Authentication Application Credentials
Description
Application-only access is broader and more powerful than delegated access (User Credentials), so you should only use app-only access where needed. Use it when: 1. The application needs to run in an automated way, without user input (for example, a daily script that checks emails from certain contacts and sends automated responses). 2. The application needs to access resources belonging to multiple different users (for example, a backup or data loss prevention app might need to retrieve messages from many different chat channels, each with different participants). 3. You find yourself tempted to store credentials locally and allow the app to sign in 'as' the user or admin. [API reference]
Instructions
Follow these simple steps below to create Microsoft Entra ID application with application access permissions. Using following steps, you can grant very granular app permissions to access File(s). Choose permission based on your need.
Create OAuth app
- Navigate to the Azure Portal and log in using your credentials.
- Access Microsoft Entra ID.
-
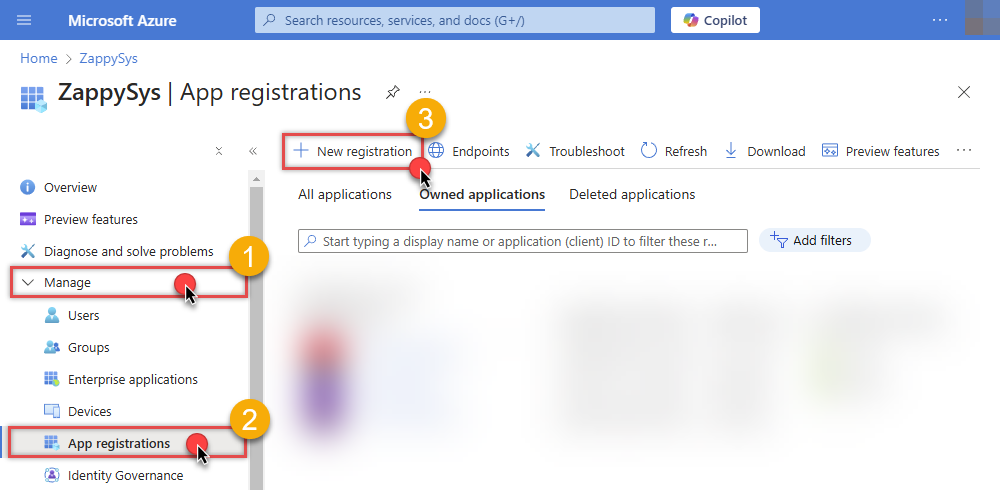
Register a new application by going to
App registrations
and clicking on New registration button:
 INFO: Find more information on how to register an application in Graph API reference.
INFO: Find more information on how to register an application in Graph API reference. -
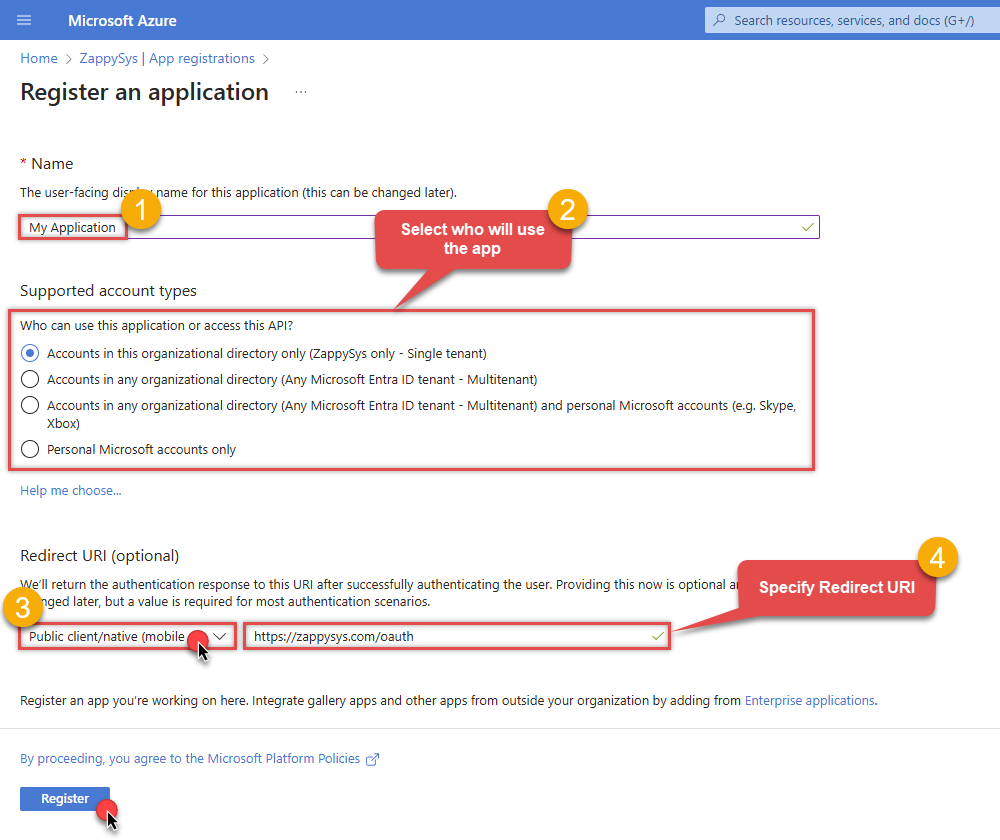
When configuration window opens, configure these fields:
-
Supported account type
- e.g. select
Accounts in this organizational directory onlyif you need access to data in your organization only.
