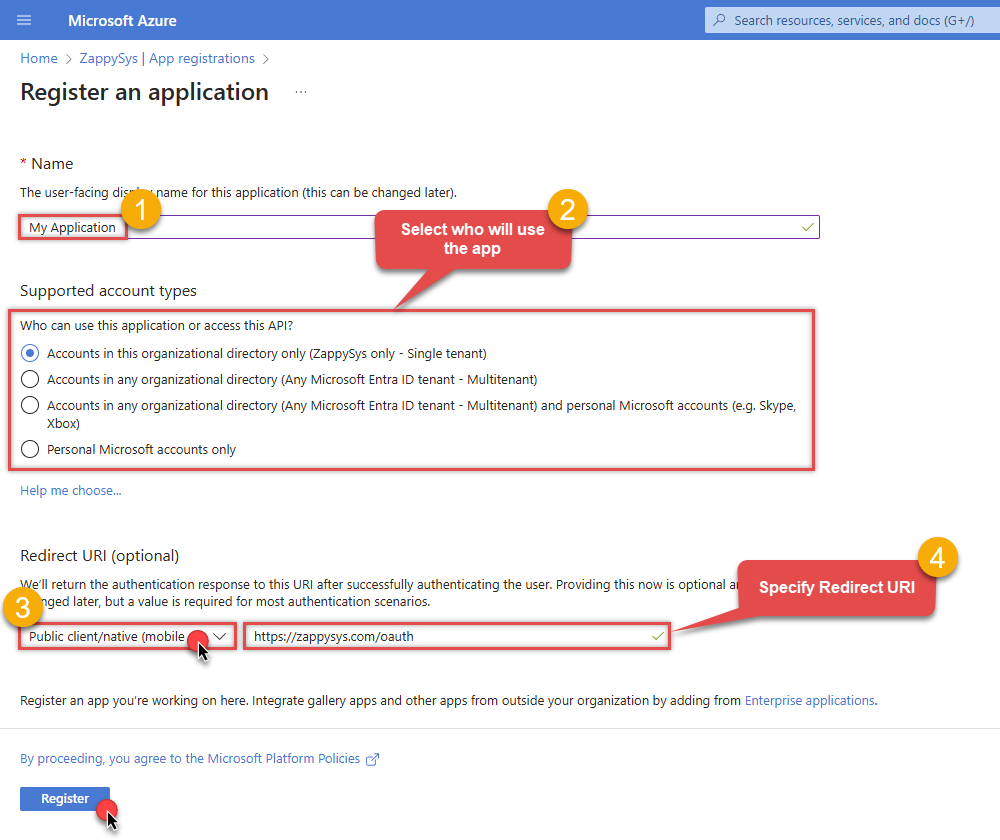
-
Register a new application by going to
App registrations
and clicking on New registration button:
 INFO: Find more information on how to register an application in Graph API reference.
INFO: Find more information on how to register an application in Graph API reference. -
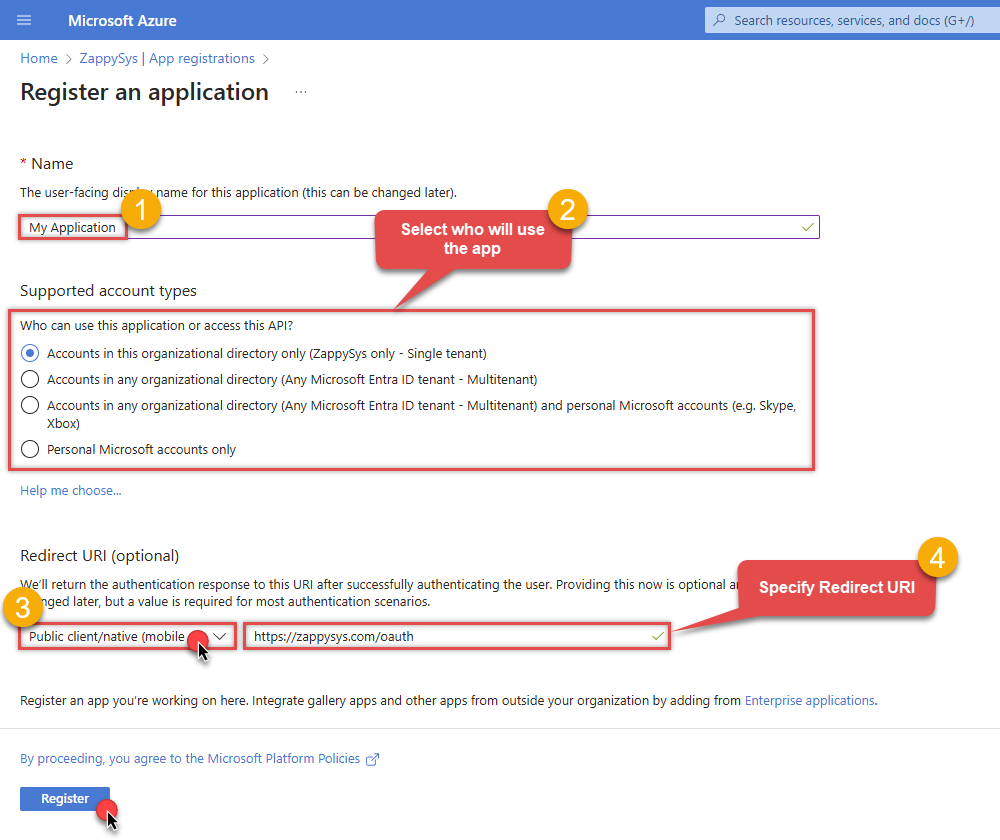
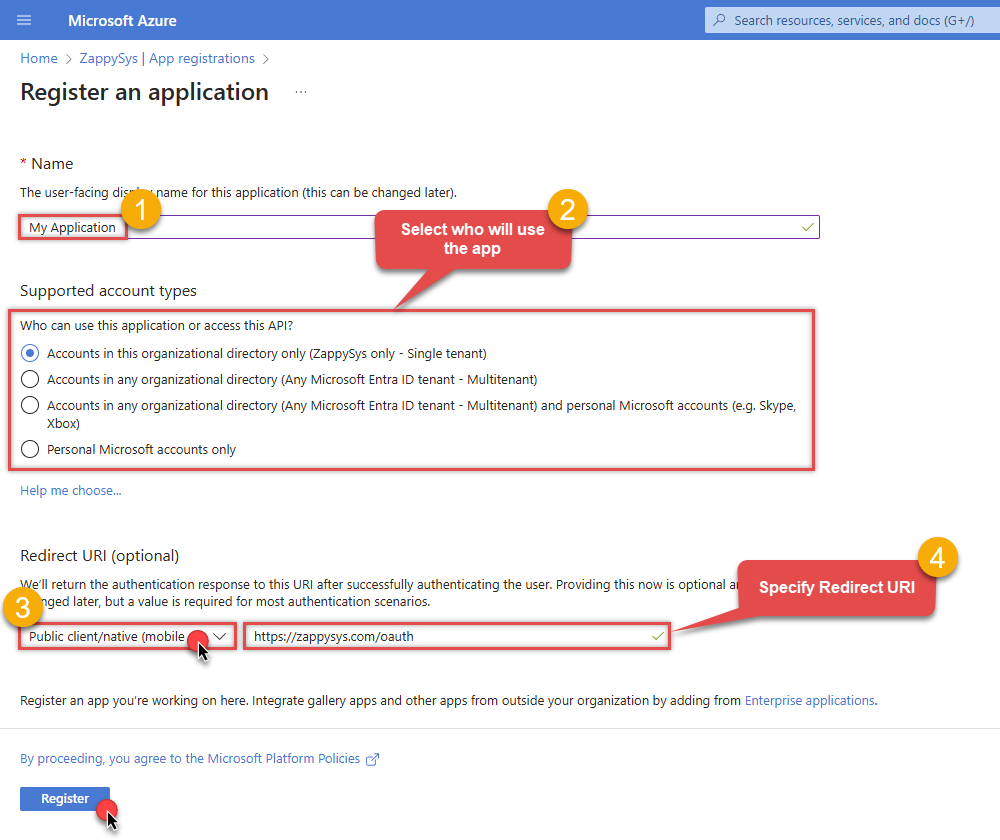
When configuration window opens, configure these fields:
-
Supported account type
- Use
Accounts in this organizational directory only, if you need access to data in your organization only.
- Use
-
Supported account type
-
Redirect URI:
- Set the type to
Public client/native (mobile & desktop). - Use
https://zappysys.com/oauthas the URL.
