Authentication Application Credentials with Certificate (Sign JWT with Private Key)
Description
Instructions
Follow these simple steps to create Microsoft Entra ID application with application access permissions:
- Create an OAuth app
- Configure App Permissions
- Create Public/Private Key Pair
- Upload Public Key
- Configure ZappySys Connection for Private Key use
-
Grant granular permissions (optional)
This step allows to grant OAuth application granular permissions, i.e. access configured specificSites,Lists, andList Items.Step-1: Create OAuth app
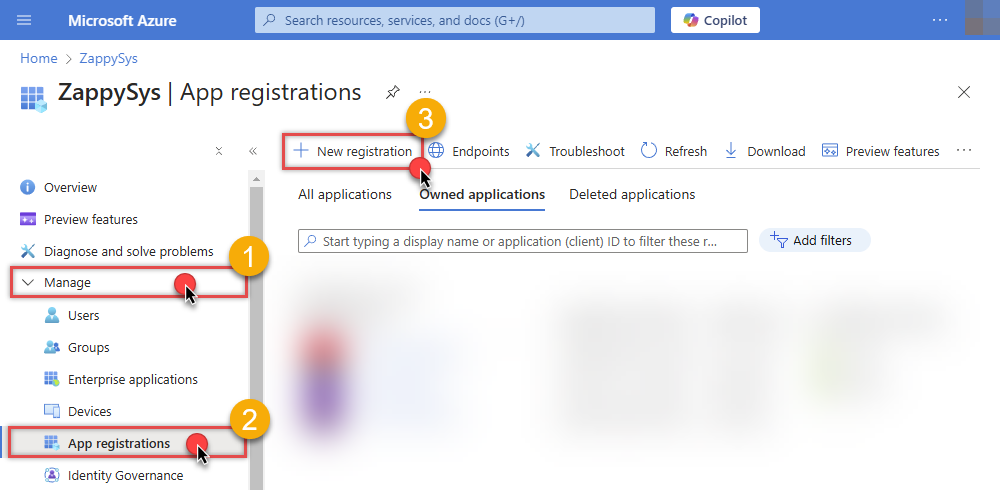
- Navigate to the Azure Portal and log in using your credentials.
- Access Microsoft Entra ID.
-
Register a new application by going to
App registrations
and clicking on New registration button:
 INFO: Find more information on how to register an application in Graph API reference.
INFO: Find more information on how to register an application in Graph API reference. -
When configuration window opens, configure these fields:
-
Supported account type
- e.g. select