- e.g. select
-
Supported account type
-
Redirect URI:
- Set the type to
Public client/native (mobile & desktop). - Leave the URL field empty.
- Set the type to
-
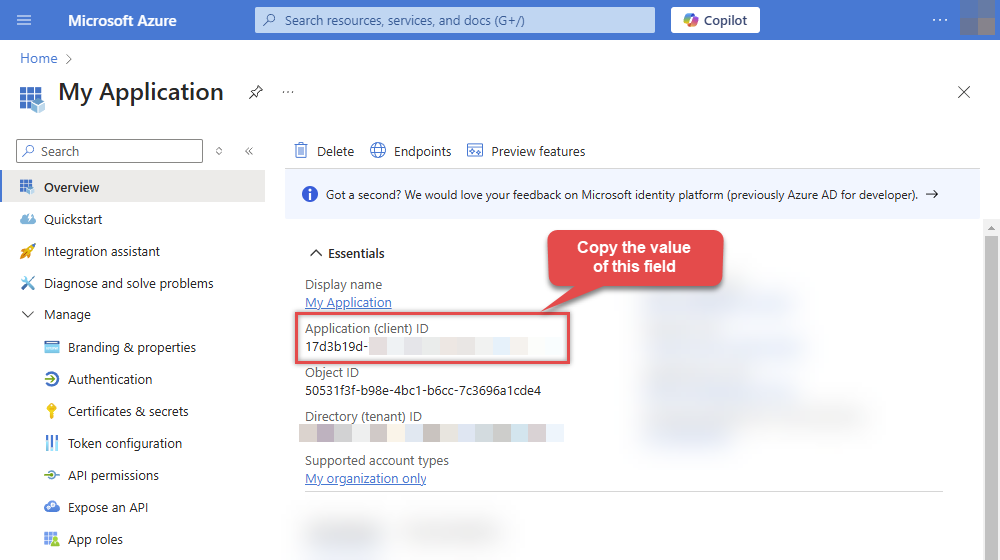
After registering the app, copy the Application (client) ID for later:
-
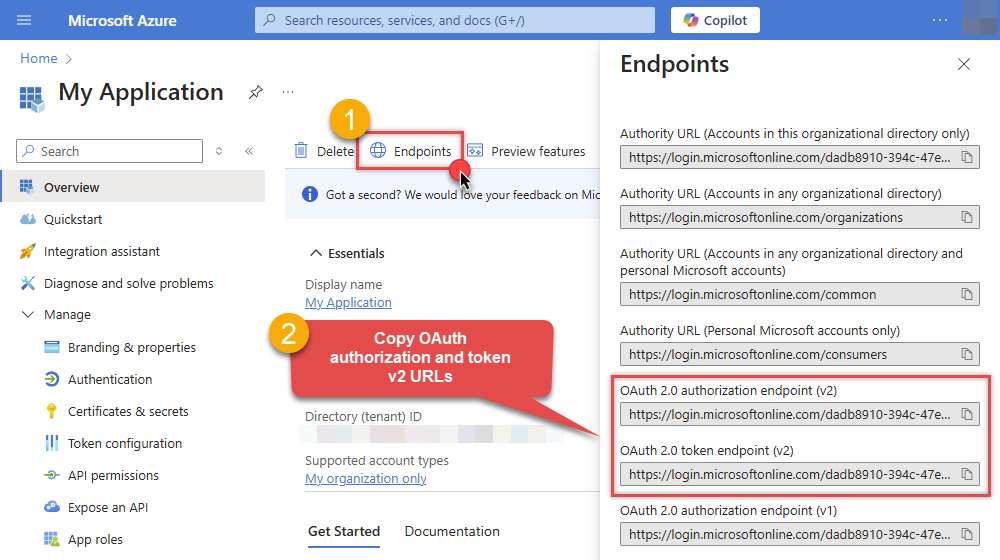
Then copy OAuth authorization endpoint (v2) & OAuth token endpoint (v2) URLs:
-
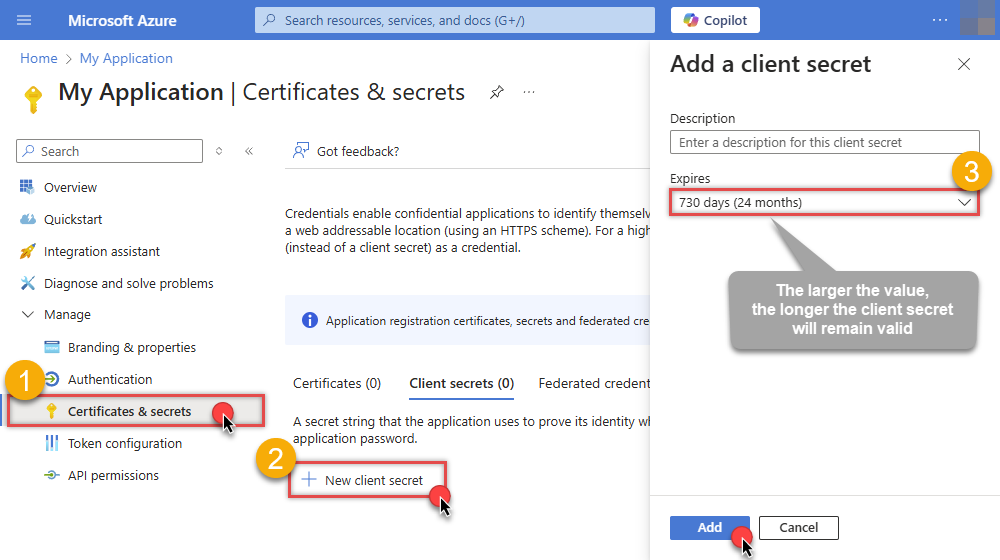
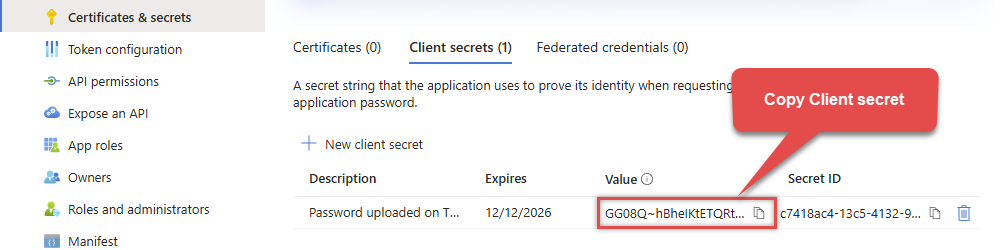
Continue and create Client secret:
-
Then copy the Client secret for later steps:
-
Continue by adding permissions for the app by going to the API permissions section, and clicking on Add a permission:
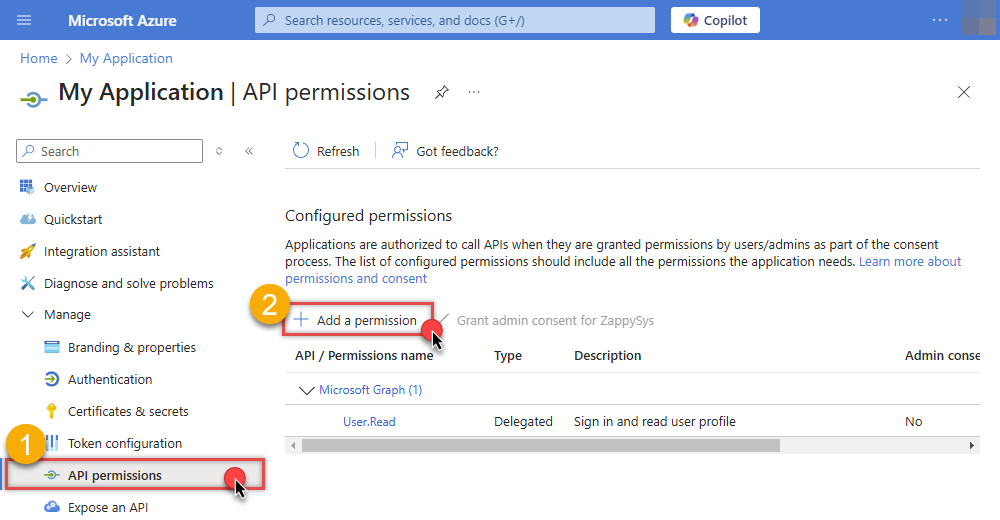
-
Select Microsoft Graph:
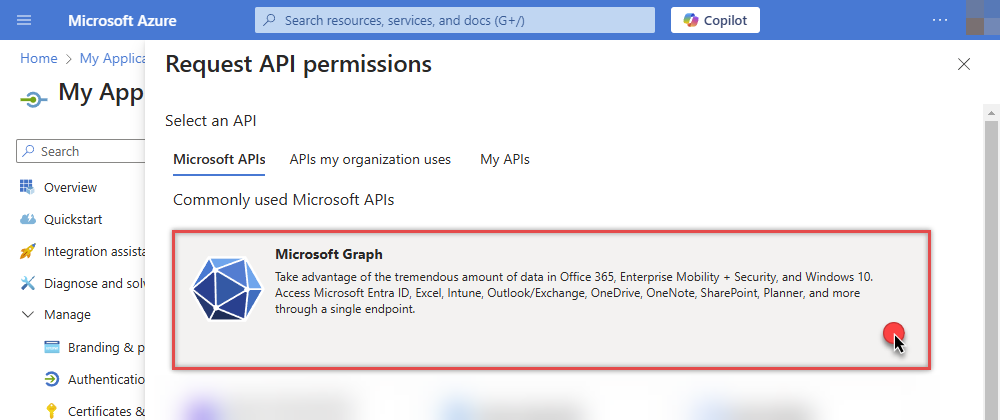
-
Then choose Application permissions option:
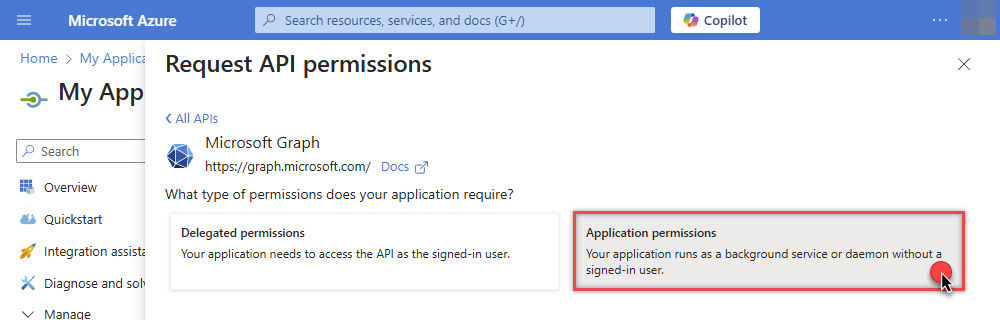
-
Continue by adding these Files (OneDrive) permissions (Just search for "Files" and then select desired permissions):
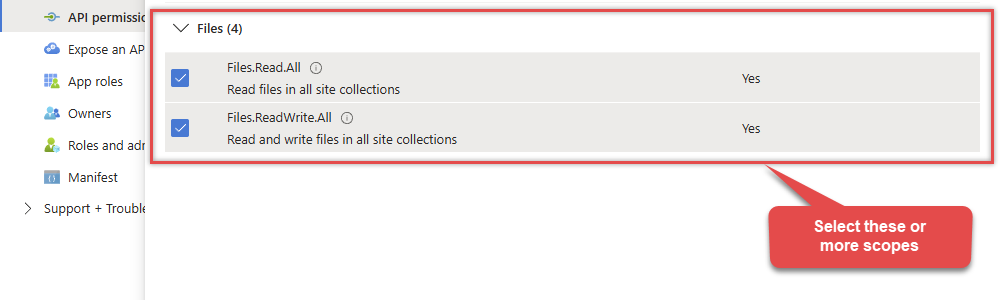
-
Finish by clicking Add permissions button:

-
Now it's time to Grant admin consent for your application:
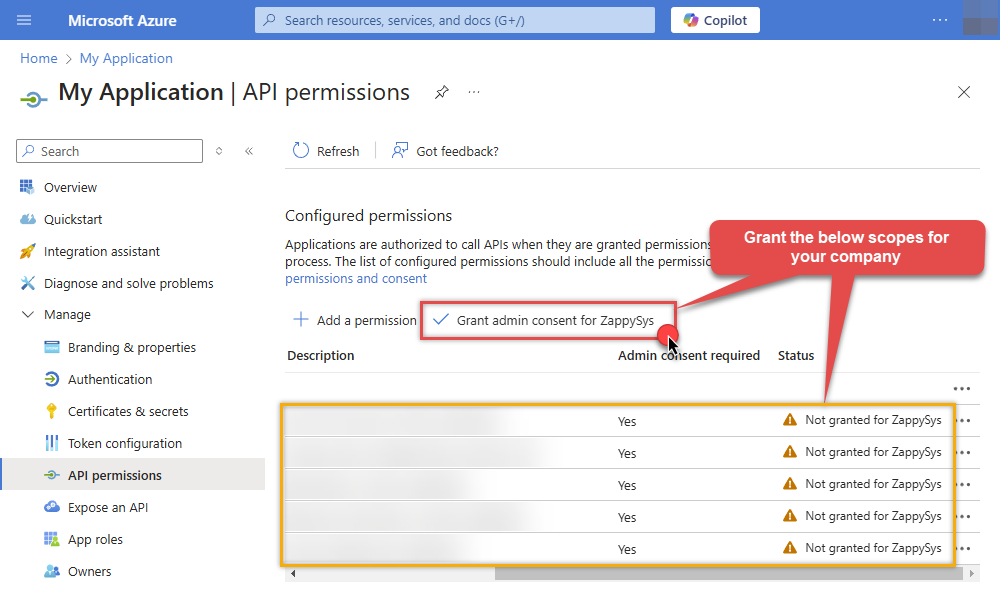
-
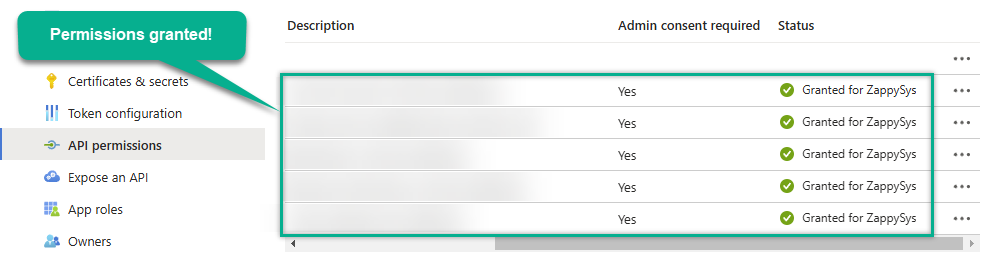
Confirm all the permissions are granted:
-
Now go to SSIS package or ODBC data source and use the copied values in Application Credentials authentication configuration:
- In the Token URL field paste the OAuth token endpoint (v2) URL value you copied in the previous step.
- In the Client ID field paste the Application (client) ID value you copied in the previous step.
- In the Client Secret field paste the Client secret value you copied in the previous step.