- Set the type to
-
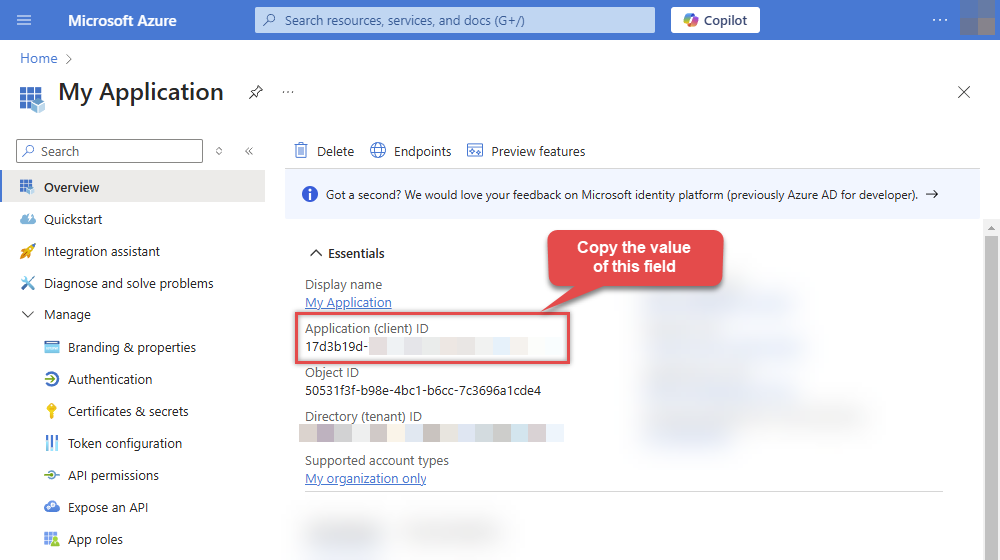
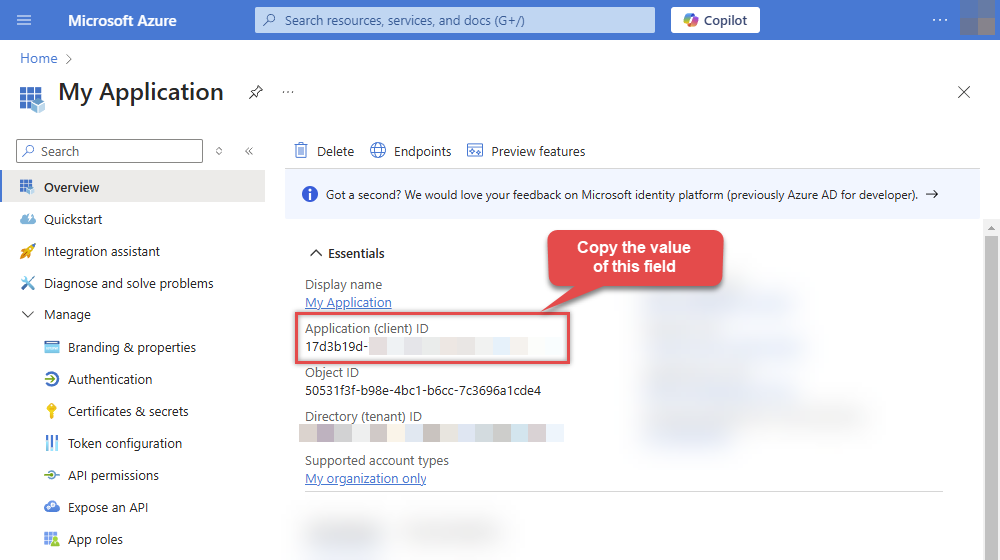
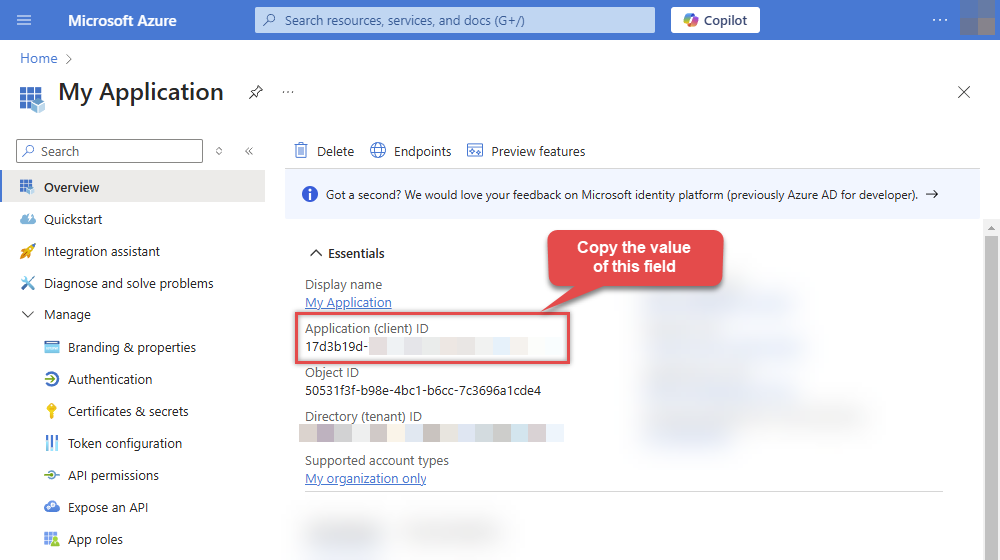
After registering the app, copy the Application (client) ID for later:
-
Then copy OAuth authorization endpoint (v2) & OAuth token endpoint (v2) URLs to use later in the configuration:
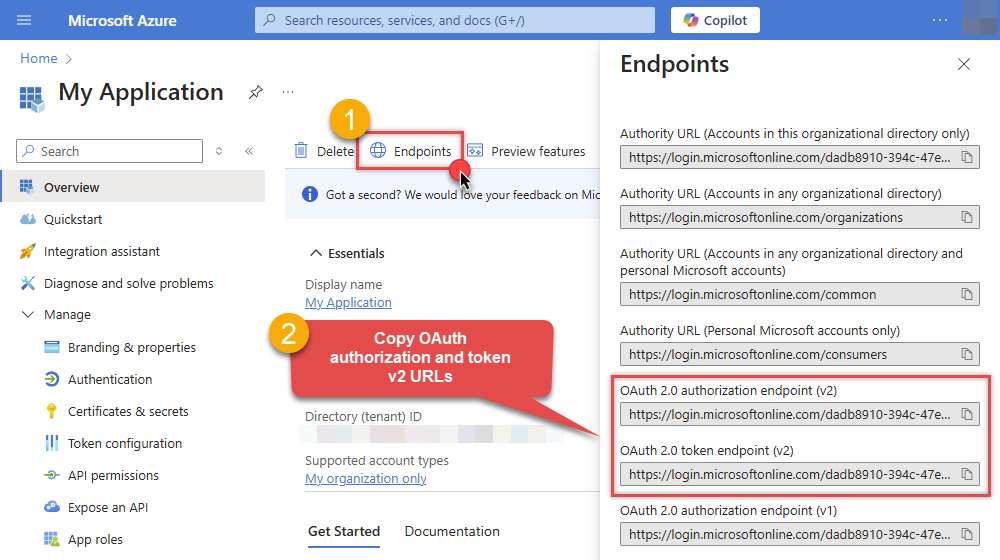
-
Now go to SSIS package or ODBC data source and use the copied values in User Credentials authentication configuration:
- In the Authorization URL field paste the OAuth authorization endpoint (v2) URL value you copied in the previous step.
- In the Token URL field paste the OAuth token endpoint (v2) URL value you copied in the previous step.
- In the Client ID field paste the Application (client) ID value you copied in the previous step.
-
In the Scope field use the default value or select individual scopes, e.g.:
-
vso.project -
vso.work_full
-
- Press Generate Token button to generate Access and Refresh Tokens.
- Optional step. Choose Default Drive Id from the drop down menu.
- Click Test Connection to confirm the connection is working.
- Done! Now you are ready to use the API Connector!
API Connection Manager configuration
Just perform these simple steps to finish authentication configuration:
-
Set Authentication Type to
User Credentials [OAuth] - Optional step. Modify API Base URL if needed (in most cases default will work).
- Fill in all the required parameters and set optional parameters if needed.
- Press Generate Token button to generate the tokens.