Accounts in this organizational directory onlyif you need access to data in your organization only.
- e.g. select
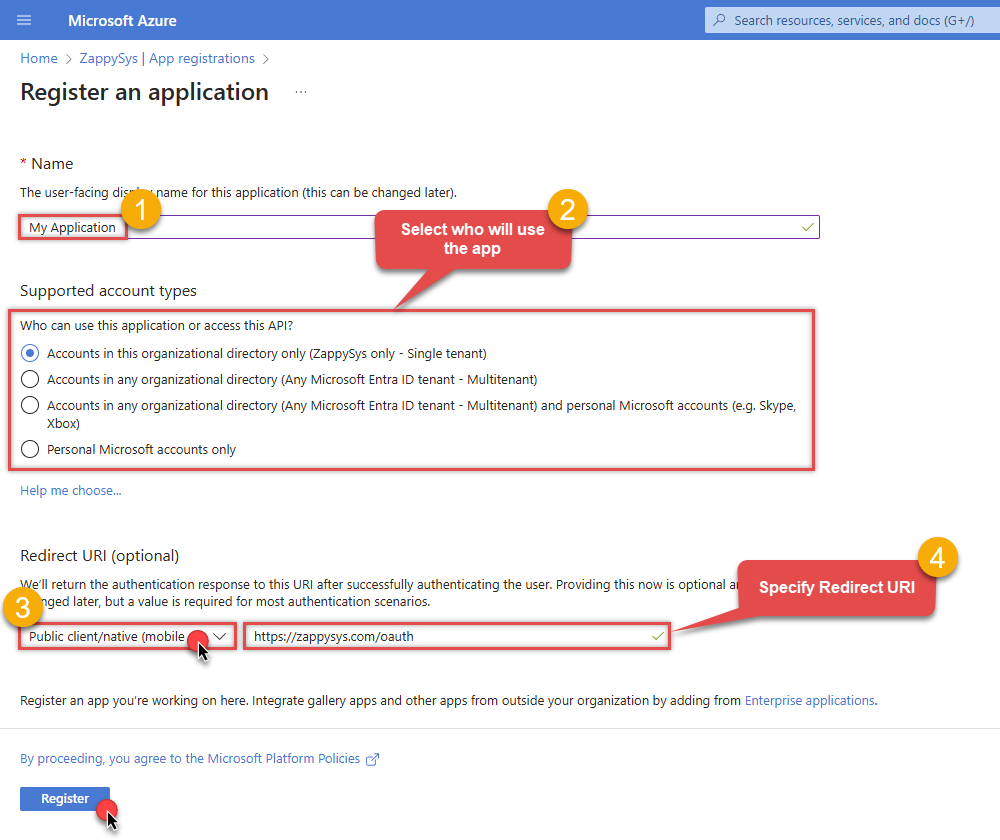
-
Supported account type
-
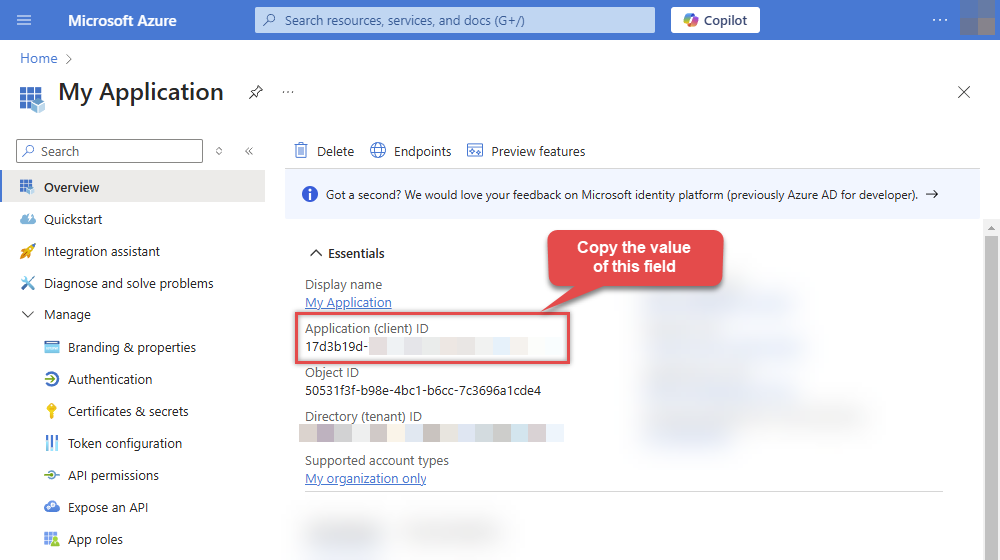
After registering the app, copy the Application (client) ID for later:
-
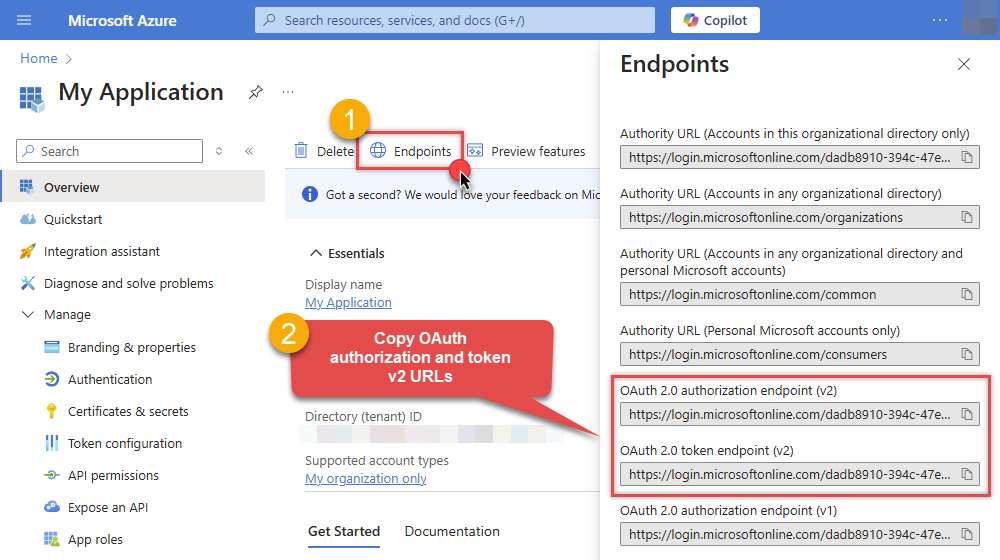
Then copy OAuth authorization endpoint (v2) & OAuth token endpoint (v2) URLs:
Step-2: Configure App Permissions
-
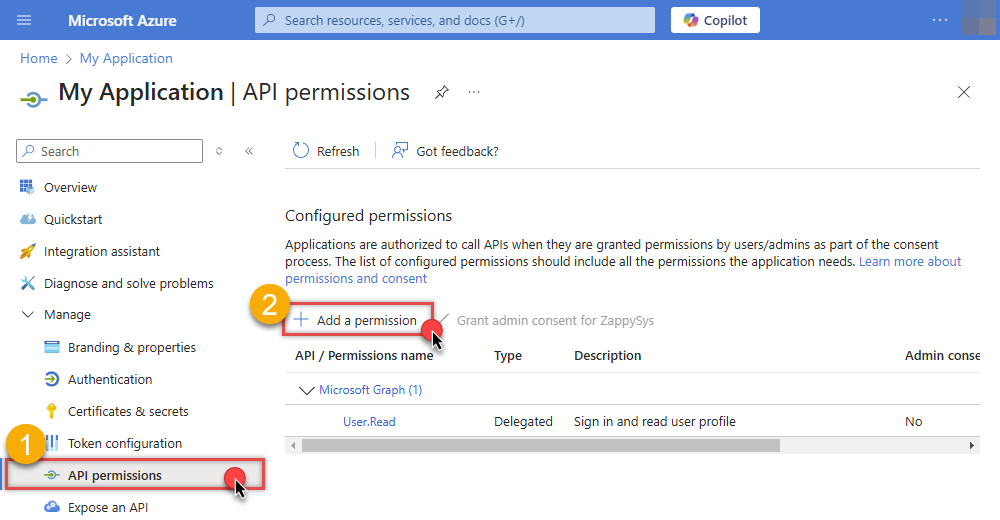
Continue by adding permissions for the app by going to the API permissions section, and clicking on Add a permission:
-
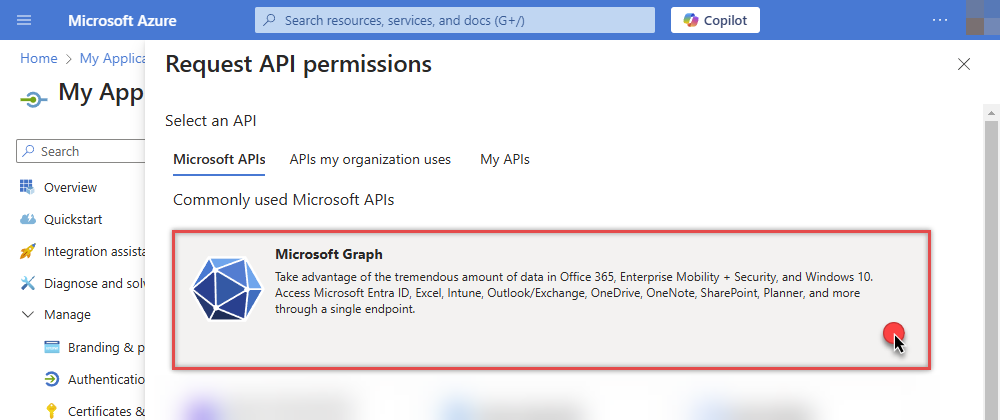
Select Microsoft Graph:
-
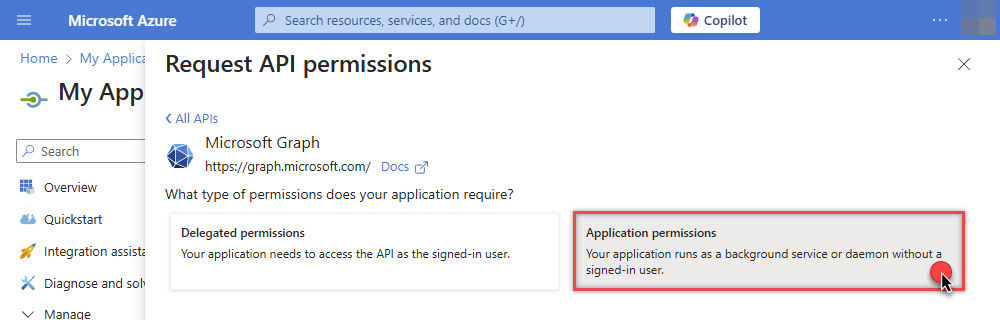
Then choose Application permissions option:
-
Continue by adding these Sites permissions (search for
site):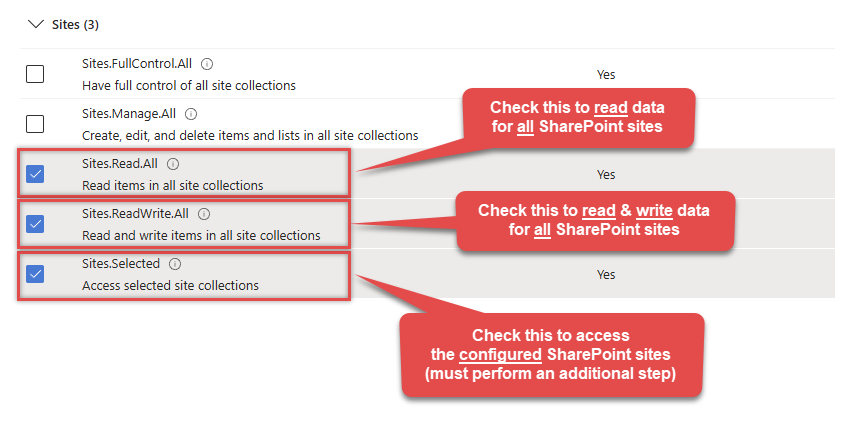 INFO: If you want to access specific lists or list items (table-level vs row-level security) rather than the full site, then add