- Optional step. Choose Default Drive Id from the drop down menu.
- Click Test Connection to confirm the connection is working.
Parameters
| Parameter | Required | Default value | Options | ||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|
|
Name:
Label: Token URL |
YES |
|
|||||||||
|
Name:
Label: Client ID |
YES | ||||||||||
|
Name:
Label: Client Secret |
YES | ||||||||||
|
Name:
Label: Default Group or User Id (additional Scopes needed to list - If fails enter manually) To list all users and groups from your organizations you need additional scopes. See connection UI - Choose User.Read.All and Group.Read.All Scopes and regenerate token. You can manually type value too if you know Group or User Id. Format is /users/{id} OR /groups/{id} |
YES |
|
|||||||||
|
Name:
Label: Default Drive Id |
YES | ||||||||||
|
Name:
Label: Scope Permissions you want to use. |
https://graph.microsoft.com/.default
|
||||||||||
|
Name:
Label: RetryMode |
RetryWhenStatusCodeMatch
|
|
|||||||||
|
Name:
Label: RetryStatusCodeList 429 is API limit reached, 423 is File locked |
429|503|423
|
||||||||||
|
Name:
Label: RetryCountMax |
5
|
||||||||||
|
Name:
Label: RetryMultiplyWaitTime |
True
|
||||||||||
|
Name:
Label: Search Option For Non-Indexed Fields (Default=Blank - Search Only Indexed) If you wish to do certain operations e.g. search / order by on non-indexed fields then you have to set this option to HonorNonIndexedQueriesWarningMayFailRandomly. By default filter / orderby on non-indexed fields not allowed. |
|
||||||||||
|
Name:
Label: Extra Headers (e.g. Header1:AAA||Header2:BBB) |
|
||||||||||
|
Name:
Label: IsAppCred For internal use only |
1
|