- Finally, hit OK button:
Azure DevOpsUser Credentials [OAuth]https://dev.azure.comRequired Parameters Authorization URL Fill-in the parameter... Token URL Fill-in the parameter... Client ID Fill-in the parameter... Organization name or Id (e.g. mycompany) Fill-in the parameter... Return URL Fill-in the parameter... Scopes (Must match with App Registration) Fill-in the parameter... API Version Fill-in the parameter... Optional Parameters Client Secret Refresh Token File Path Default Project Name (Choose after Generating Token) RetryMode RetryWhenStatusCodeMatch RetryStatusCodeList 429 RetryCountMax 5 RetryMultiplyWaitTime True 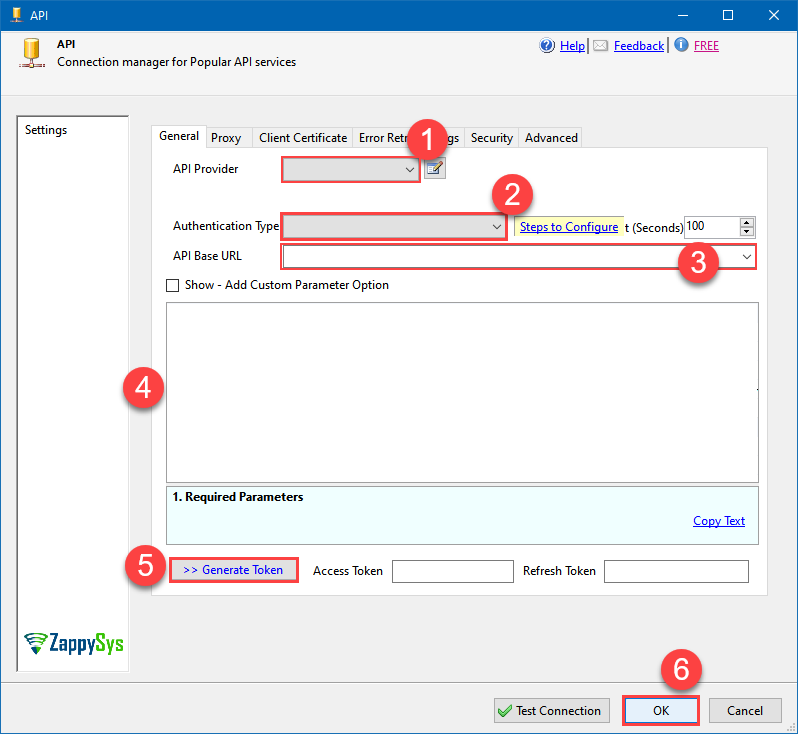 Find full details in the Azure DevOps Connector authentication reference.
Find full details in the Azure DevOps Connector authentication reference.Azure App Credentials
Azure DevOps authentication
Use Azure AD service principal credentials (client id + secret) with the client credentials flow. Recommended for automated server-to-server access instead of PAT or delegated OAuth. [API reference]
Step 1: Register the App in Microsoft Entra ID (AAD)
- Go to the Azure Portal > Microsoft Entra ID > App registrations and click New registration:
- Name it (e.g., ZS-AzureDevOps-AppCred).
- Set Supported account types to "Accounts in this organizational directory only" (Single Tenant):
- Leave Redirect URI blank (it's not used for Client Credentials).
- Click Register.
Step 2: Create a Client Secret
- In your new app, go to Certificates & secrets.
- Click New client secret, give it a name, and set an expiration.
- Copy the Secret Value immediately. You will never see it again once you leave the page:
Step 3: Set Permissions and Admin Consent
- Go to API permissions > Add a permission.
- Select Azure DevOps and click Delegated permissions.
- Check the necessary scopes (e.g.,
vso.project,vso.work_full). - Crucial: Click Grant admin consent for [Your Tenant]. Without this, the app cannot authenticate in the background.
Step 4: Map the App to Azure DevOps Organization
- Copy your Application (client) ID from the App Overview page.
- Go to your Azure DevOps Organization Settings > Users.
- Click Add users, paste the Application (client) ID in the search box, and select the App.
- Assign an Access level (usually Basic) and add it to the relevant Projects.
Step 5: Connection Settings
In your SSIS package or ODBC data source, use the following in the App Credentials configuration:
- In the Token URL field, paste the OAuth token endpoint (v2) URL from the Azure Portal 'Endpoints' tab.
- In the Client ID field, paste the Application (client) ID.
- In the Client Secret field, paste the Secret Value copied in Step 2.
- In the Scope field, use:
https://app.vssps.visualstudio.com/.default
Step 6: Finalize Connection
- Press Generate Token button to fetch the token using the Client Secret.
- Click Test Connection to confirm the setup.
- Done! You are ready to use the API Connector!
API Connection Manager configuration
Just perform these simple steps to finish authentication configuration:
-
Set Authentication Type to
Azure App Credentials [OAuth] - Optional step. Modify API Base URL if needed (in most cases default will work).
- Fill in all the required parameters and set optional parameters if needed.
- Finally, hit OK button:
Azure DevOpsAzure App Credentials [OAuth]https://dev.azure.comRequired Parameters Token URL Fill-in the parameter... Client ID Fill-in the parameter... Client Secret Fill-in the parameter... Scopes (Use .default for App Credentials) Fill-in the parameter... Organization name or Id Fill-in the parameter... API Version Fill-in the parameter... Optional Parameters Default Project Name RetryMode RetryWhenStatusCodeMatch RetryStatusCodeList 429 RetryCountMax 5 RetryMultiplyWaitTime True 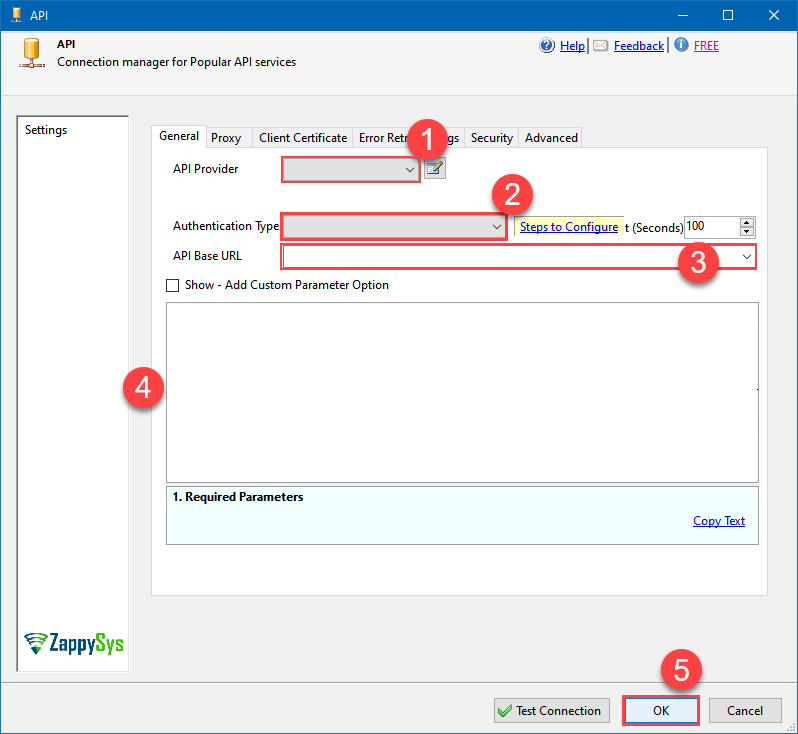 Find full details in the Azure DevOps Connector authentication reference.
Find full details in the Azure DevOps Connector authentication reference.Azure App Credentials with Certificate (Sign JWT with Private Key)
Azure DevOps authentication
Same as Application Credentials but uses a client certificate instead of a secret. [API reference]
Step 1: Register the App in Microsoft Entra ID (AAD)
- Go to the Azure Portal > Microsoft Entra ID > App registrations and click New registration:
- Name it (e.g., ZS-AzureDevOps-CertAuth).
- Set Supported account types to "Accounts in this organizational directory only" (Single Tenant):
- Leave Redirect URI blank (it's not used for Client Credentials flows).
- Click Register.
Step 2: Upload Client Certificate
- In your new app, go to Certificates & secrets.
- Click the Certificates tab, then click Upload certificate.
- Upload your public key certificate (.cer, .pem, or .crt). Keep the private key secure on your system.
- Copy the Thumbprint for your configuration:
Step 3: Set Permissions and Admin Consent
- Go to API permissions > Add a permission.
- Select Azure DevOps and click Delegated permissions.
- Select the required scopes (e.g.,
vso.project,vso.work_full). - Crucial: Click Grant admin consent for [Your Tenant]. Without this, the background service cannot acquire a token.
Step 4: Map the App to Azure DevOps Organization
- Copy your Application (client) ID from the App Overview page.
- Go to your Azure DevOps Organization Settings > Users.
- Click Add users and paste the Application (client) ID in the search box to find the App.
- Assign an Access level (usually Basic) and add it to the relevant Projects.
Step 5: Connection Settings
In your SSIS package or ODBC data source, use the following in the Client Certificate configuration:
- In the Token URL field, paste the OAuth token endpoint (v2) URL from the Azure Portal 'Endpoints' tab.
- In the Client ID field, paste the Application (client) ID.
- Configure your Certificate Path or Thumbprint in the Client Certificate tab of the connector.
- In the Scope field, use:
https://app.vssps.visualstudio.com/.default
Step 6: Finalize Connection
- Press Generate Token. The connector will sign the request using your certificate to fetch a token.
- Click Test Connection to confirm the setup.
- Done! Your certificate-based connection is ready!
API Connection Manager configuration
Just perform these simple steps to finish authentication configuration:
-
Set Authentication Type to
Azure App Credentials with Certificate (Sign JWT with Private Key) [OAuth] - Optional step. Modify API Base URL if needed (in most cases default will work).
- Fill in all the required parameters and set optional parameters if needed.