INFO: If you want to access specific lists or list items (table-level vs row-level security) rather than the full site, then addLists.SelectedOperations.SelectedorListItems.SelectedOperations.Selectedpermissions , just like in the previous step (search forlist).WARNING: If you add any of these permissions -Sites.Selected,Lists.SelectedOperations.Selected, orListItems.SelectedOperations.Selected- you must grant the app the SharePoint permissions for the specific resource (e.g. aSite, aList, or aListItem). Follow instructions in Grant SharePoint permissions to the OAuth app (optional) section on how to accomplish that. -
Finish by clicking Add permissions button:

-
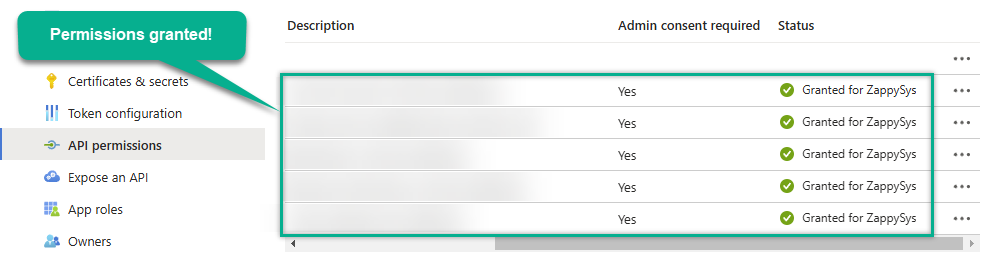
Now it's time to Grant admin consent for your application:
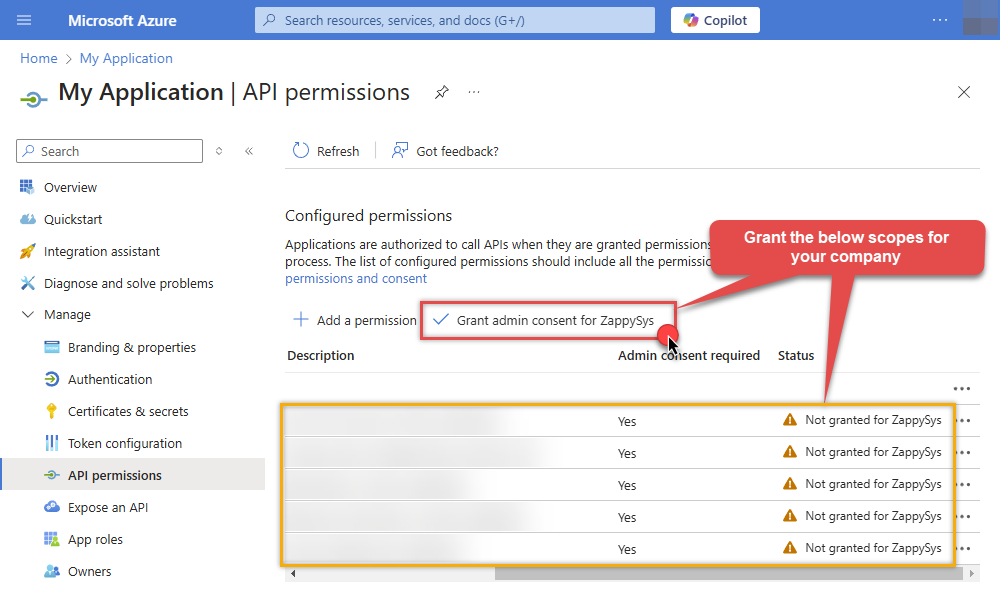
-
Confirm all the permissions are granted:
Step-3: Generate a Self-Signed Certificate
Now let's go through setting up a certificate-based authentication flow for Microsoft Graph or other Azure AD protected APIs using client credentials and a JWT.
You can use OpenSSL or any other way to generate Certificate file but to make it simple we will use below example PowerShell script.
Open PowerShell and execute code listed in below steps.