- Finally, hit OK button:
Azure DevOpsAzure App Credentials with Certificate (Sign JWT with Private Key) [OAuth]https://dev.azure.comRequired Parameters Token URL Fill-in the parameter... Client ID Fill-in the parameter... Certificate: *** Configure [Client Certificate] Tab *** Fill-in the parameter... Scopes (Must match with App Registration) Fill-in the parameter... Organization name or Id Fill-in the parameter... API Version Fill-in the parameter... Optional Parameters Default Project Name RetryMode RetryWhenStatusCodeMatch RetryStatusCodeList 429 RetryCountMax 5 RetryMultiplyWaitTime True 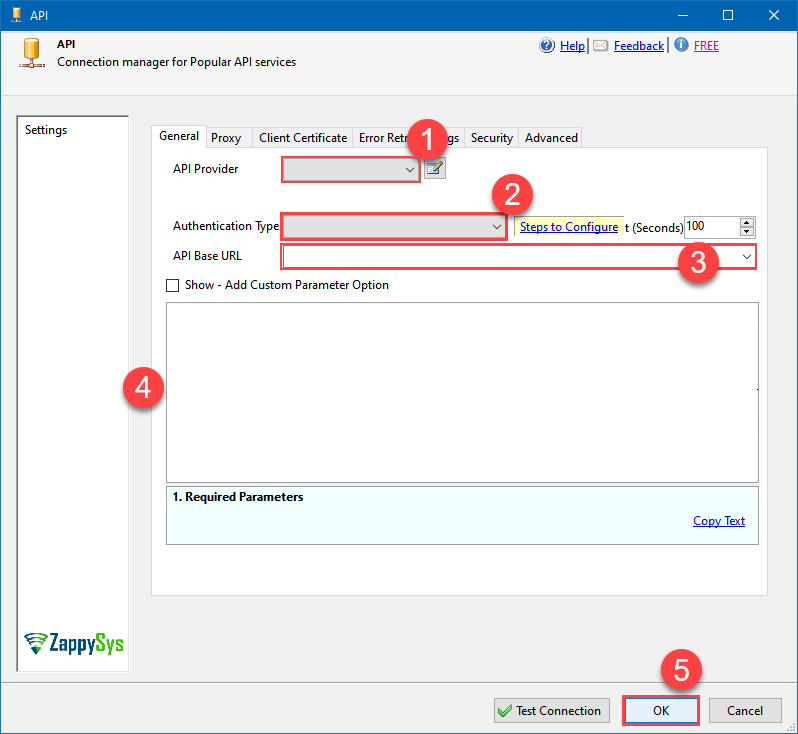 Find full details in the Azure DevOps Connector authentication reference.
Find full details in the Azure DevOps Connector authentication reference.(Cloud) OAuth App - User Credentials (DEPRECATED)
Azure DevOps authentication
**DEPRECATED:** this OAuth-based user credential flow is legacy; for new integrations prefer the Azure App Credentials options below. Connecting to your Azure DevOps data requires you to authenticate your REST API access. Follow the instructions below:- Go to https://app.vsaex.visualstudio.com/app/register to register your app.
-
Fill in your application and company's information as required, and then select the scopes that your application needs.
This should typically be Project and team (read and write) and Work items (read and write).
Your selected scopes when registering your app must match the scopes you enter here on the connector screen. If they don't match, the connector will not be able to work with your Azure DevOps account!If you need further information about the scopes used in Azure DevOps, or need to see what to enter into the connector screen to match up with your selected scopes, visit https://learn.microsoft.com/en-us/azure/devops/integrate/get-started/authentication/oauth?view=azure-devops.
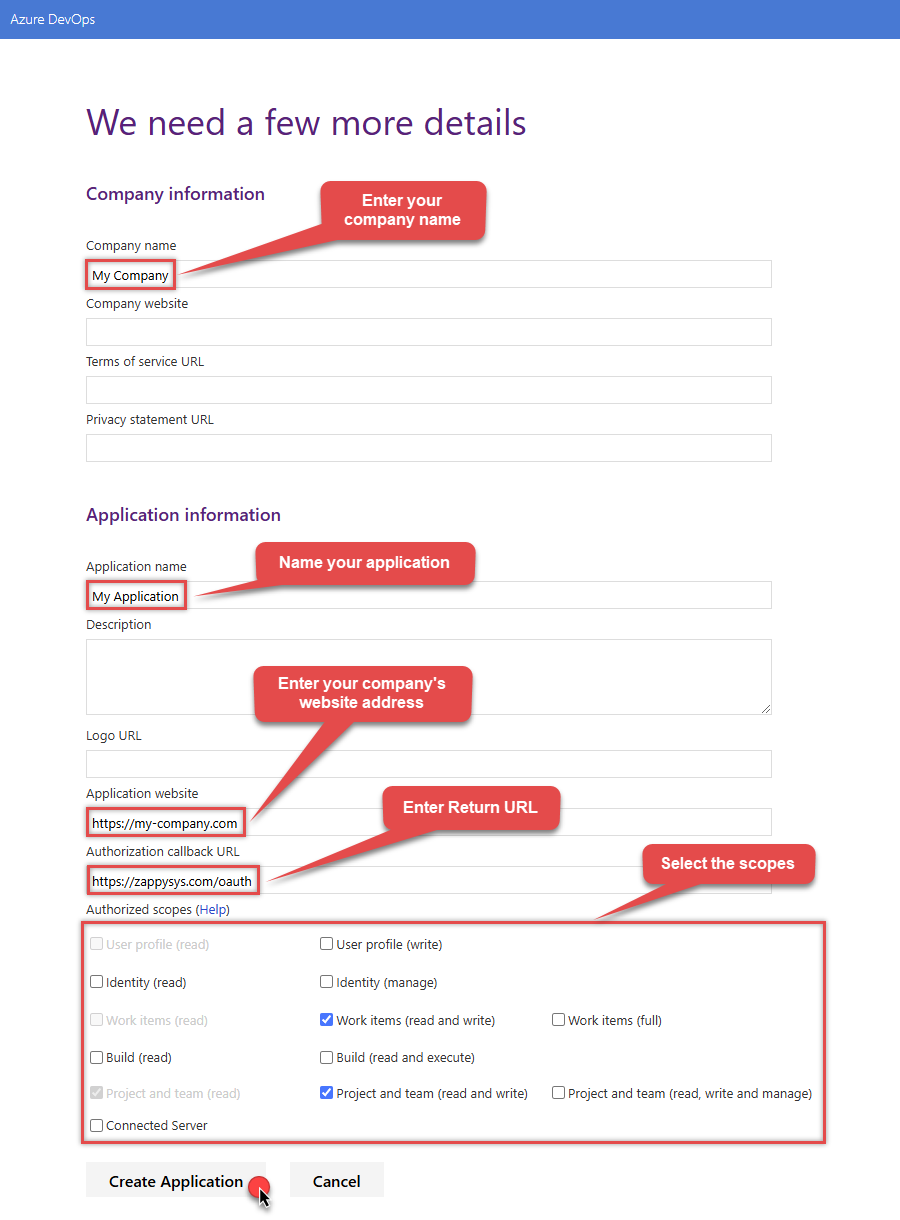
NOTE: For Authorization callback URL use your company's OAuth Redirect URL (if IT administrator provides you one) or you can use
https://zappysys.com/oauth(it's safe). - Select Create Application and then the Application Settings page will be displayed.
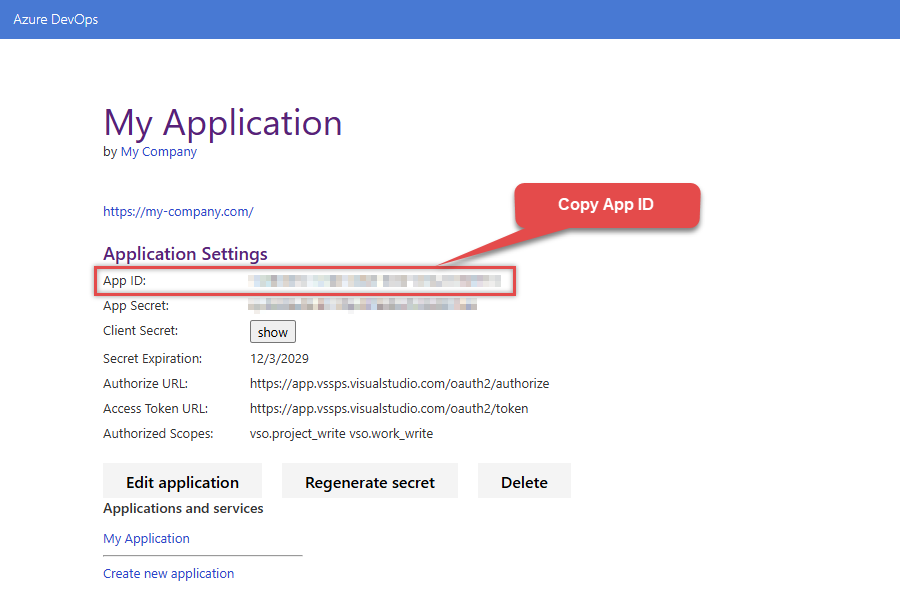
-
Record the App ID for us to use later:
-
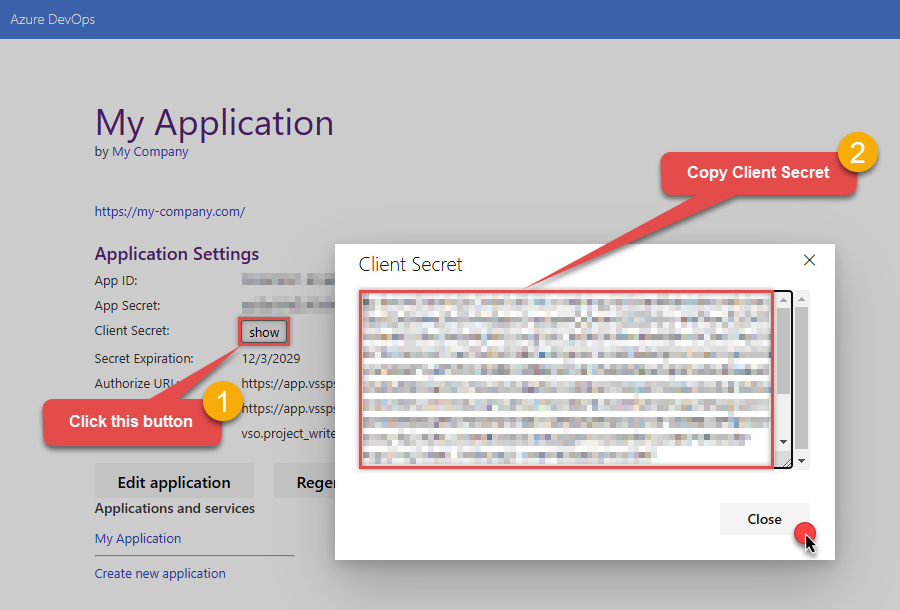
And do the same with Client Secret:
- Then go to https://aex.dev.azure.com and select relevant organization on the left.
-
Then copy Organization's host name part (e.g.
acmeinc, if full host name isacmeinc.visualstudio.com), save it to a file, and click it: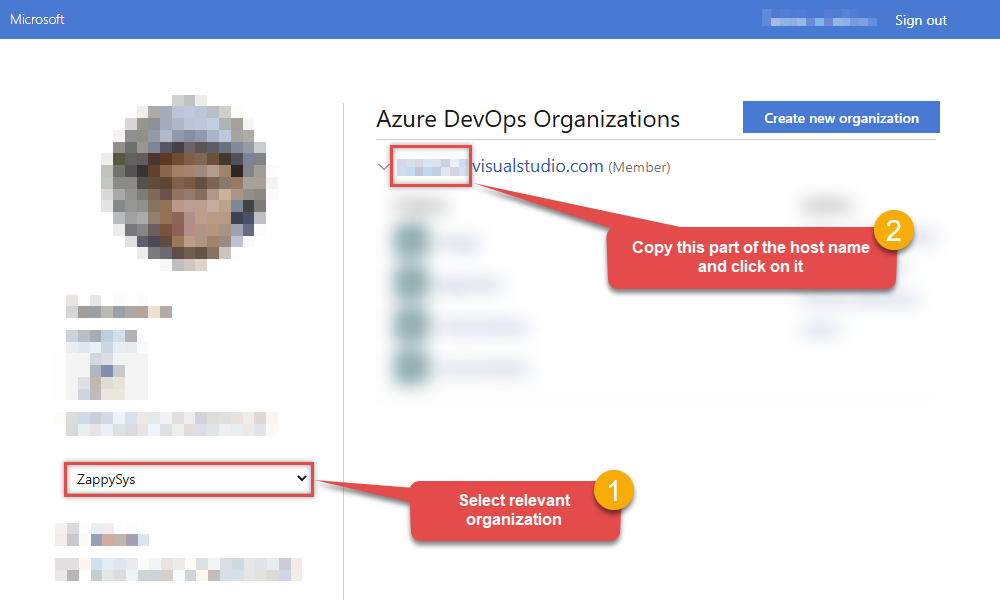
- Back at the connector screen, enter the App ID into the Client Id (App ID) field that was recorded in the previous step.
- Enter the Client Secret that was recorded in the previous step into the Client Secret field. In order to edit the text in this field, select the ellipses (...) button that appears when the textbox is clicked, and edit the Client Secret with the dialog box that appears.
- Enter the organization that was recorded in step 5 into the Organization name or Id for url field.
- Click Generate Token. If proper authentication occurs, you will see a notice saying so. You can click Yes to save a backup file of your generated tokens.
- Select the project you want to connect to by default from the Default Project (Choose after Generating Token) field.
- Select the Security tab.
-
Enter
https://auditservice.dev.azure.com,https://almsearch.dev.azure.cominto the Additional Trusted Domains field. - Select the Test Connection button at the bottom of the window to verify proper connectivity with your Azure DevOps account.
- If the connection test succeeds, select OK.
-
To edit previously created app you can visit
https://app.vsaex.visualstudio.com/meand see Applications and services section. Click on your desired app name.
API Connection Manager configuration
Just perform these simple steps to finish authentication configuration:
-
Set Authentication Type to
(Cloud) OAuth App - User Credentials (DEPRECATED) [OAuth] - Optional step. Modify API Base URL if needed (in most cases default will work).
- Fill in all the required parameters and set optional parameters if needed.
- Press Generate Token button to generate the tokens.
- Finally, hit OK button:
Azure DevOps(Cloud) OAuth App - User Credentials (DEPRECATED) [OAuth]https://dev.azure.comRequired Parameters Client Id (App ID) Fill-in the parameter... Client Secret Fill-in the parameter... Organization name or Id (e.g. mycompany) Fill-in the parameter... Return URL Fill-in the parameter... Scopes (Use .default for App Credentials) Fill-in the parameter... API Version Fill-in the parameter... Optional Parameters Default Project Name (Choose after Generating Token) RetryMode RetryWhenStatusCodeMatch RetryStatusCodeList 429 RetryCountMax 5 RetryMultiplyWaitTime True 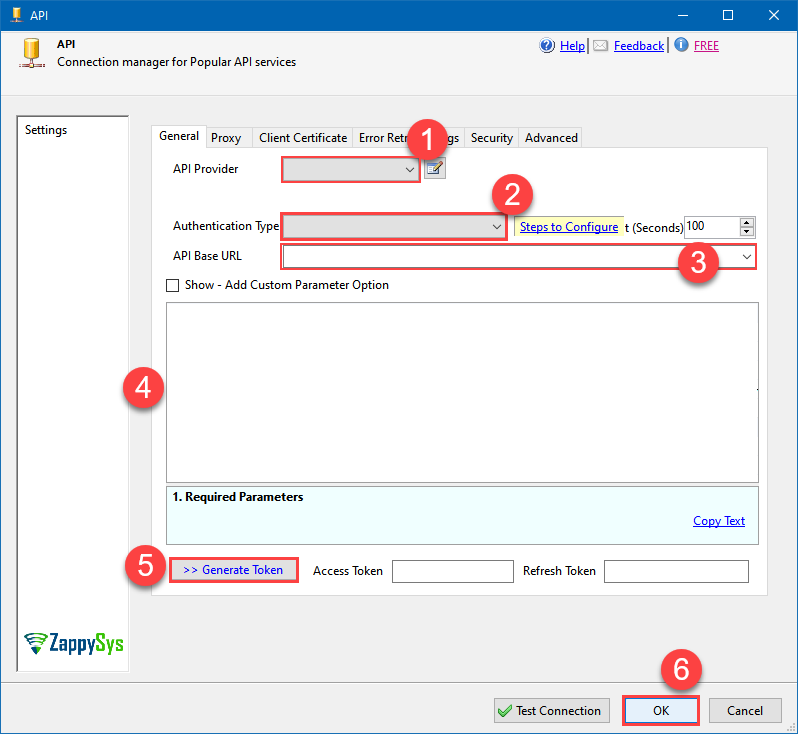 Find full details in the Azure DevOps Connector authentication reference.
Find full details in the Azure DevOps Connector authentication reference.(Cloud) Personal Access Token (PAT) (DEPRECATED)
Azure DevOps authentication
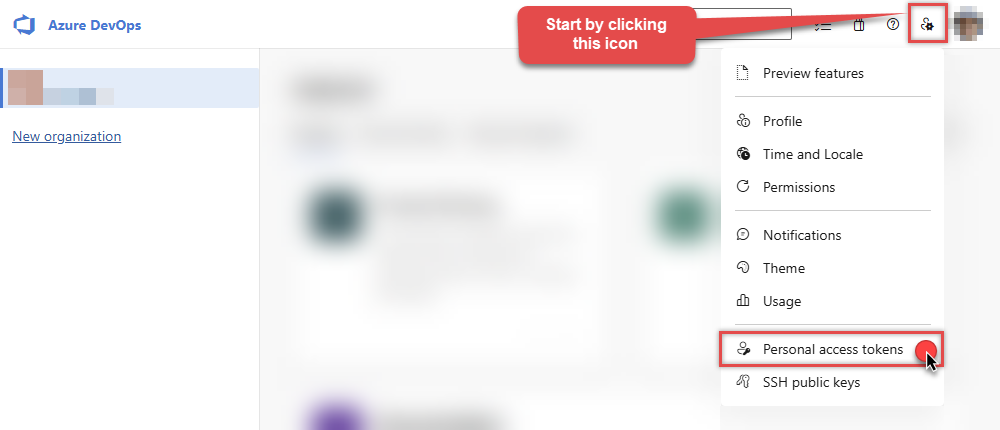
**DEPRECATED:** Personal Access Tokens are still supported but the new Azure App Credentials auth is recommended for security and automation. To connect to Azure DevOps using a Personal Access Token (PAT), you must first create a valid PAT:- Start by going to https://aex.dev.azure.com and selecting relevant organization on the left.