# Run this in PowerShell #Change .AddYears(1) to desired number. By default it expires certificate in one year as per below code. $cert = New-SelfSignedCertificate ` -Subject "CN=MyClientAppCert" ` -KeySpec Signature ` -KeyExportPolicy Exportable ` -KeyLength 2048 ` -CertStoreLocation "Cert:\CurrentUser\My" ` -KeyAlgorithm RSA ` -HashAlgorithm SHA256 ` -NotAfter (Get-Date).AddYears(1) ` -Provider "Microsoft Enhanced RSA and AES Cryptographic Provider" # Export private key (.pfx) - Keep this with you to make API calls (SECRET KEY - DONOT SHARE) $pfxPath = "$env:USERPROFILE\Desktop\private_key.pfx" $pwd = ConvertTo-SecureString -String "yourStrongPassword123" -Force -AsPlainText Export-PfxCertificate -Cert $cert -FilePath $pfxPath -Password $pwd # Export public certificate (.cer) - UPLOAD this to Azure Portal $cerPath = "$env:USERPROFILE\Desktop\public_key.cer" Export-Certificate -Cert $cert -FilePath $cerPathStep-4: Upload the Certificate (i.e. Public Key *.cer)
Once we have certificate file generated.- In your App Registration, go to Certificates & secrets