-
Then copy Organization's host name part (e.g.
acmeinc, if full host name isacmeinc.visualstudio.com), save it to a file, and click it: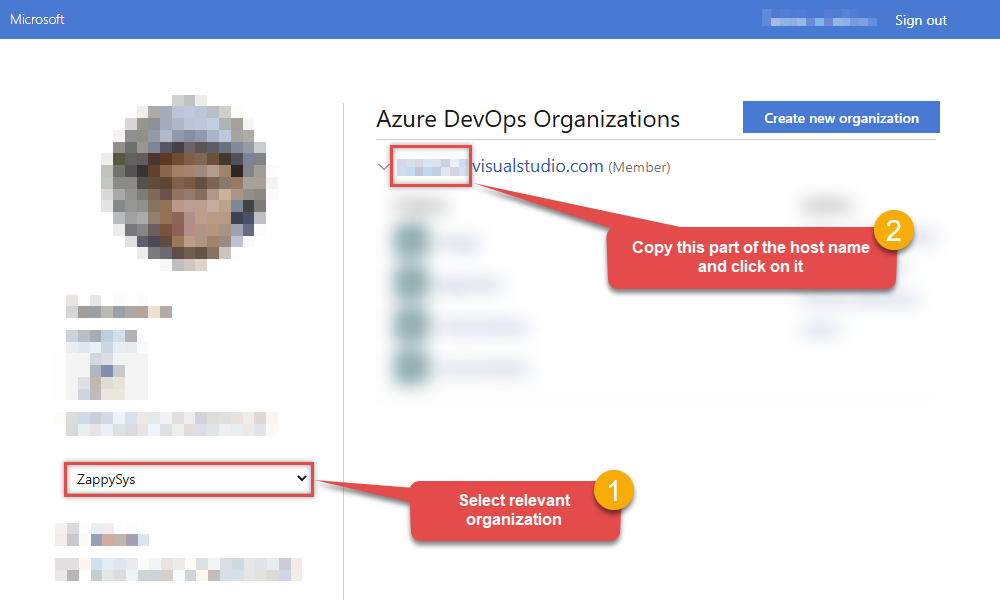
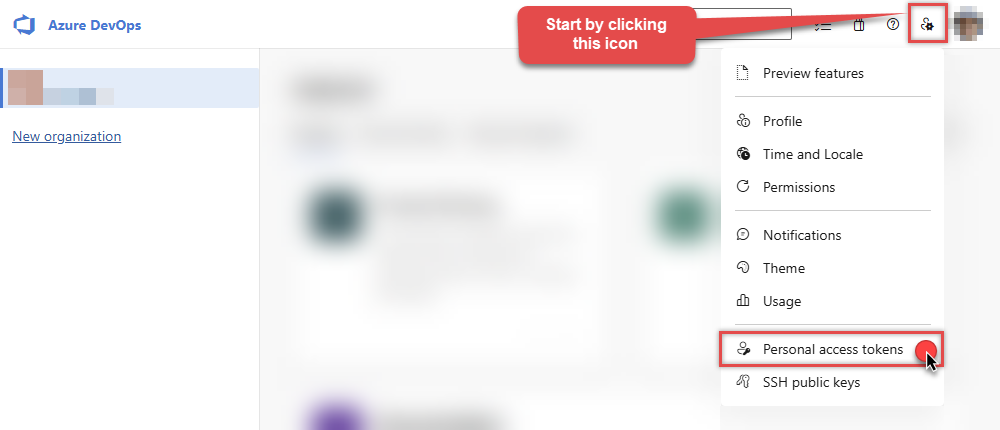
-
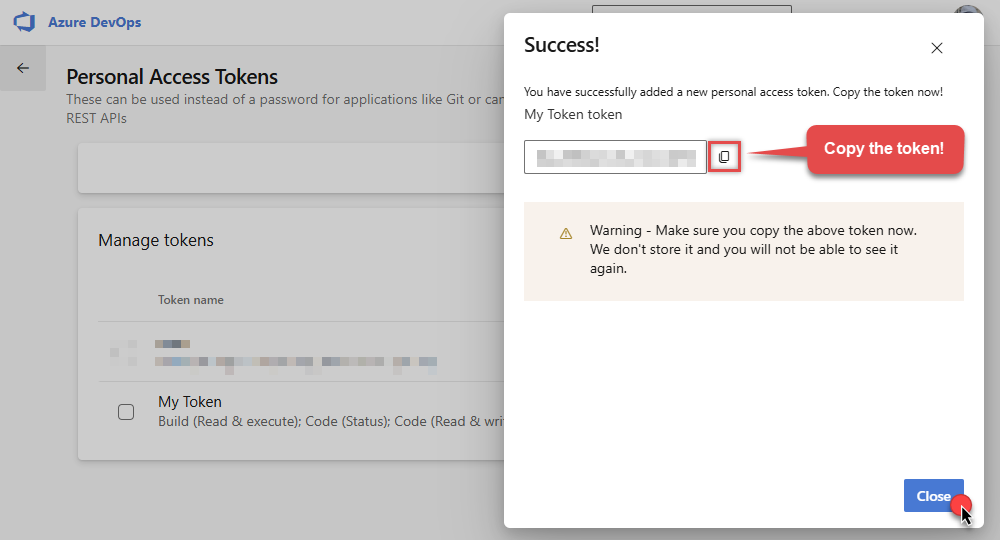
Next, click User settings icon and then click Personal access tokens:
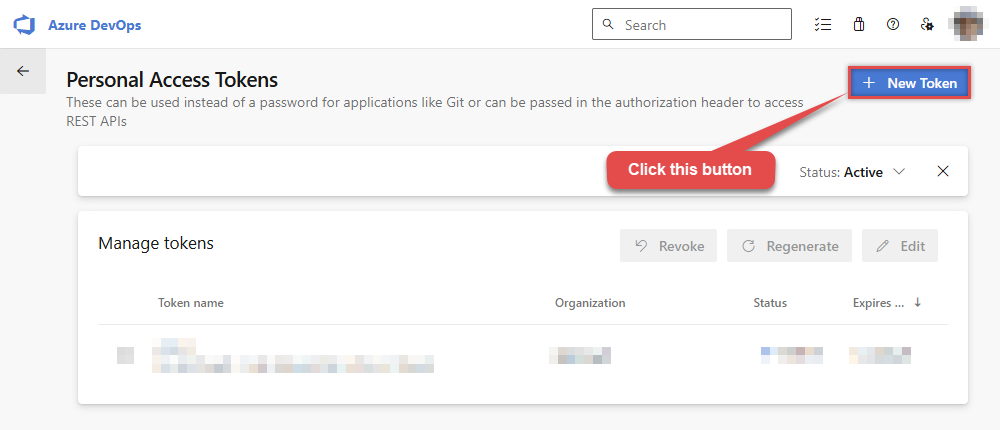
-
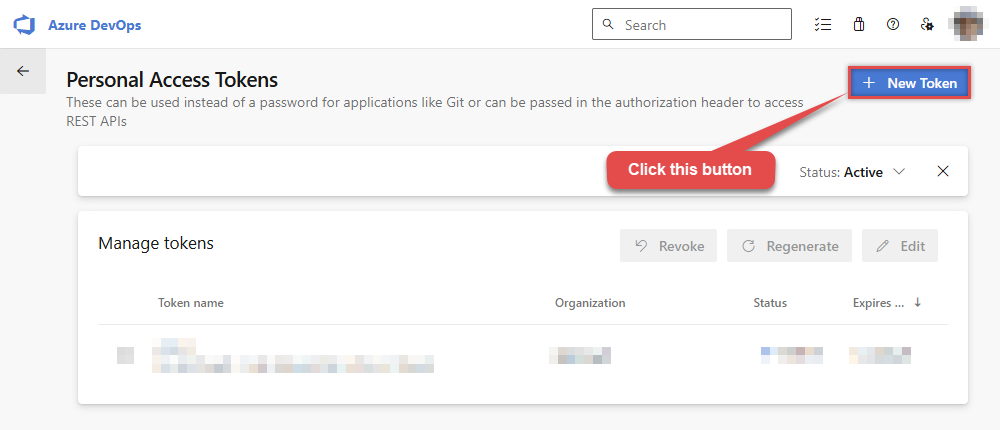
Then click New Token button to create a new personal access token:
-
Continue by...
- naming your token
- selecting the right Organization
- setting token's Expiration date (it's recommended to use
Custom definedoption and make it expire after one year or later) - and setting the Scopes:
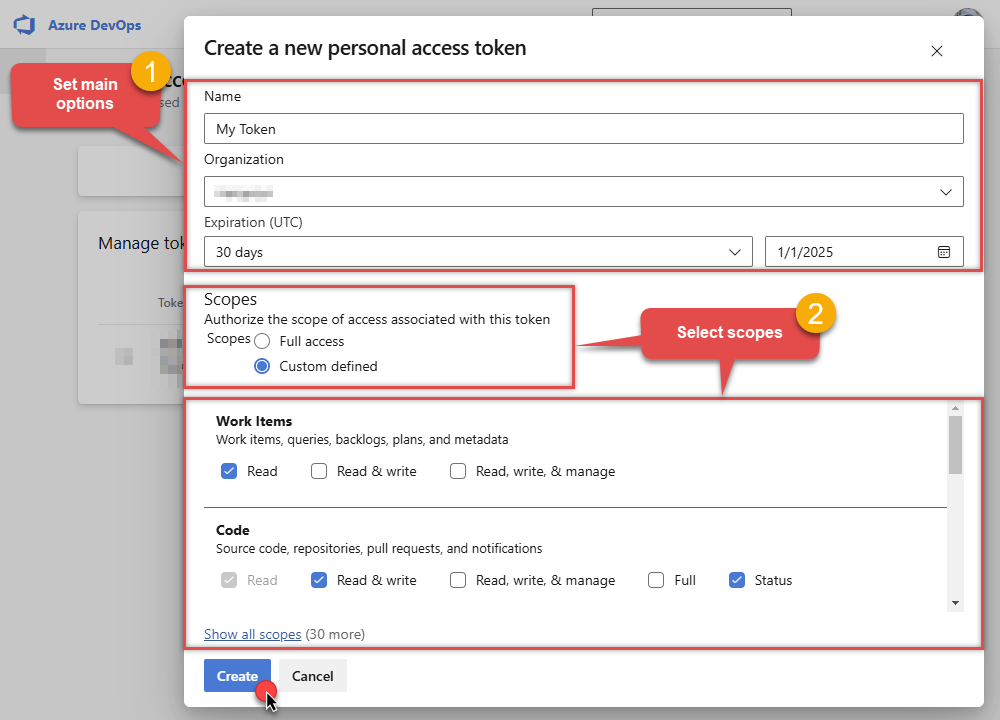
NOTE: You may be restricted from creating full-scoped PATs. If so, your Azure DevOps administrator in Azure AD has enabled a policy which limits you to a specific custom defined set of scopes.
-
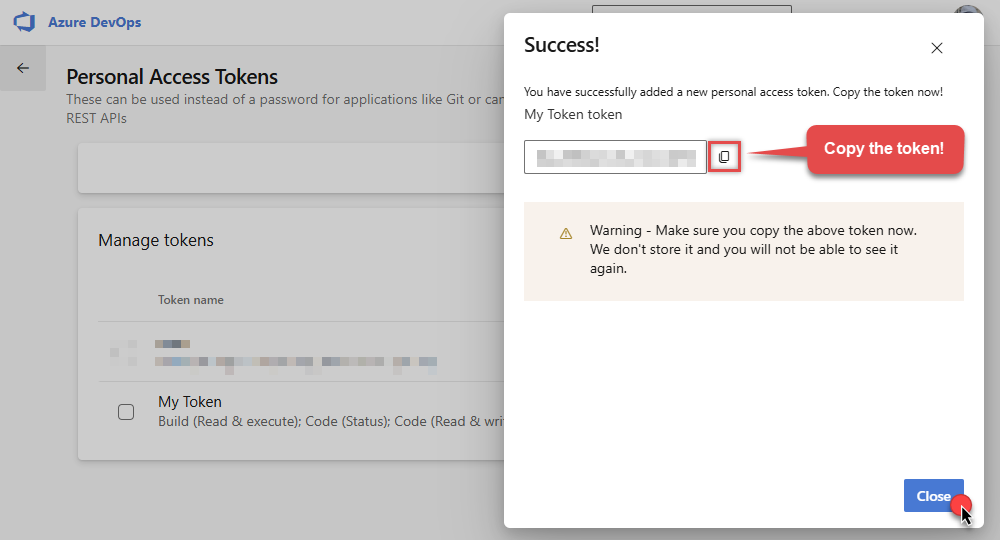
Now click Copy button and save the newly created token into a file for quick access later:
- Go back to the connector screen, input the token you saved in a previous step into the Personal Access Token (PAT) field.
- Then enter the Organization host name part that you noted recorded in previous step into Organization name or Id for url field.
- Enter the name or Id of the project you want to connect to by default in the Default Project (Choose after above fields) field.
- Select the Security tab.
- Enter
https://auditservice.dev.azure.com,https://almsearch.dev.azure.com,https://analytics.dev.azure.cominto the Additional Trusted Domains field. - Select the Test Connection button at the bottom of the window to verify proper connectivity with your Azure DevOps account.
- Done!
API Connection Manager configuration
Just perform these simple steps to finish authentication configuration:
-
Set Authentication Type to
(Cloud) Personal Access Token (PAT) (DEPRECATED) [Http] - Optional step. Modify API Base URL if needed (in most cases default will work).
- Fill in all the required parameters and set optional parameters if needed.
- Finally, hit OK button:
Azure DevOps(Cloud) Personal Access Token (PAT) (DEPRECATED) [Http]https://dev.azure.comRequired Parameters Personal Access Token (PAT) Fill-in the parameter... Organization name or Id for url Fill-in the parameter... API Version Fill-in the parameter... Optional Parameters AuthScheme Bearer AuthHeader Authorization Default Project Name RetryMode RetryWhenStatusCodeMatch RetryStatusCodeList 429 RetryCountMax 5 RetryMultiplyWaitTime True 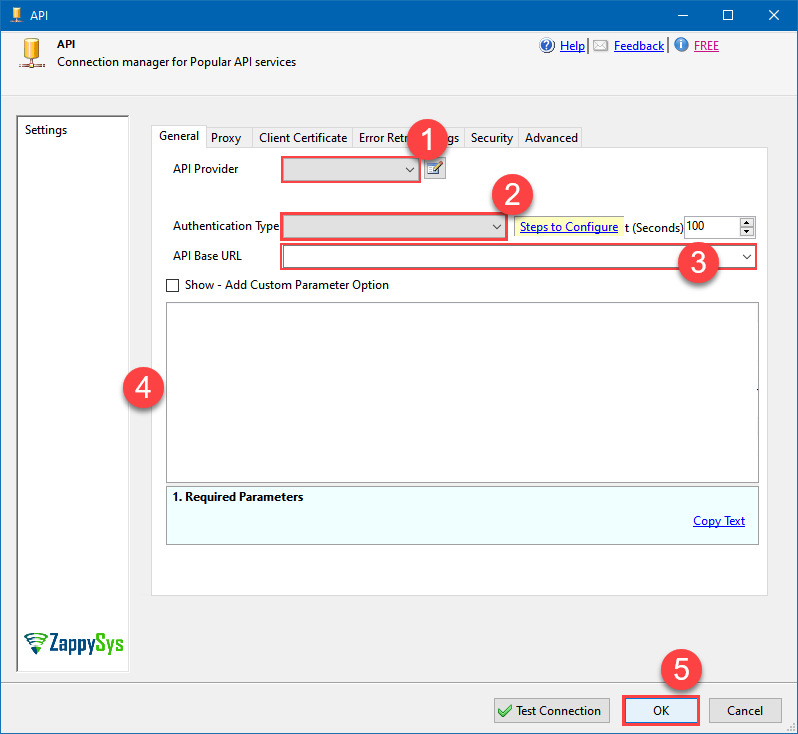 Find full details in the Azure DevOps Connector authentication reference.
Find full details in the Azure DevOps Connector authentication reference.(On-Premises) Personal Access Token (PAT) (DEPRECATED)
Azure DevOps authentication
**DEPRECATED:** On-premises PAT method is legacy; consider Azure App Credentials if your server supports Azure AD apps. To connect to Azure DevOps On-Premises Server using a Personal Access Token (PAT), you must first create a valid PAT:-
Start by navigating to your on-premises Azure DevOps Server URL.
NOTE: The screenshots shown below are from the cloud version, so your interface may look slightly different depending on which on-premises Azure DevOps Server version you’re using — however, the overall concepts and steps are very similar between the cloud and on-premises editions. -
Now open any project and capture Collection Name from the URL. For example if your URL is
https://tfs.mycompany.local/tfs/MyCollection/MyProject/
then your collection name is MyCollection usually after /tfs/. Copy this collection name and later we will enter on Connection UI. -
Next, click User settings icon and then click Personal access tokens:
-
Then click New Token button to create a new personal access token:
-
Continue by...