- Under Certificates, click Upload certificate
- Select the
.cerfile (public certificate)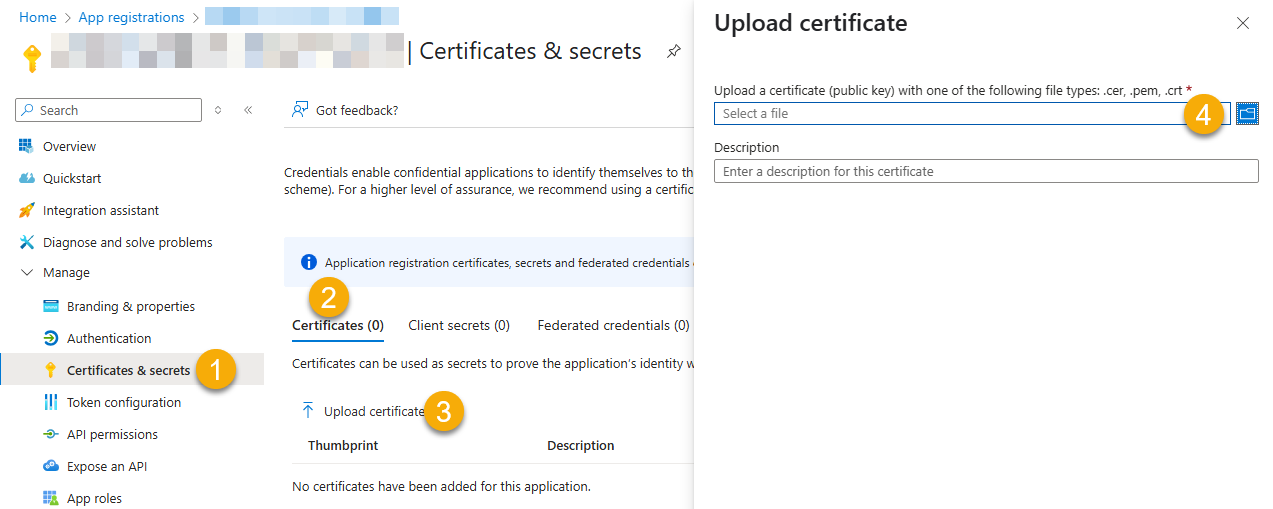
- Click Select a file (Browse button)
- Select public key file (*.cer) from local machine and click OK to upload
Step-5: Configure ZappySys Connection - Use private key (i.e. *.pfx or *.pem)
Now its time to use certificate pfx file (private key) generated in the previous step (NOTE: PFX file contains both private key and public key).-
Go to SSIS package or ODBC data source and use the copied values in Application Credentials authentication configuration:
- In the Token URL field paste the OAuth token endpoint (v2) URL value you copied in the previous step.
- In the Client ID field paste the Application (client) ID value you copied in the previous step.
- Configure private key
- go to
Certificate Tab - Change Storage Mode to
Disk File: *.pfx format (PKCS#12).NOTE: You can also useStored In LocalMachinemode if PFX file already imported in the Local Certificate Storage Area - User Store OR Machine Store. If you used OpenSSL to generate key pair then useDisk File: *.pem format (PKCS#8 or PKCS#1)Mode for Cert Store Location. - Supply the key file path
- Supply the certificate password (same password used in earlier PowerShell script)
- go to
- Now go back to General Tab, choose Default Site Id and Default Drive Id from the drop down menu.
- Click Test connection see everything is good
Step-6 (optional): Grant granular permissions to the OAuth app
If you used
Sites.Selected,Lists.SelectedOperations.SelectedorListItems.SelectedOperations.Selectedpermission in the previous section, you must grant the app the SharePoint permissions for the specific resource (e.g. aSite, aList, or aListItem). You can do it using PowerShell or SharePoint admin center (obsolete method).Granting SharePoint permissions using PowerShell
Unfortunately, there is no user interface available to control these permissions yet. For now, granting permissions has to be accomplished via Microsoft Graph API [Microsoft reference]:
You must be the owner of the resource to grant permissions (i.e. belong to SharePoint owners group or be the owner of theSiteorList).- Open PowerShell (run as admin).
-
Call the following PowerShell code to grant
readandwritepermission for the app we created earlier (assuming Application (client) ID is89ea5c94-aaaa-bbbb-cccc-3fa95f62b66e):##### CONFIGURATION ############################################################################################ # More info at: # - https://learn.microsoft.com/en-us/graph/permissions-selected-overview?tabs=powershell # - https://learn.microsoft.com/en-us/powershell/module/microsoft.graph.sites/?view=graph-powershell-1.0 # Find SharePoint Site Id by following these steps: # - Login into SharePoint Online # - Open this URL https://{your-company}.sharepoint.com/_api/site in the browser # NOTE: For a subsite use https://{your-company}.sharepoint.com/sites/{your-subsite}/_api/site # - Find 'Id' element in the response (e.g. <d:Id m:type="Edm.Guid">efcdd21a-aaaa-bbbb-cccc-5d8104d8b5e3</d:Id>) # - Copy the Site Id, i.e.: efcdd21a-aaaa-bbbb-cccc-5d8104d8b5e3 # Set $siteId variable to the retrieved Site Id: $siteId="efcdd21a-aaaa-bbbb-cccc-5d8104d8b5e3" # Find your Application Id (i.e. Client Id) in the Azure Portal, in App Registrations page: # https://portal.azure.com/#view/Microsoft_AAD_RegisteredApps/ApplicationsListBlade $applicationId="89ea5c94-aaaa-bbbb-cccc-3fa95f62b66e" # Set one of app permissions: read, write, fullcontrol, owner ('write' includes 'read' permission) $appPermission="write" ##### SCRIPT ################################################################################################### # Step-1: Install 'Microsoft.Graph.Sites' module if it's not installed if (-not (Get-Module Microsoft.Graph.Sites -ListAvailable)) { Install-Module Microsoft.Graph.Sites } # Step-2: Load module Import-Module Microsoft.Graph.Sites # Step-3: Login (use Azure admin or SharePoint owner account) DisConnect-MgGraph Connect-MgGraph # Step-4: Set parameters for API call (set permissions, Site ID and Application ID) $params = @{ roles = @($appPermission) grantedTo = @{ application = @{id = $applicationId} } } # Step-5: Grant permissions New-MgSitePermission -SiteId $siteId -BodyParameter $params # Done! Write-Host "Granted SharePoint permissions to application '$applicationId' for site '$siteId'." - That's it! Now you can use the connector.
Parameters
Parameter Required Default value Options Name: TokenUrl Label: Token URL
YES Name Value For Single Tenant https://login.microsoftonline.com/{ENTER-TENANT-ID-HERE}/oauth2/v2.0/token For Multi Tenant https://login.microsoftonline.com/common/oauth2/v2.0/token Name: ClientId Label: Client ID
YES Name: Certificate Label: Certificate: *** Configure [Client Certificate] Tab ***
YES Name: SiteId Label: Default Site Id
Specify a siteYES rootName: DriveId Label: Default Drive Id
Specify a default Drive Id you like to use for operations.Name: RetryMode Label: RetryMode
RetryWhenStatusCodeMatchName Value None None RetryAny RetryAny RetryWhenStatusCodeMatch RetryWhenStatusCodeMatch Name: RetryStatusCodeList Label: RetryStatusCodeList
429 is API limit reached, 423 is File locked429|503|423Name: RetryCountMax Label: RetryCountMax
5Name: RetryMultiplyWaitTime Label: RetryMultiplyWaitTime
TrueName: SearchOptionForNonIndexedFields Label: Search Option For Non-Indexed Fields (Default=Blank - Search Only Indexed)
If you wish to do certain operations e.g. search / order by on non-indexed fields then you have to set this option to HonorNonIndexedQueriesWarningMayFailRandomly. By default filter / orderby on non-indexed fields not allowed.Name Value Search Only Indexed Search Both Indexed and Non-Indexed HonorNonIndexedQueriesWarningMayFailRandomly Name: ExtraHeaders Label: Extra Headers (e.g. Header1:AAA||Header2:BBB)
Name Value MyHeader1:AAA MyHeader1:AAA MyHeader1:AAA||MyHeader2:BBB MyHeader1:AAA||MyHeader2:BBB Name: IsAppCred Label: IsAppCred
For internal use only1