- naming your token
- selecting the right Organization
- setting token's Expiration date (it's recommended to use
Custom definedoption and make it expire after one year or later) - and setting the Scopes:
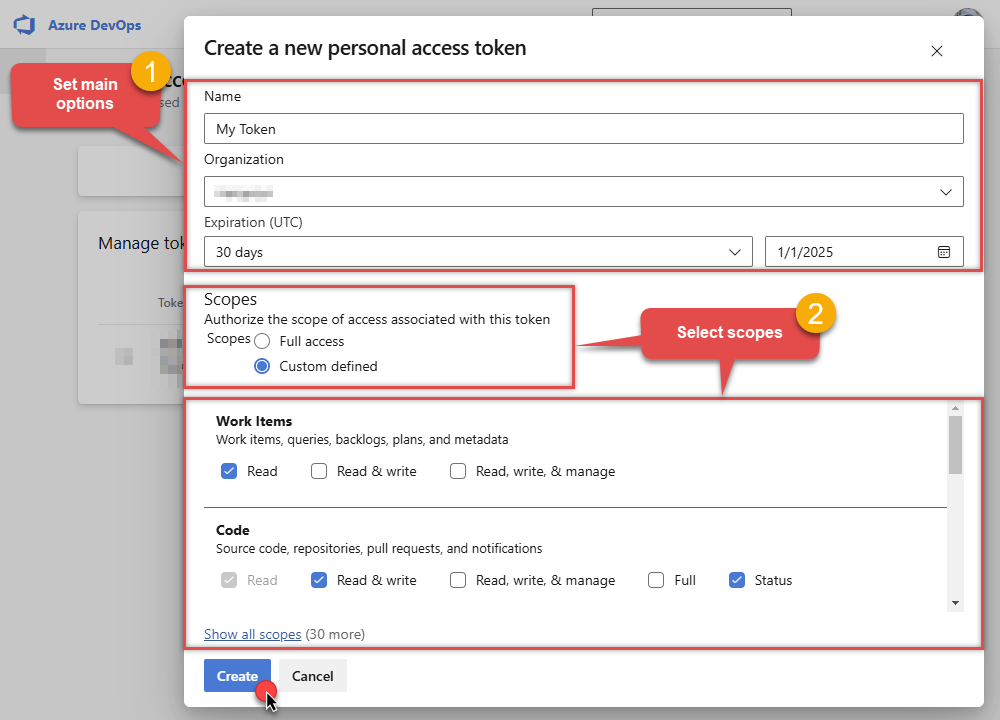
NOTE: You may be restricted from creating full-scoped PATs. If so, your Azure DevOps administrator in Azure AD has enabled a policy which limits you to a specific custom defined set of scopes.
-
Now click Copy button and save the newly created token into a file for quick access later:
- Go back to the connector screen, input the token you saved in a previous step into the Personal Access Token (PAT) field.
- Then enter the Organization host name part that you noted recorded in previous step into Organization name or Id for url field.
- Enter the name or Id of the project you want to connect to by default in the Default Project (Choose after above fields) field.
- Select the Security tab.
- Enter
https://auditservice.dev.azure.com,https://almsearch.dev.azure.com,https://analytics.dev.azure.cominto the Additional Trusted Domains field. - Select the Test Connection button at the bottom of the window to verify proper connectivity with your Azure DevOps account.
- Done!
API Connection Manager configuration
Just perform these simple steps to finish authentication configuration:
-
Set Authentication Type to
(On-Premises) Personal Access Token (PAT) (DEPRECATED) [Http] - Optional step. Modify API Base URL if needed (in most cases default will work).
- Fill in all the required parameters and set optional parameters if needed.
- Finally, hit OK button:
Azure DevOps(On-Premises) Personal Access Token (PAT) (DEPRECATED) [Http]https://dev.azure.comRequired Parameters Personal Access Token (PAT) Fill-in the parameter... Collection name (e.g. MyCollection) Fill-in the parameter... API Version Fill-in the parameter... Optional Parameters AuthScheme Bearer AuthHeader Authorization Default Project Name RetryMode RetryWhenStatusCodeMatch RetryStatusCodeList 429 RetryCountMax 5 RetryMultiplyWaitTime True 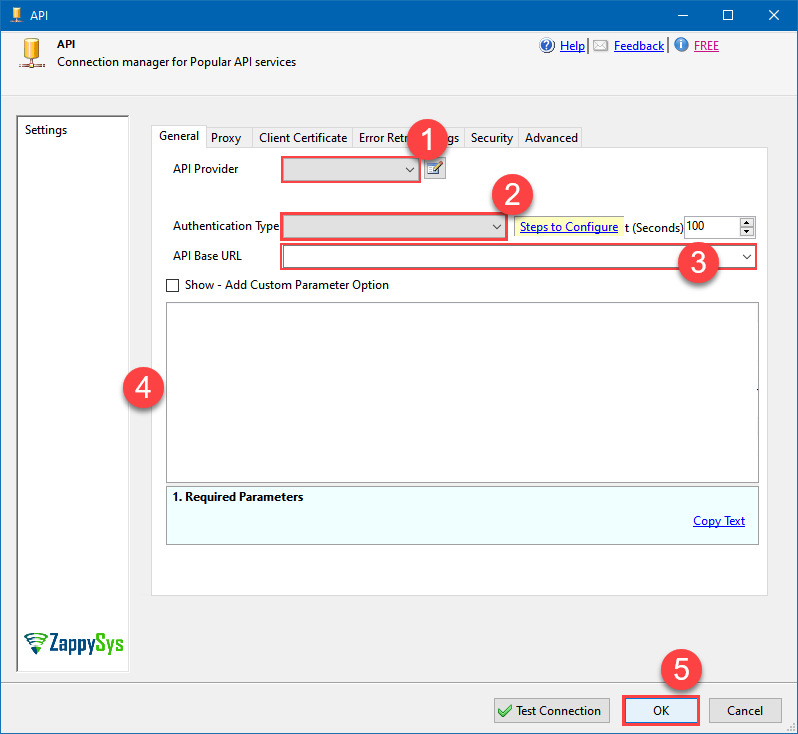 Find full details in the Azure DevOps Connector authentication reference.
Find full details in the Azure DevOps Connector authentication reference. -
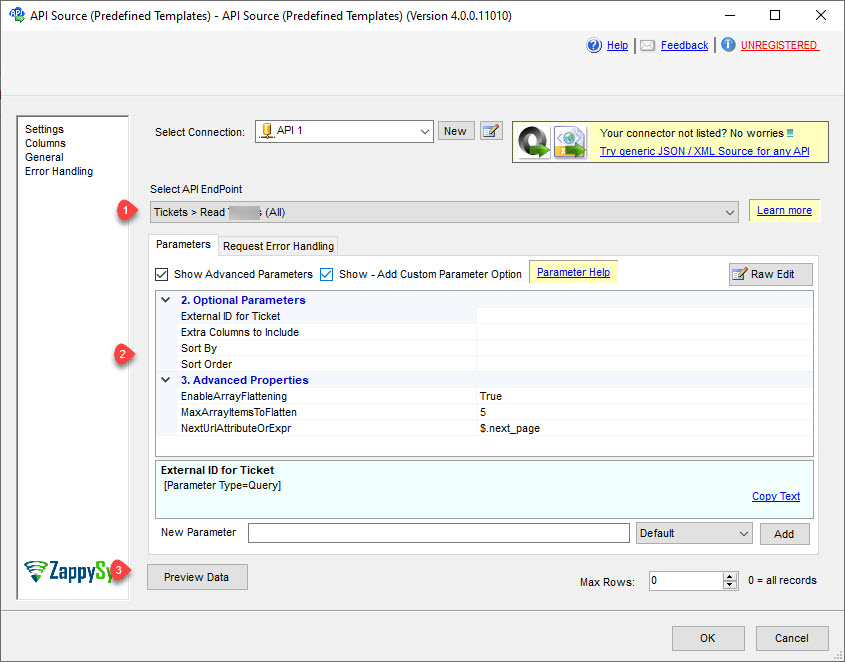
Select the desired endpoint, change/pass the properties values, and click on Preview Data button to make the API call.
API Source - Azure DevOpsRead and write Azure DevOps (Cloud or On-Premises) data effortlessly. Integrate, manage, and automate work items, projects, and teams — almost no coding required.
-
That's it! We are done! Just in a few clicks we configured the call to Azure DevOps using Azure DevOps Connector.
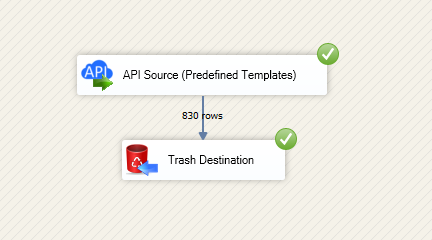
You can load the source data into your desired destination using the Upsert Destination , which supports SQL Server, PostgreSQL, and Amazon Redshift. We also offer other destinations such as CSV , Excel , Azure Table , Salesforce , and more . You can check out our SSIS PowerPack Tasks and components for more options. (*loaded in Trash Destination)